Cloud LDAP
Connect your users to their on-premises resources from anywhere, with no hardware requirements.
Complete LDAP Functionality, No Traditional Setup
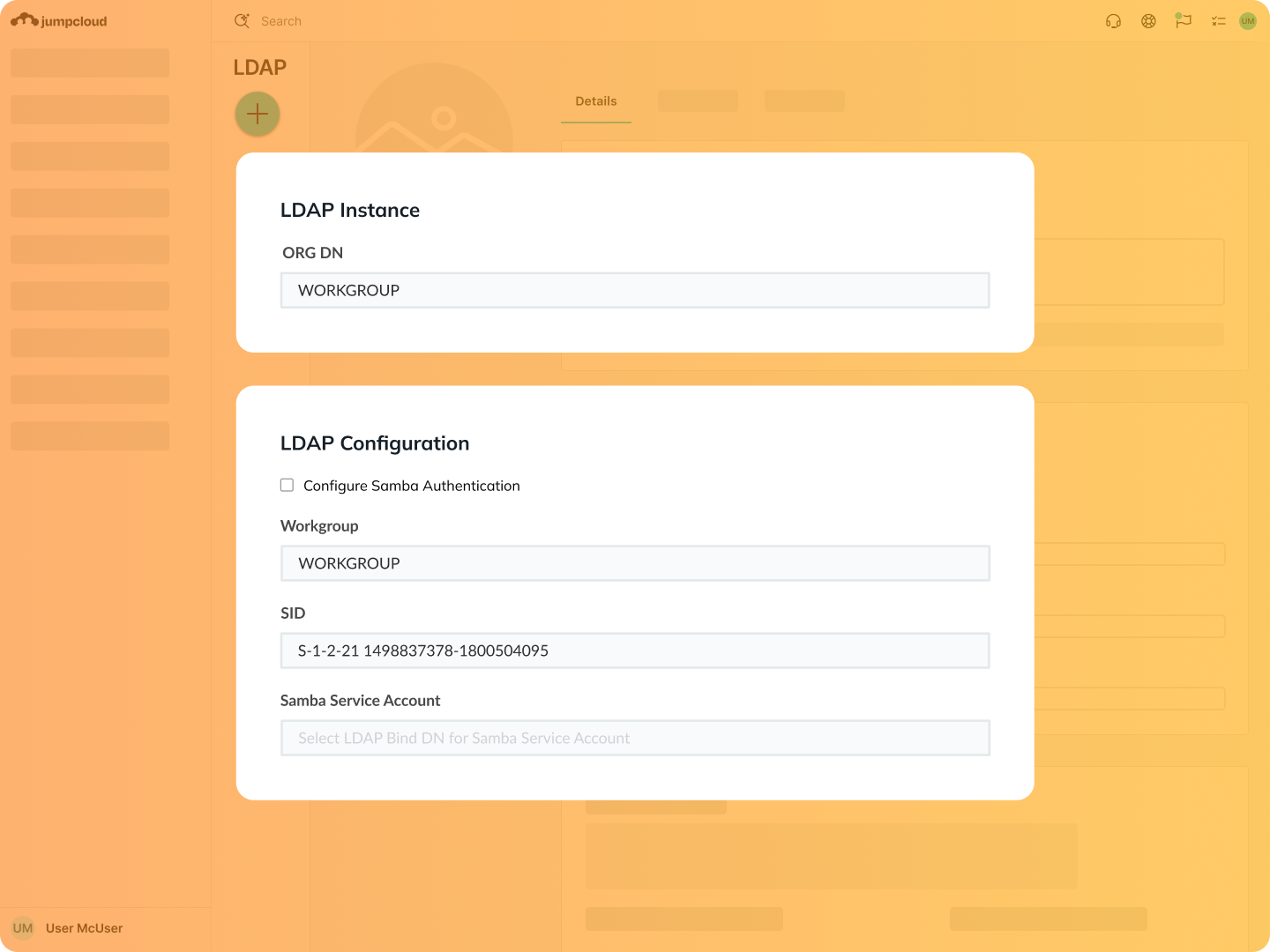
In the past, LDAP implementations required a significant amount of setup, patching and maintenance, failover requirements, and on-premises hardware. JumpCloud’s Cloud LDAP servers are self-supported and maintained, so all you need to do to take full advantage is point your LDAP-connected endpoints to JumpCloud.
