
The Three I’s of Intelligent IT
How to Automate, Secure, and Unify Your Identity Management
AI has changed the way organizations operate, forever.
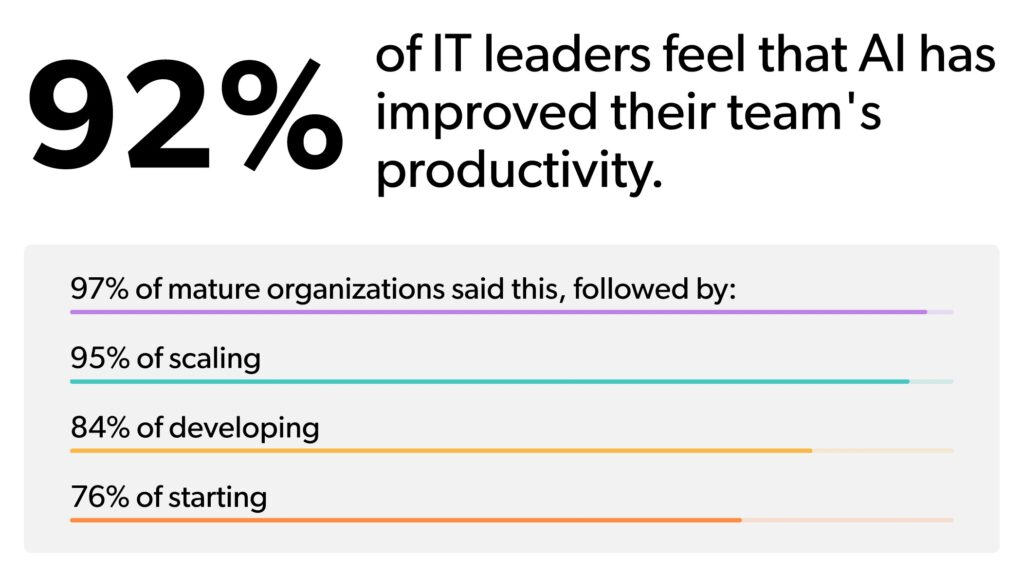
Despite the raging debate, there is a growing consensus among IT leaders: AI is a powerful driver of productivity. In a very short time, this technology has fundamentally changed how we work, opening a world of opportunity for IT teams.
But with opportunity, comes the responsibility to manage new risks.
For most leaders, the conversation has moved past the hype. The question is no longer “Should we use AI?” but “How quickly can we build the infrastructure to support it safely?”
We are currently standing at a defining moment. Tools like Copilot, Gemini, and Claude Code are deeply woven into business workflows. These capabilities evolve every day, and the barrier to entry continues to decline. This creates a world of opportunity to drive operational advantage and strategic agility.
But seizing AI’s full potential requires more than just launching pilot projects. You cannot treat AI governance as a siloed effort. You cannot focus only on the tools or the outputs. True success requires an integrated, identity-centric model that embeds security and automation into every layer of your stack.
The same IT leaders who celebrate AI’s productivity gains also agree on a critical point: Secure identity and access management (IAM) is the foundation of successful AI adoption.
This is what we call intelligent IT. And it all starts with identity.
To lead your organization through this transition, you need a layered approach to identity. This model positions identity as the center of your world through three core disciplines:
-
1
Identity Governance (IG)
-
2
Identity Security Posture Management (ISPM)
-
3
Identity Threat Detection and Response (ITDR)
When you integrate these layers, you create a security-first infrastructure. This foundation supports AI-driven decision-making and automation at scale, safeguarding the sensitive systems AI needs to connect to. Without this solid framework, AI adoption can lead to ballooning costs, shadow AI, and compliance gaps.
A well-established identity foundation helps you unify and automate critical processes. It provides the security and scalability needed to unlock AI’s full potential while aligning with your risk management priorities.
In this eBook, we will explore:
-
How Identity Governance ensures visibility and oversight of permissions.
-
How Identity Security Posture Management delivers granular control to secure critical assets.
-
How Identity Threat and Detection Response enables proactive detection to mitigate risks.
Together, these layers form the bedrock for an intelligent, secure IT framework. The kind that helps you accelerate AI adoption confidently and strategically. And most importantly: safely.
