SaaS and AI Discovery
Uncover every SaaS and AI tool across your fleet, from browsers to the desktop, to eliminate blind spots and move from reactive cleanup to proactive, intelligent control.
See What You’ve Been Missing
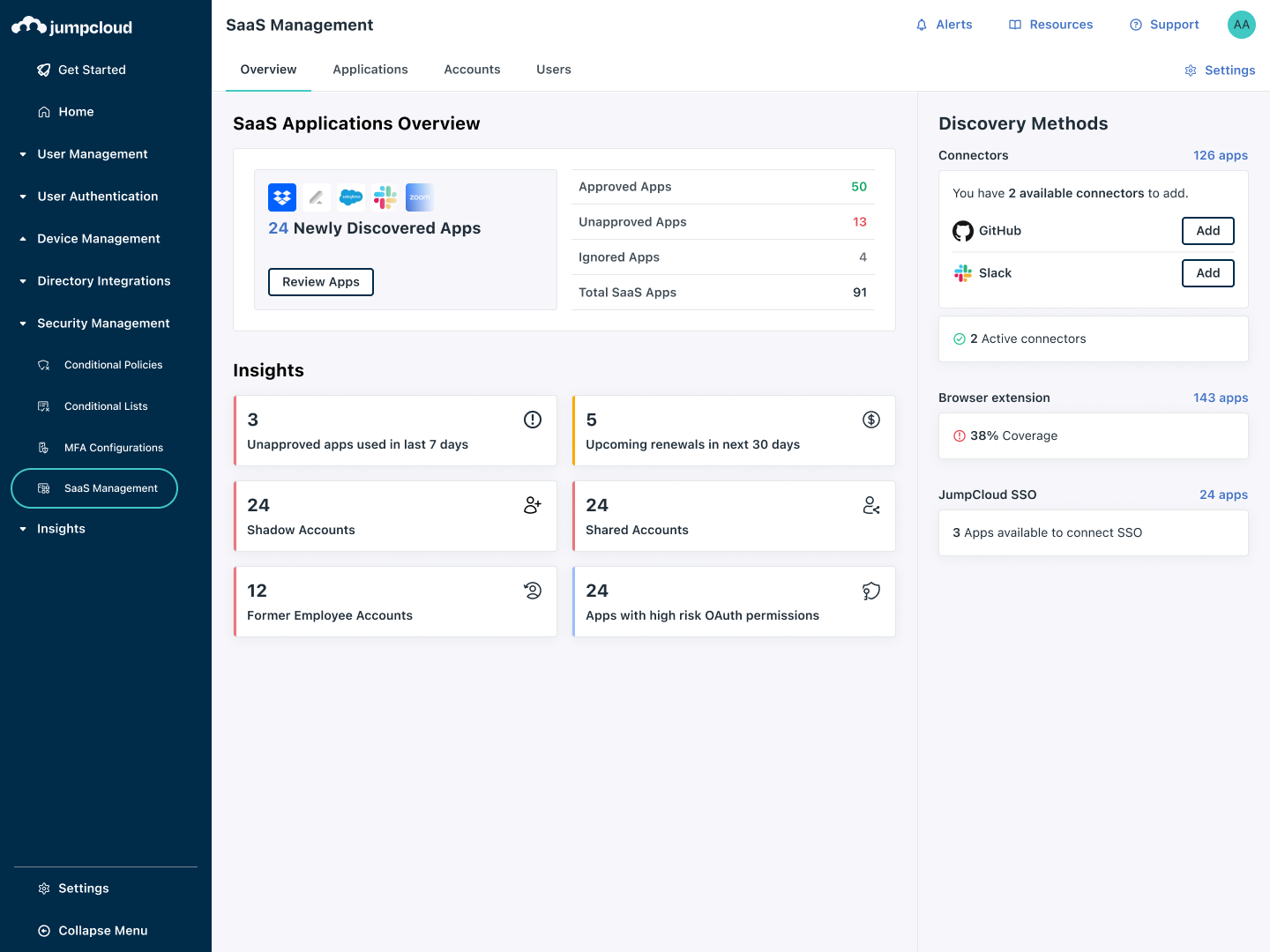
SaaS and AI adoption moves fast, and shadow IT moves with it. JumpCloud surfaces every application across browsers and managed devices, mapping them back to the identities behind them. IT gets a single, living view of every tool in use across the workforce: who’s using what, how often, how secure, and what it’s costing. The visibility to support safe adoption, and the control to stay secure.
