Editor’s Note: This article was originally published at Cloudfresh, which you can read here.
Let’s be honest. Shadow IT isn’t going anywhere.
Teams move fast. SaaS tools are easy to buy. Remote work is normal. Waiting weeks for approval feels outdated.
So people solve their own problems.
That doesn’t make them reckless. It makes them resourceful.
The real question is this: What if you could keep that speed and still stay in control?
And today, it is answered by a Platinum-tier JumpCloud Partner.
It’s Bigger Than Security
Most conversations about Shadow IT start with cyber risk.
Want to hear the bigger story? Think of operational clarity.
When software purchasing spreads from one department to another, traditional FinOps and IT asset management lose visibility.
The bottom line? Fragmented budgets, duplicated platforms, and inflated costs without anyone intending it.
EY reports that 64% of CISOs are dissatisfied with how non-IT employees adopt cybersecurity best practices. They also rank weak compliance outside central IT among the top internal challenges organizations face.
That tension tells us something important.
This isn’t about bad behavior. It’s about disconnected systems.
McKinsey & Company points out that when ownership of software capabilities is unclear, new tools get created outside central IT. The result? Extra cost. Limited budget tracking. More complexity later.
But complexity can be reorganized. And visibility changes everything.
The Opportunity Hidden Inside Shadow IT
Shadow IT shows you where innovation is happening.
- It highlights unmet needs.
- It reveals which tools employees actually value.
- It exposes inefficiencies in your procurement flow.
Yes, unmanaged tools can bypass MFA, endpoint monitoring, or DLP controls.
But that’s not a reason to panic. It’s a reason to discover.
If multiple teams independently adopt the same tool, that’s a clear indication of demand. Forward-looking organizations treat Shadow IT as intelligence rather than a problem.
Here’s a quick Shadow IT example—a mid-sized outsourcing software development company.
- Multiple teams sign up for an outside project tracking platform.
- IT discovers the trend and negotiates a company-wide license, later integrating the platform into SSO and compliance workflows.
- What has started as fragmented Shadow IT becomes a standardized, secure tool that employees were already comfortable using.
In its Digital Defense Report 2025, Microsoft identifies unmanaged digital assets as common targets for advanced attackers.
Say, a company finds out a departing employee still has access to a design collaboration platform purchased outside IT oversight.
The platform holds sensitive projects. Attackers exploit a vulnerability in a connected third-party plugin and potentially compromise customer data.
Without visibility, IT couldn’t have acted in advance.
But the takeaway isn’t fear. It’s awareness.
You can’t protect what you don’t see. So make it visible.
Governance That Enables Growth
Banning tools rarely works. If anything, it slows teams down and pushes activity underground.
Instead, you need to orchestrate.
So don’t ask “How do we stop this?” Try “How do we govern this?”
That will change everything.
Treat Data as Business
PwC advises treating data exposure as a business issue, not just an IT problem.
Shadow IT becomes manageable when business leaders participate in data classification and governance. When departments help define how their data is handled, accountability rises naturally.
Security becomes shared ownership.
Rethink How Technology Is Funded
McKinsey suggests moving toward fixed-capacity funding models.
Why? Because structure leads to understanding.
When business units have a clear financial capacity to operate within, software decisions become intentional. Investments are visible, and trade-offs are clear.
Software isn’t quietly spreading anymore. On the contrary, it becomes part of strategic planning.
Imagine that your Marketing team subscribes to a new analytics tool, Sales picks a different CRM plugin, and Customer Success adds an extra engagement tracker for whatever justified reason they have. Two years later, IT reaches out because there now has to be a single-pane-of-glass customer view. In this Shadow IT example, integration costs skyrocket, even though there are no bad intentions at all, just independent work.
But if IT and finance could’ve seen it right away, they would’ve checked for overlaps with existing tools, approved only the most necessary licenses, and reduced untracked subscriptions.
Protect Data without Blocking Productivity
Device management leaders like Apple show how balance works.
Features like Managed Open In on iOS and iPadOS allow you to decide how corporate data moves between managed and personal apps and make boundaries clear, protection strong, and disruption minimal.
The key takeaway is that security can and must feel supportive, not restrictive.
Shadow IT Is the New Normal
Distributed work and SaaS accessibility have forever changed how procurement gets done.
That being said, Shadow IT is far from being temporary. It reflects how teams roll these days and will roll in years to come.