AI Readiness vs. AI Maturity: The Dual Disconnect
There is a common misunderstanding in modern IT: the belief that using AI tools is the same as being “AI mature.” In reality, adopting tools and building the infrastructure to secure them are two completely different achievements. Our recent industry data highlights a significant readiness gap. While 40% of organizations claim to have achieved AI maturity, only 22% actually meet the objective criteria for “Leading” readiness.

Many teams deploy advanced automation before they have the underlying governance to manage it. There is a perception that AI is just another piece of software. This leads to rampant shadow AI, where employees use unmanaged tools to handle company data. When IT is forced to react, they often build siloed policies for each specific tool.
But AI does not exist in a vacuum. It interacts with your cloud apps, your local devices, and your sensitive databases. If your identity frameworks are not unified, you create blind spots.

True AI readiness means your entire IT base works in harmony. Your IAM, security protocols, and governance frameworks must operate as a single system. Identity serves as the common denominator. It bridges human users, traditional machine accounts, and the emerging world of autonomous AI agents.
By establishing a secure foundation now, you ensure that you can scale your tech stack safely. You move from trying out tools to building a platform.
The Three Faces of Identity: Moving Beyond The Binary
To manage an intelligent environment, we must first redefine who, or what, is accessing our systems. For years, identity models relied on a simple binary:
Human Identities
People who possess judgment but operate at human speed. Their behavior is usually semi-predictable.
Non-Human Identities (NHIs)
Scripts or service accounts that execute at machine speed. They follow rigid rules and have zero independent judgment. We call this deterministic behavior.
Today, this binary model fails. We have entered the era of the AI Identity.
The Rise of AI Agents
AI agents are a distinct third category. They operate with simulated judgment at machine speed. Unlike traditional scripts, AI agents are “probabilistic.” This means they are goal-oriented. They assess context and make independent decisions to achieve an objective.
If an AI agent is given a goal, like “organize these customer files”, it might decide to move data between folders or change permissions to finish the task. If that agent is not governed by strict identity controls, it could inadvertently expose sensitive information.
Managing the Identity Explosion
This “identity explosion” requires a framework tailored to how autonomous agents behave. You cannot manage an AI agent the same way you manage a standard employee or a simple script. You need a system that understands intent, monitors for drift, and can revoke access in milliseconds if the agent moves outside its guardrails.
Understanding these three faces of identity (human, machine, and AI) is the first step in building a modern security posture.
Identity Governance (IG) | The Foundation
Intelligent IT begins with a solid system of record. Identity Governance (IG) is the policy layer that manages the digital lifecycle of every entity in your organization. If you cannot see an identity, you cannot secure it.
-
What is Identity Governance (IG)?
Identity Governance serves as your system of record. This is how you manage the operational lifecycle of every identity within your organization. IG is the policy layer that manages digital identities and access rights throughout their entire lifecycle.
In a legacy environment, IG was often a manual process. IT teams would manually enter data when someone joined the company and hope they remembered to remove it when that person left. In an intelligent IT environment, this is no longer sustainable.
Modern governance requires automation. You must move toward “event-driven” workflows. This means your HR system (HRIS) should automatically trigger access changes the moment an employee’s status changes. This is known as the Joiner, Mover, Leaver (JML) process.
Evolving for the Agentic Era
For AI agents, governance must adapt even further. You need an “Instantiate, Update, Decommission” model.
-
Instantiate: Every AI agent must be born with a clear purpose and a limited scope.
-
Update: Permissions must be reviewed constantly as the agent learns or its tasks change.
-
Decommission: The moment a task is finished, the agent’s access must be revoked.
This prevents the creation of “zombie agents”—autonomous entities that retain access to your systems long after they are needed. By unifying identity management through a strong governance layer, you eliminate orphaned accounts and reduce organizational risk.
Identity Security Posture Management (ISPM) | The Guardrails
Once your foundation is set, you need active enforcement. This is the role of Identity Security Posture Management (ISPM). While IG tells you who should have access, ISPM tells you if that access is actually secure.
-
What is Identity Security Posture Management (ISPM)?
Identity Security Posture Management (ISPM) serves as the proactive hygiene layer for your environment. It continuously monitors your identity infrastructure to detect misconfigurations and over-privileged accounts. ISPM validates the security of IT by providing quantifiable metrics on identity risk.
ISPM acts as a continuous monitor for your identity infrastructure. Its first job is discovery. You must bring shadow AI and undocumented services into your governed perimeter. Using API-based inventory, ISPM finds every connection and maps it.