Eliminate Shadow IT
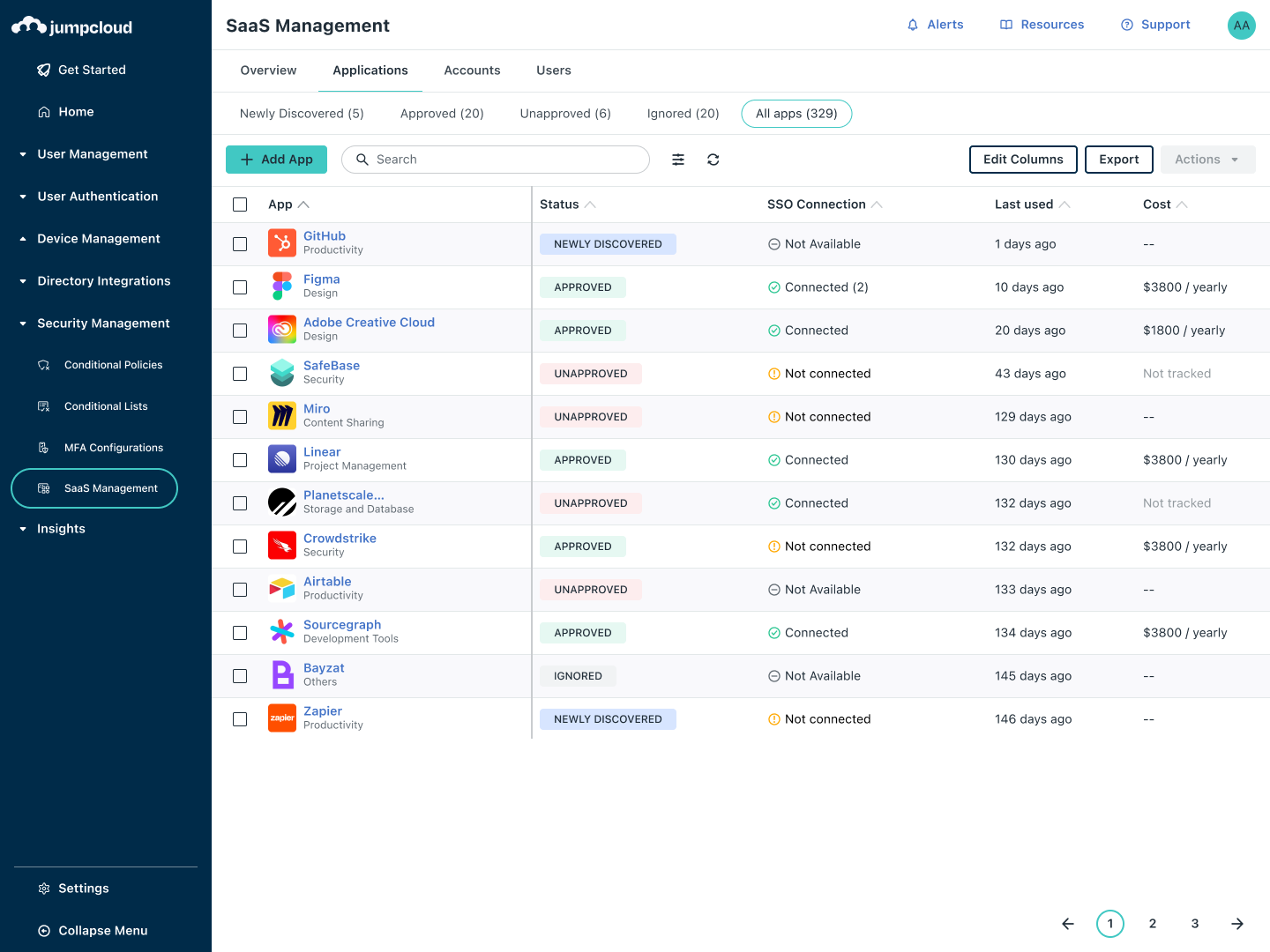
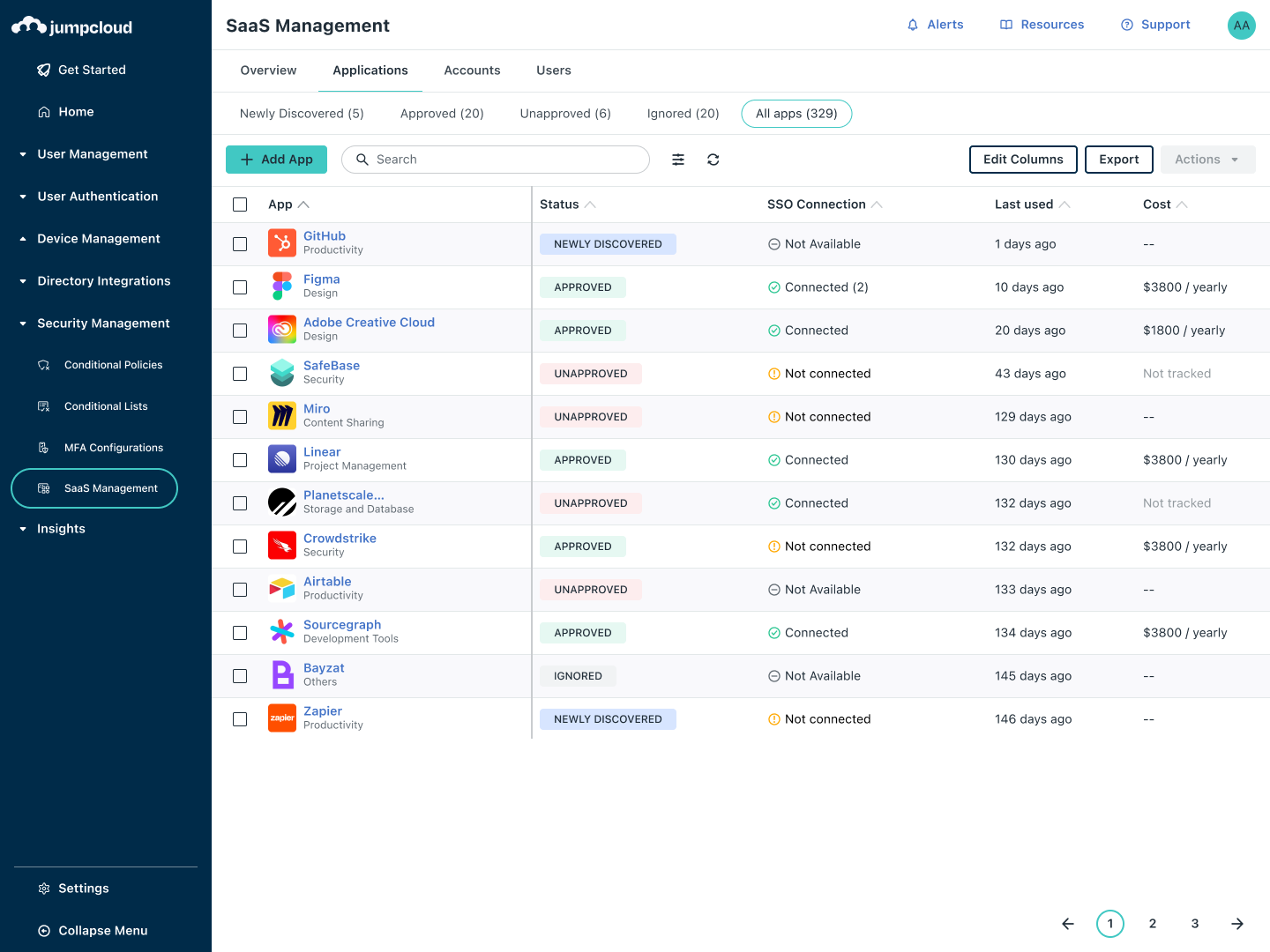
Identify every SaaS and AI tool in use across browsers and managed devices with multiple discovery methods. Prevent unauthorized usage with warnings and blocks on unapproved apps, ensuring compliance and securing employee-led adoption across your organization.
Blog Post
| Bring Shadow IT to Light with JumpCloud SaaS ManagementeBook
| SaaS Management: A New Pillar Is ForgedBlog Post
| SaaS Discovery Methods: IT Admin’s Guide

Save Time and Money
Consolidate all your SaaS apps in a categorized and up-to-date SaaS inventory. Shed light on usage frequency, track licenses, and identify redundant or unused apps to streamline operations and maximize cost efficiency.
eBook
| Casting IT into the ShadowsSupport Article
| Get Started: SaaS ManagementBlog Post
| What is SaaS Sprawl? How to Manage It
Mitigate Security Risks
Gain total visibility into SaaS usage, from OAuth permissions to login methods and SSO-connected apps. Spot overly permissive scopes and unauthorized access to prevent security risks, empowering you to protect your data without disrupting productivity.
Webinar
| Overcoming Shadow IT: Why It Happens and How to Prevent ItSupport Article
| Configure SaaS ManagementBlog Post
| SaaS Procurement: Best Practices & Common Mistakes
Explore Our SaaS Discovery Guided Simulation
Please rotate device
This interactive demo is best viewed in landscape mode.
Explore JumpCloud Open Directory Platform Capabilities
Identity Management
Access Management
Device Management