Organizations that implement continuous discovery, adaptive FinOps, and Zero Trust architecture gain something powerful, which is confidence.
Confidence in spend, in access, and in audit readiness.
JumpCloud treats Shadow IT as a lifecycle challenge and covers discovery, governance, optimization, and offboarding, all connected.
Instead of chasing problems, you gain a live map of your SaaS ecosystem.
Let’s look at how.
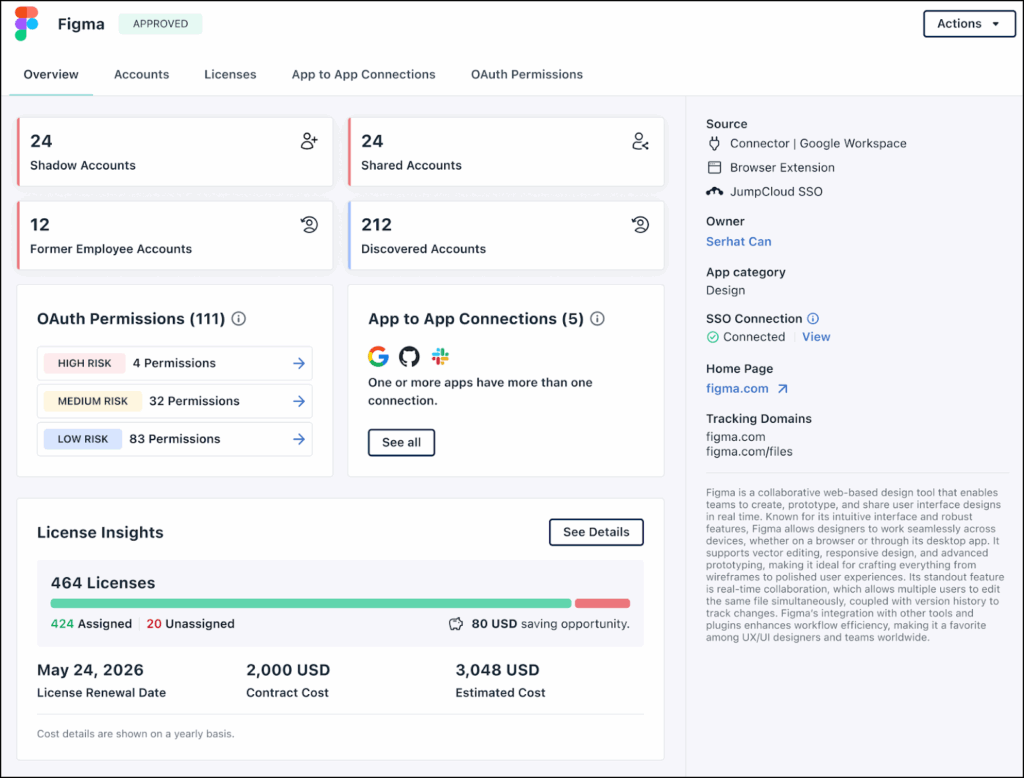
JumpCloud SaaS Management: The Four Areas of Discovery
First things first, Shadow IT doesn’t wait for you to catch up. It starts in the browser, in personal accounts, on unsanctioned apps.
That’s why JumpCloud approaches SaaS Management as more than monitoring.
It doesn’t just spot rogue apps. It gives you full visibility, continuous discovery, Shadow IT risk insight, and control over every SaaS tool in your organization, whether approved or not.
