JumpCloud’s AI Gateway secures autonomous AI workflows by centralizing visibility, monitoring behavior, and enforcing least-privilege access for AI clients and agents connecting to your enterprise applications.
As organizations integrate AI into their daily operations, IT admins need control over non-human identities like AI agents. Traditional API keys and service accounts only execute explicit commands. However, AI agents are autonomous. They process unstructured data, orchestrate complex workflows, and act on behalf of your users. Without centralized management, organizations risk exposing sensitive data through over-privileged access and unmonitored actions. You need to know exactly which agents are running, what tools they can access, and what they're doing.
The AI Gateway solves this by acting as a centralized MCP control plane, securing the connection between your AI clients and enterprise applications. This allows you to govern AI activity from a single JumpCloud platform, ensuring you always know who accessed your data and when.
- The AI Gateway is not an SSO login method for your AI clients. While SAML SSO controls who can log in to an AI client like ChatGPT, the AI Gateway controls and audits what enterprise data the AI client can access.
- The AI Gateway acts exclusively as a secure authentication and routing layer. It does not process, alter, or influence the responses generated by your AI clients.
- This feature is in Public Preview and is currently available only in the US data center region. See JumpCloud Data Centers to learn more.
Core Concepts and Terminology
Before configuring the AI Gateway, familiarize yourself with the standard terminology used to describe AI integrations:
- Model Context Protocol (MCP): An open standard that enables AI applications to securely connect to external data sources.
- Enterprise Application: The 3rd party software or platform that holds organization data.
- MCP Server: A backend program that offers an enterprise application’s data and actions to AI clients using the MCP standard. Note: JumpCloud can also act as an MCP server, allowing external clients to query JumpCloud directory data. The AI Gateway acts as a control plane for your other enterprise MCP servers.
- Admins register and manage these servers in the JumpCloud Admin Portal under Access > AI Gateway.
- AI Client: An AI-powered application, most commonly a large language model (LLM) like ChatGPT or integrated development environment (IDE) like Cursor that users interact with to access information from MCP servers.
- Users configure their specific AI client to connect to JumpCloud's AI Gateway endpoint.
- AI Agent: Software that uses AI to carry out tasks for you by interacting with tools and APIs autonomously.
- MCP Resources and Tools: Specific functions exposed by an MCP server that the AI client can use. Resources are "read-only" data that the AI can view, and tools are executable actions that the AI can perform. For example, these might be the ability to view a document or search for objects in the enterprise application.
See What is an MCP Server for a deeper dive into how this architecture functions.
Key Features and Benefits
- Central AI Access Control: Register your enterprise MCP servers in one location and determine whether users authenticate to them via OAuth or API tokens.
- Secure Routing: The gateway automatically routes AI tool calls to the correct MCP servers.
- Behavior Monitoring and Auditing: Track, analyze, and audit requests. Tool call activity is published as Directory Insights (DI) events.
Considerations:
- AI Gateway doesn’t currently support MCP servers that require client secrets.
Understanding the Authentication Flow
The AI Gateway uses a secure redirect flow to ensure users only access the MCP servers you have explicitly configured for them in JumpCloud.
- A user configures their AI client (for example, Cursor) using the JumpCloud AI Gateway MCP URL: https://ai.jumpcloud.com/mcp.
- When the user attempts to use the AI client, they are redirected to a JumpCloud authorization page.
- The AI Gateway presents a list of all MCP servers the administrator has configured.
- The user authenticates to each application via OAuth or by entering a specific API key, depending on the admin configuration.
- During an active session, the gateway routes the requests to the selected MCP server and returns the results to the AI client.
Choosing an Authentication Method
When connecting external applications to the AI Gateway, the authentication methods available depend on how the application provider designed their MCP server. Some applications support OAuth, some require API Tokens, and some offer both.
If an application supports both methods, JumpCloud generally recommends configuring the server using OAuth.
