Remote desktop protocol (RDP) is a proprietary communication protocol initially built by Microsoft. It allows two computers to exchange a graphical user interface (GUI) via transmission control protocol (TCP)/internet protocol (IP). RDP is an extension of the T.120 point-to-point (P2P) communication protocols that are standardized by the International Telecommunications Union (ITU).
There are three primary use cases for RDP. Firstly, IT admins can use this protocol to remotely perform administrative tasks, such as PC tuneups, ID protection settings, software installations, computer troubleshooting, and printer setups. By using RDP, IT teams can easily maintain and diagnose problems that individual employees are encountering from afar.
Secondly, employees can leverage RDP to access their workstations remotely. For example, they could access enterprise resources while working from home or traveling. Thirdly, RDP is also helpful for “headless computers” or thin clients that employees may want to leverage to access powerful workstations in the office.
How Remote Desktop Protocol Works
RDP is a secure protocol that furnishes the user on one computer with a GUI that they can use to connect to another PC over TCP/IP network directly. For this to work, the user originating the request must have an RDP client application installed on their computer. Similarly, the PC the user is trying to access must be running an RDP server software, allowing the client to connect remotely.
Once linked, the user can now see the desktop of the PC to which they have connected through RDP to access applications and files on that desktop. All current Windows operating systems (OSs), including Windows Server and desktop versions, come with a built-in RDP server that provides remote desktop connection capabilities.
However, the RDP client software is only available to Windows Pro and higher versions. For example, Windows Home users must upgrade their OSs to Windows Pro or higher versions to use remote desktop connection (RDC) services.
RDC is one of the three client components of Microsoft’s Remote Desktop Services (RDS). It enables remote client PCs — powered by RDP — to connect with Windows-based platforms. The two other client components of Microsoft’s RDS are Fast User Switching and Windows Remote Assistance. Aside from RDCs, RDP clients are available for Unix, Linux, macOS, Android, and iOS.
By default, RDP-based communications are established over TCP port 3389, or if the remote desktop gateway is used, the connections are made over TCP port 443. When a user connects to a remote PC, the RDP client redirects the mouse and keyboard events to the remote server. RDP uses its own on-screen mouse and keyboard driver on the remote server to receive these input events from RDC clients.
To help render the user’s actions, RDP uses its own graphics driver to construct the display output into TCP/IP packets that are then redirected to the RDC client. On the client’s side, the RDC client receives the rendered data and translates it into corresponding graphics device interface (GDI) application programming interface (API) calls.
As a multi-channel platform, RDP uses separate virtual channels for device communication, presentation data, and encrypted input events between the RDP client and server. RDP’s virtual channel ecosystem is extensible and can support up to 6,400 disparate channels for data connections and multipoint transmissions.
Pros and Cons of RDP
Below are some advantages that organizations and users can derive from RDP:
- Easy access to enterprise resources. Employees can easily connect to their workstations from anywhere in the world. The protocol eliminates the need for employees to travel with flash drives.
- Streamlined IT management. IT teams can manage every aspect of the enterprise’s network in real time from one location. For example, they can edit the permissions to individual users or groups within the organization through RDC.
- Cost savings. Using RDP for RDC can help an organization save on hardware and ongoing maintenance costs. Employees can use their personal devices under the bring-your-own-device (BYOD) framework for work-related activities.
Despite the advantages, RDP has its own disadvantages. Below are a few of them:
- Internet connectivity. You need reliable internet connectivity for a client PC to connect successfully to a remote machine. Otherwise, the entire RDC will break down.
- Security vulnerabilities. Although RDP-based sessions have inbuilt data encryption, access control, and activity logging capabilities, the protocol has inherent weaknesses that hackers can exploit and compromise the network. Let’s discuss some of these risks in more detail in the next section.
RDP Security Risks
RDP is the foundation for many remote access solutions within Windows-based environments. As such, it has become one of the most popular targets for hackers. Below are three common RDP security risks that hackers can exploit:
Weak Authentication
Most users rely on passwords to protect their workstations. They often reuse the same password across different systems, including RDP logins. If the password is weak, any hacker can attempt a brute force attack through techniques such as credential stuffing or rainbow table attack to gain access to the enterprise network. To mitigate these attacks, organizations can use single sign-on (SSO), multi-factor authentication (MFA), and adhere to password management best practices.
Unrestricted Port Access
By default, RDP connections take place on TCP port 3389. If this port is left open, an attacker can easily carry out on-path attacks and compromise the network. To protect against port-based attacks, you’ll need to lock down port 3389 and implement firewall rules.