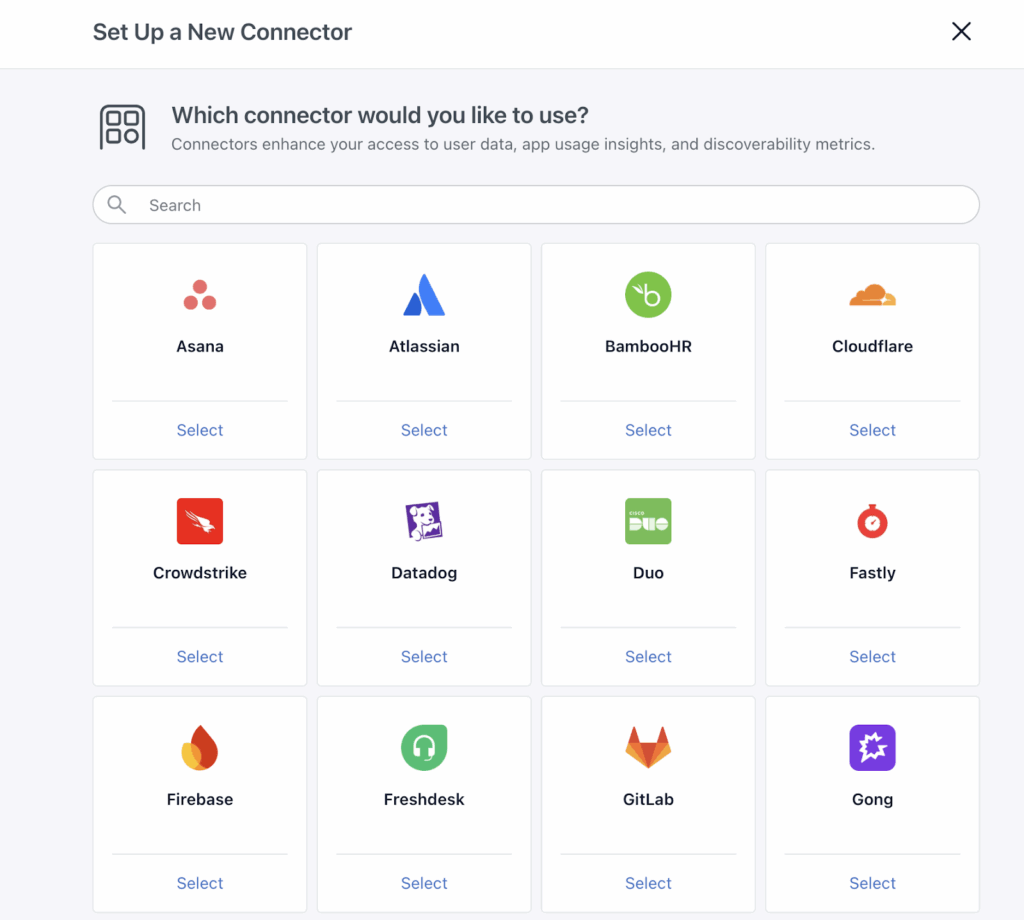
Area #1. Direct Connectors: Deep Insight from Core SaaS
JumpCloud integrates natively with over 30 platforms, including:
- Google Workspace.
- Microsoft Entra ID.
- Slack.
- Atlassian.
- Zendesk.
- Salesforce.
- Zoom.
Each connector speaks directly to the app via API and pulls detailed user account inventories, activity logs of who’s using the app and how, app-to-app connections revealing integrations that could create Shadow IT, OAuth permissions and access scopes, and license usage data from supported SaaS providers.
The power of these connectors is that they see beyond surface-level usage and bring into light hidden accounts, redundant access, and Shadow IT activity that otherwise fly under IT’s radar.
Area #2. JumpCloud Go™ Browser Extension: Real-Time Visibility
The browser is where Shadow IT begins. JumpCloud Go™ captures live, user-level SaaS activity as it happens.
It works by:
- Detecting sign-ups, logins, and usage patterns for every SaaS application accessed in the browser.
- Recording frequency of visits, showing which tools gain traction and which fade away.
- Capturing activity for apps not connected to SSO, including unsanctioned or personal accounts used for work.
Requirements:
- JumpCloud Go™ installed in the user’s browser.
- Users logged into the JumpCloud User Portal or any SSO-enabled application.
Passwordless login improves user experience, but isn’t required for discovery to function.
Area #3. SSO-Connected Applications: Continuous Governance
JumpCloud also monitors applications that are already part of your SSO ecosystem. Once an app is integrated with JumpCloud SSO, it’s:
- Instantly recognized and cataloged.
- Automatically labeled as Approved.
- Continuously monitored for usage and login behavior.
IT can see a centralized list of all SaaS apps connected via JumpCloud SSO, which users are logging into which apps and how often, and trends in adoption across departments.
That way, you can make sure that managed apps are clearly distinguished from the unvetted ones, which makes audits, compliance, and Shadow IT risk assessment plain and automated.
Hint: apps must be set up and active within JumpCloud SSO to be automatically tracked.
Area #4. Identity as a Discovery Engine
Identity platforms are where employees authenticate, and that’s where valuable insight lies. JumpCloud leverages Google Workspace and Microsoft Entra ID to uncover hidden SaaS usage.