Complete Access Control
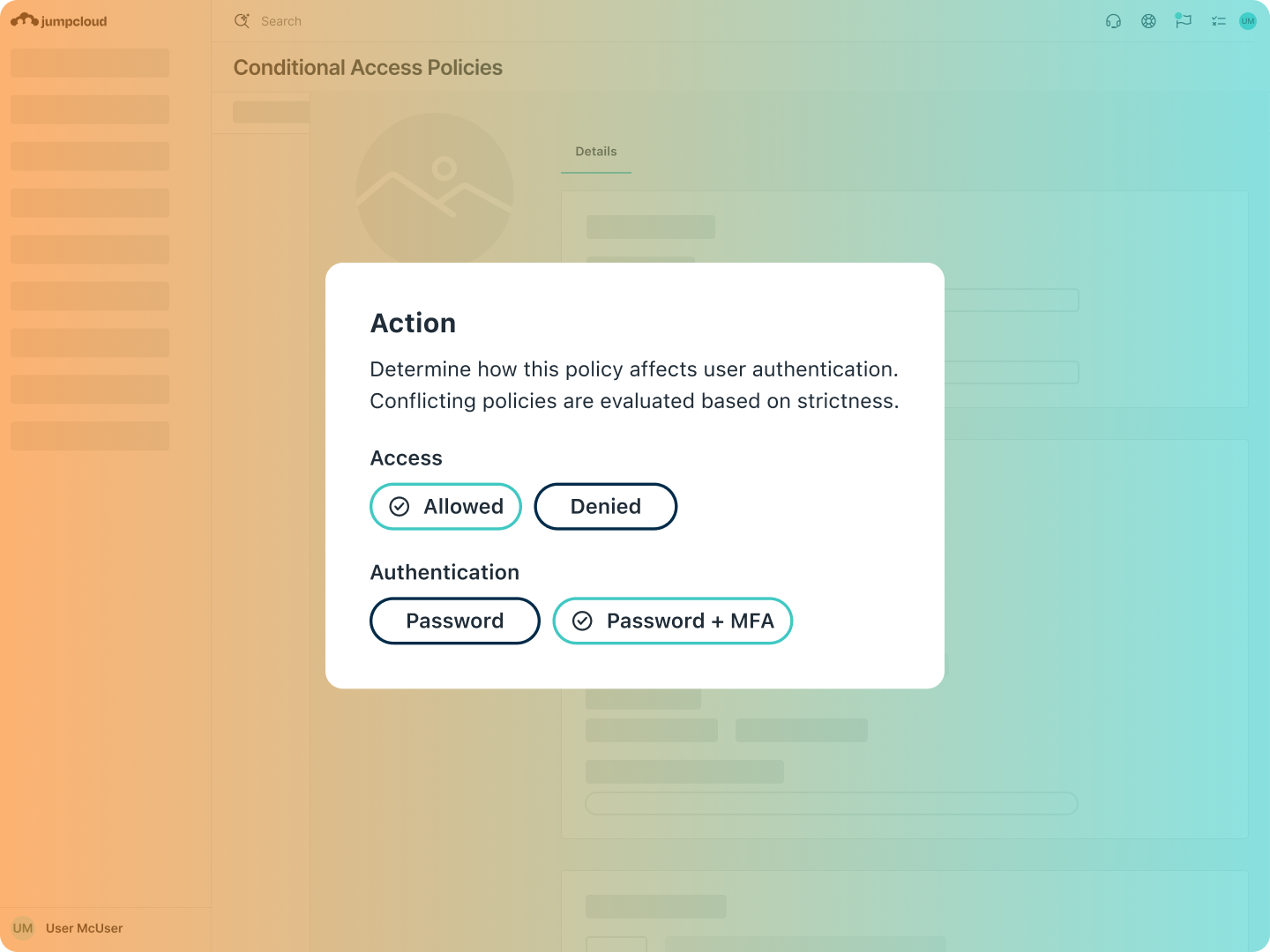
Distributing and managing access to on-prem systems can add undue overhead challenges and create gaps in security if not done right. Through group-based access controls, you can streamline LDAP management to best suit your needs, whether from your browser through the JumpCloud Admin Portal, via the command line, or through RESTful APIs.