- OAuth (Recommended): OAuth provides the most seamless and secure experience. As an administrator, you configure a single OAuth application in the provider’s console. When users connect their AI clients, they simply click a button to securely log in via the application’s standard authentication screen. They do not need to handle, store, or rotate any credentials.
- API Token: API Token authentication requires every user to manually generate an API key directly within the application’s platform (for example, in their Slack or Atlassian account settings) and paste it into the JumpCloud authorization page. While JumpCloud securely passes this token, this method introduces more friction for the user and relies on them to correctly generate the key with the right scopes.
Always review the application’s MCP documentation to determine which authentication method their server requires before configuring it in JumpCloud.
Configuring the AI Gateway
Adding MCP Servers
To begin securing your AI workflows, you must register your enterprise applications as MCP servers in the Admin Portal. Because each application has specific prerequisite configurations, you must review the application’s setup guide before adding the server to JumpCloud.
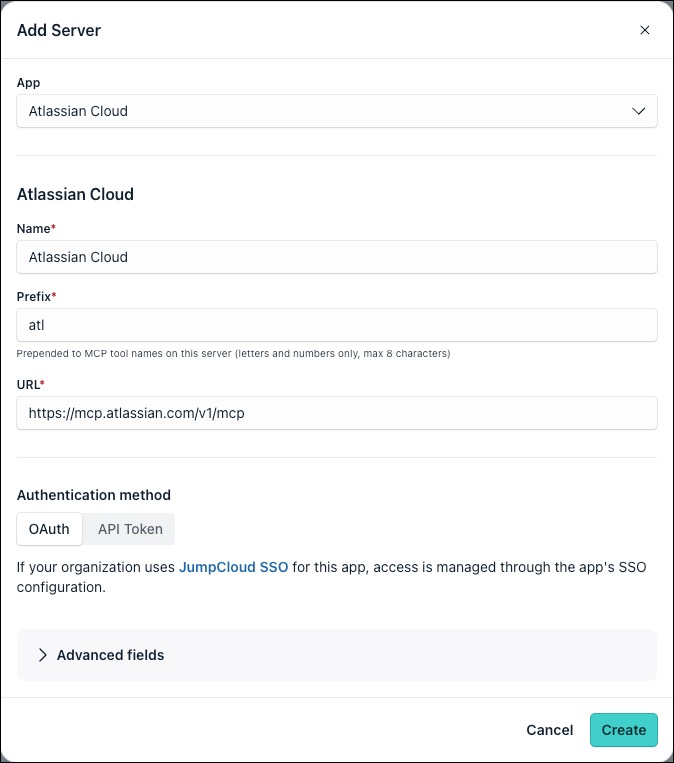
To add an MCP server:
- Review Supported AI Gateway Integrations for a list of supported MCP server integrations and specific instructions for each.
- Log in to the JumpCloud Admin Portal.
- Go to Access > AI Gateway.
- Select the Servers tab.
- Click + Add Server.
- Under App, select from the list of configured SSO apps within your org, or create a Custom App.
- Follow the instructions in the application’s setup guide to complete the required JumpCloud configurations for that specific integration, such as the Authentication method, Client ID, and Scope).
When configuring an MCP server with OAuth authentication, if the server requires the Client ID to be specified, use the service managed client_id, not the corresponding JumpCloud SSO app’s client_id. Some enterprise applications require specific configurations to generate this.