It can detect third-party apps accessed with corporate credentials, OAuth permissions granted by users to external tools, and which employees have accounts in unmonitored or Shadow IT apps.
This switches identity from a login mechanism to a governance tool and gives IT the ability to enforce security, revoke risky access, and guide employees to approved alternatives.
The Six Business Outcomes: The Road to Control
JumpCloud doesn’t just detect Shadow IT. With it, governance turns into tangible business outcomes.
Outcome #1. Full Visibility
- Live SaaS inventory for every user.
- Discovery of both approved and Shadow IT apps.
- Complete insight into which tools are actively used, which are dormant, and which are redundant.
Outcome #2. Cost Optimization and ROI
- Identification of “zombie licenses,” or accounts paid for but unused for over 30 days.
- Optimized SaaS spend across departments.
- Informed decision-making about which licenses to renew or retire.
As a result, your organization can reclaim thousands of dollars monthly by simply removing unused subscriptions and preventing purchases that you don’t really need.
Outcome #3. Proactive Security and Compliance
- Non-IT employees often choose tools for ease of use, not security.
- Shadow IT may violate internal security standards or compliance guidelines.
JumpCloud enforces governance proactively, with policies such as:
- Approve: unrestricted access.
- Warn: notify users about potential Shadow IT risks.
- Block: prevent use of unsafe applications.
No more reactive incident response. Only preventive, proactive security.
Outcome #4. Offboarding as It Should Be
Shadow IT makes revoking access complicated.
JumpCloud makes sure that departing employees lose access to all SaaS resources, including personal accounts tied to work tasks that could expose sensitive corporate data.
Outcome #5. Accidental Backdoors Never Opened
Shadow IT accounts created with the same set of corporate credentials are high-value targets for hackers.
JumpCloud spots such accounts, brings them in for review, and protects the login info.
That’s exactly how you shrink an overall attack surface and keep your employees productive.
Outcome #6. Improved Employee Experience
Instead of banning everything outright, JumpCloud guides employees toward approved alternatives, which makes them more likely to follow secure practices.
In turn, Shadow IT becomes a signal for improving UX rather than a source of punishment.
Before vs. After: The JumpCloud Effect
| Function | Life with Shadow IT | With JumpCloud SaaS Management |
| Visibility | None | Real-time inventory of every app, approved and Shadow IT |
| Costs | Chaotic department spending | Centralized budget tracking, license optimization |
| Security | High risk of unauthorized access | Automated auditing and access enforcement |
| Compliance | Stressful, time-consuming audits | One-click reports for GDPR, SOC2, and other frameworks |
The main idea is, Shadow IT doesn’t have to feel like a threat. It can become insight.
With visibility, governance, and user-focused design, you don’t slow innovation down. Rather, you give it direction.
Building to Solve for Shadow IT in the Real World
Cloudfresh doesn’t just do rollouts. We help teams make it work in the real world. Our focus is on helping organizations get full value from cloud identity, access, and device management, especially in environments where Shadow IT is growing fast.
JumpCloud itself is a modern, cloud‑based directory and identity platform that makes it fairly easy for companies to secure users, devices, and access to everything from SaaS apps to on‑prem servers, no matter where your teams work. It centralizes IAM, SSO, MFA, Zero Trust security, password management, and cross‑platform device management, all from the cloud.
But powerful tools only matter if you can use them effectively. That’s where Cloudfresh:
- Helps you choose the right JumpCloud license for your needs, from core directory services to full identity, device, and SaaS governance.
- Customizes and integrates JumpCloud with your existing systems so you get value from the get-go.
- Trains your IT team and provides ongoing support so you stay ahead of Shadow IT and security risks.
- Runs security audits and best‑practice reviews so your cybersecurity gets stronger every day.
Whether you’re scaling fast, dealing with decentralized teams, or trying to bring order to sprawling SaaS usage, we help you turn Shadow IT from chaos into advantage.
FAQ
Shadow IT simply means any app or service that your employees use without your IT department knowing. The main concern is that you can’t really do anything about it in case things go south (e.g., data breaches involving reused passwords or unintended corporate data leaks).
Sure. If you communicate openly with your teams, you can find out which tools they find most useful for work and start managing them properly. That’s a typical win-win situation.
JumpCloud’s approach stands on three pillars, each working both independently and together, namely direct connectors, JumpCloud Go™ browser extension, and SSO integration.