This allows you to create an “access graph.” You can see the complex web of permissions across your cloud environments. This visibility is vital for identifying “toxic combinations”—where a single user or agent has a set of permissions that could be exploited to gain administrative control.
From Static Checks to Contextual Evaluation
ISPM moves the security question from “Is the credential valid?” to “Is the context appropriate?” To secure AI agents, ISPM enforces two critical concepts:
-
Principle of Least Privilege (PLP): Ensuring entities only have the absolute minimum access required.
-
Just Enough Access (JEA): Granting granular, task-specific permissions that limit the “blast radius.”
If an AI agent is compromised, JEA ensures the attacker cannot use that agent to move laterally across your network. ISPM also monitors for “Master Key” risks, ensuring that no single entity, human or AI, can access your root administrative estate without extra layers of verification.
Identity Threat Detection & Response (ITDR) | The Security Blanket
The final layer is your vigilance layer. Identity Threat Detection and Response (ITDR) operates on a simple assumption: eventually, your preventive controls will fail. ITDR is your emergency brake.
-
What is Identity Threat Detection and Response (ITDR)?
Identity Threat Detection and Response focuses on identities in motion. It operates on the assumption that preventive controls will eventually fail. ITDR functions as the ultimate safety net, identifying and neutralizing unauthorized activity before it leads to a major breach.
Modern ITDR relies heavily on behavioral analytics. This allows systems to detect subtle anomalies such as credential abuse or unusual lateral movement. This is much more effective than relying on static signatures. Deception technology also plays a vital role. Honeytoken identities trap attackers the moment they interact with a fake resource.
In the context of AI, ITDR monitors for behavioral drift. Drift occurs when an AI agent’s behavior starts to change. This could happen because its underlying model was updated or its training data caused it to deviate from its original profile. If an agent suddenly tries to access a database it has never touched before, ITDR recognizes the deviation instantly.
The Automated Response Loop
When a threat is detected, the response must be faster than any human could manage. The ITDR loop follows four steps:
-
1
Detect: Identify the anomaly or unauthorized movement.
-
2
Shutdown: Automatically kill the session or revoke the compromised token.
-
3
Analyze: Determine how the breach happened and what the attacker was after.
-
4
Patch: Update your governance and posture rules to prevent it from happening again.
While the response is automated, the strategy remains with you. A “Human-in-the-Loop” approach ensures that IT leaders maintain ultimate oversight over complex remediation efforts. You aren’t losing control to AI; you are using AI to maintain control at a scale that was previously impossible.
How The Three I’s Interlock Together
Identity governance, security posture management, and threat detection are not separate strategies. They are three parts of a single identity fabric.
When these layers are aligned, your IT ecosystem becomes proactive and resilient.
- IG provides the definitive record of access.
- ISPM sets the contextual rules and monitors hygiene.
- ITDR acts as the safety net for any breach of those boundaries.
The Business Impact
The benefits of this unified approach extend far beyond security:
Operational Efficiency
Automation handles the “busy work” of identity management. Your team can stop resetting passwords and start architecting business growth.
Compliance Readiness
Because you have a continuous record of every access point and change, audits become simple and predictable.
Strategic Agility
When you know your foundation is secure, you can adopt new AI tools faster than your competitors. You aren’t held back by “what-ifs.”
Stepping Into Your Strategic Future
The evolution of technology requires an equal evolution in how we manage infrastructure. Unification goes beyond software—it requires a unification of policies, training, and culture.
By embracing the three I’s of intelligent IT, you position your team to navigate the agentic revolution with confidence. You optimize costs, reduce complexity, and provide the secure environment your organization needs to innovate.
Your journey does not end here. To fully realize the potential of this shift, you must continue to evaluate the structural changes AI brings to your network.
Discover the next steps in your strategic evolution:
Read The AI Mandate
Understand the critical role IT plays in making secure AI a reality across the entire organization. This eBook provides actionable strategies for approaching the people, technologies, and thought processes that drive successful, enterprise-wide AI adoption.
Explore The Third Face of Identity
Dive deeper into why AI must be managed as a distinct, separate identity class. This guide breaks down how probabilistic AI agents are changing the fundamental framework of identity management, and what you need to do to secure them.
The organizations that build this layered foundation today will lead the market tomorrow. It is time to optimize your infrastructure and step firmly into your strategic future.