Unpatched Vulnerabilities
Microsoft has already provided and continues to provide OS updates and hotfixes for some of the most severe RDP vulnerabilities. Still, some of these vulnerabilities can cause damage, especially when left unpatched.
For example, “BlueKeep”—a wormable attack that allows hackers to execute arbitrary codes on a remote PC—can cause damage to the organization if the OS is not patched. To mitigate against these vulnerabilities, you can leverage patch management tools to ensure their OS and applications are up to date.
RDP Alternative
It’s no longer a secret that the shift to hybrid workplaces is having severe security implications for most modern organizations. To succeed in such environments, companies must ensure remote access solutions like mobile device management (MDM) tools are secure and fit into the organization’s budget.
JumpCloud Remote Assist is a low-cost, easy-to-use, and secure remote access solution. IT admins can leverage the tool to connect to end users’ Windows, macOS, and Linux endpoints and fix technical issues from an intuitive cloud-based console.
When used in an organization, JumpCloud Remote Assist allows IT admins to streamline access to organization resources. For example, they can easily customize, provision, and manage new security policies that better suit evolving workflows from a single place.
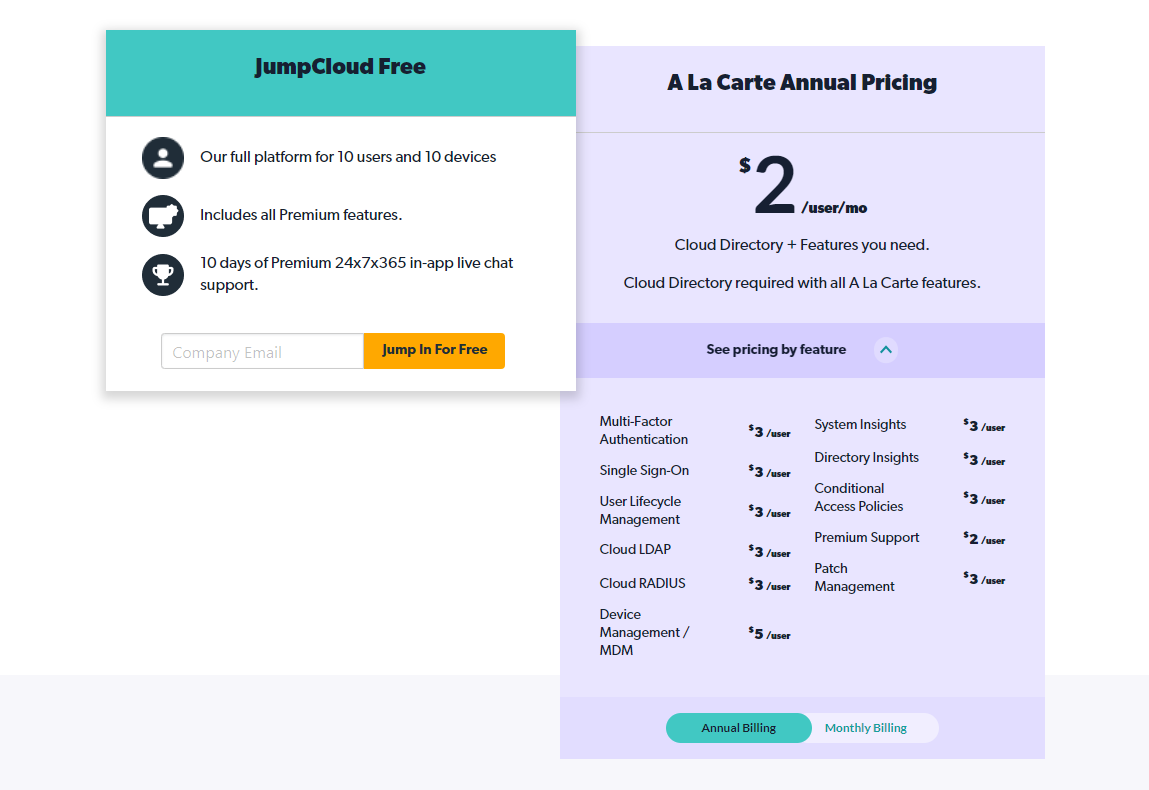
Remote Assist will be a FREE add-on for organizations already using the JumpCloud Directory Platform® to manage Windows, macOS, and Linux endpoints.