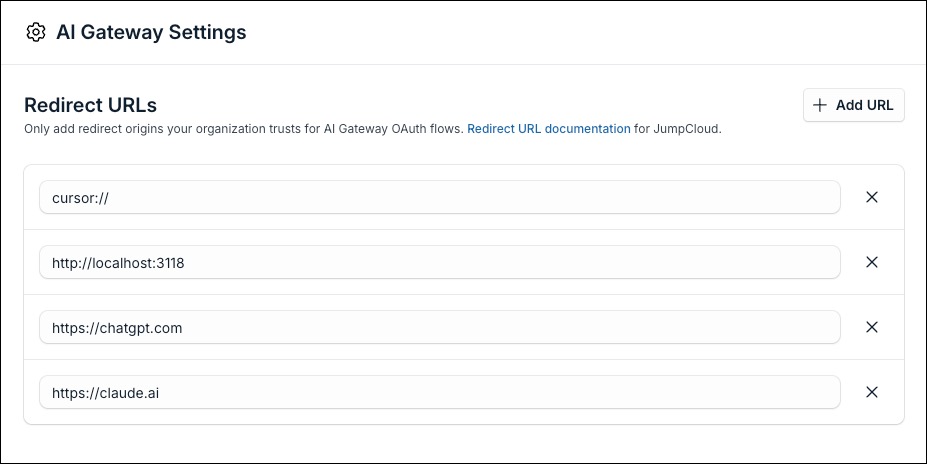
Configuring Trusted Redirect URLs
To secure your AI integrations, the AI Gateway uses an allowlist of trusted Redirect URLs to define which AI client origins are permitted to receive OAuth redirects and authentication tokens.
During the OAuth flow, the client application redirects the user to JumpCloud for consent, and then redirects the user back to the client’s URL. If the AI client’s origin doesn’t match a URL in your trusted list, JumpCloud blocks the connection. You must add the domains or customer URIs for every AI client your organization uses.
To configure trusted redirect URLs:
- From the JumpCloud Admin Portal, go to Access > AI Gateway.
- Click the AI Gateway Settings in the top right.
- In the Redirect URLs section, click + Add URL.
- Enter the redirect origin you want to trust:
- Web-based AI Clients: Enter the standard HTTPS domain
- Claude: https://claude.ai/api/mcp/auth_callback
- ChatGPT: https://chatgpt.com/connectors/oauth
- Local Desktop IDEs: Enter the localhost IP with port number to allow local clients to receive tokens on varying ports (for example http://localhost:3118).
- Custom App Protocols: Enter the custom URI scheme required by specific desktop applications:
- Cursor: cursor://anysphere.cursor-mcp/oauth/callback
- Web-based AI Clients: Enter the standard HTTPS domain
- To remove a redirect and revoke its ability to receive OAuth tokens, click the X icon next to the URL.
Configuring AI Clients
After you configure the MCP servers and establish your trusted redirect URLs in the Admin Portal, users must configure their specific AI clients to connect to the JumpCloud AI Gateway MCP endpoint: https://ai.jumpcloud.com/mcp.
Users are redirected to the AI Gateway which presents a list of all MCP servers you've configured in JumpCloud. Users can select each application and authenticate via OAuth or by entering a specific API key, depending on your server configuration.
Direct users to the Supported AI Gateway Integrations for guides on connecting each AI client.
Using the Activity Log
The Activity Log tab provides a detailed, searchable audit trail of all AI interactions to help you monitor behavior and maintain compliance. This data is powered by Directory Insights. You can use this tab to investigate anomalies, track token consumption, and audit requests across your connected MCP servers.
On the Activity Log tab, you can view the following information:
- Time: The exact date and time the event occurred.
- User: The email address of the user associated with the action.
- Action: The specific event type, such as the MCP Tool Call.
- Service: The connected MCP server (for example, Github) where the action took place.
- Details: The granular telemetry of the request, including response status and requested tool.
To find specific events, click Search activity... or click Filter to narrow the log results. To export the log data for compliance or external reporting, click the download icon in the top right.
Additional Resources
- Tutorial: JumpCloud AI Gateway
FAQ
No. When you click + Add Server in the JumpCloud Admin Portal, the App dropdown menu populates with the applications you have already configured for SSO in your JumpCloud org.
An app appearing in the dropdown does not mean it natively supports MCP. JumpCloud only links the AI Gateway connection to your existing SSO app for organizational reporting purposes. You must verify with the application vendor that they host a supported MCP server before attempting to configure it here.
This typically happens if the AI client's Redirect URL has not been correctly added in your AI Gateway Settings, causing JumpCloud to block the handoff for security reasons.
When users hit the error page in their browser, the redirect URL might be appended in their URL bar to help you investigate.