Video Tutorial
| Configuring LDAPSupport Article
| Configure MFA for LDAPSupport Article
| JumpCloud APIs
Hyper Secure and Compliant
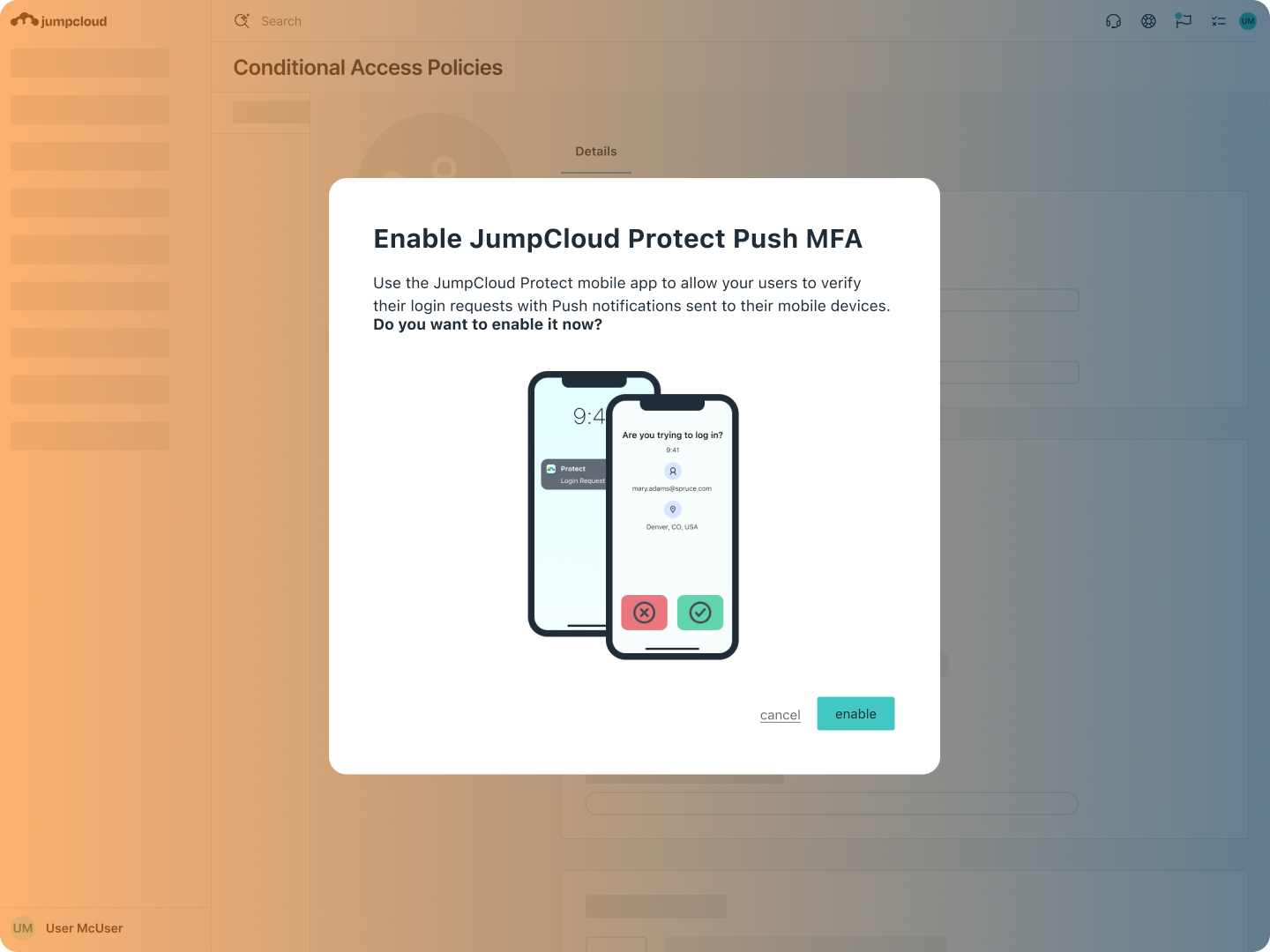
Our OpenLDAP RFC 2307-compliant Cloud LDAP offering is encrypted by LDAPS and Start TLS, ensuring your LDAP authentication remains as secure as possible. What’s more, you can require multi-factor authentication (MFA) upon entry to LDAP resources to further secure access.
Support Article
| Using Cloud LDAPSupport Article
| Create an LDAP GroupCourse
| Advanced LDAP
Wide- Ranging Authentication
JumpCloud provides authentication mechanisms, including MFA, for any application or service that can defer authentication via LDAP. Integrate with apps such as Atlassian Jira and Confluence or with DevOps infrastructure such as Jenkins, Ansible, Kubernetes, Docker, OpenVPN, and thousands of others.
Case Study
| Cabify Case Study: Agile Directory for BusinessSupport Article
| Configuring OpenVPN to use Cloud LDAPBlog Post
| Choosing the Right LDAP Server
Explore JumpCloud Open Directory Platform Capabilities
Identity Management
Access Management
Device Management







