Open Cloud Directory
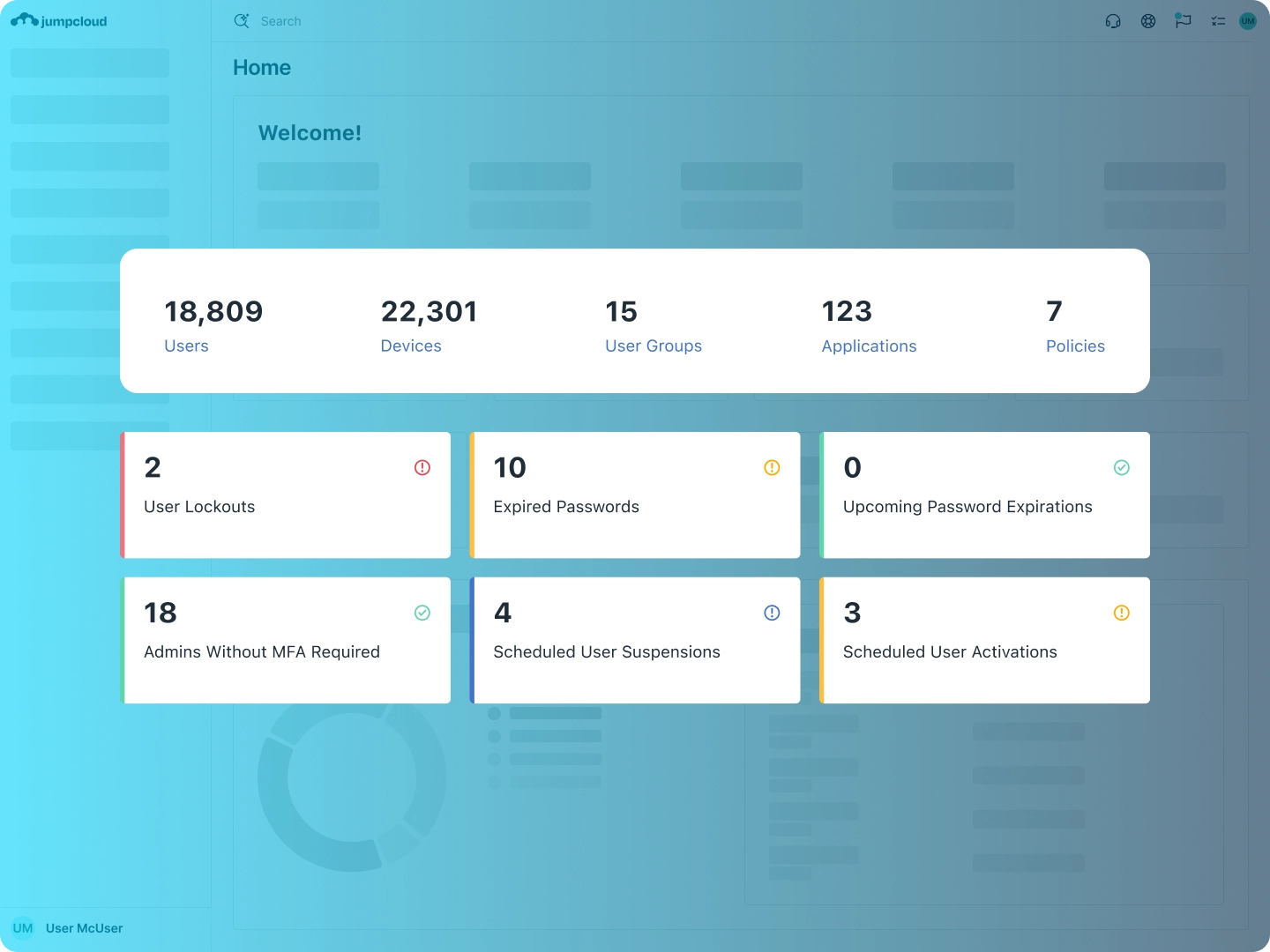
Centralized, secure, and robust identity, access, and device management capabilities.
Build a Strong, Future-Proof IT Foundation
Your organization will never stop evolving, and your technology choices will have to change over time to support it. JumpCloud, built on a bedrock of open standards and expansive functionality, makes it possible to effortlessly connect, modify, and grow your preferred suite of tools to provide each user with one, unified identity that connects them to their resources with Secure, Frictionless Access™.
One Unified Identity Per User
Create user accounts in JumpCloud, or easily import them from another authoritative identity source such as your HR system or existing directory. With JumpCloud, identity and access changes made in one source are immediately and automatically reflected across all connected resources. Users get secure access to all of their resources using one, core identity.
Blog Post
| How JumpCloud’s HRIS Integration WorksCourse
| Introduction to JumpCloud and Open DirectorySupport Article
| Get Started: Directory Integrations
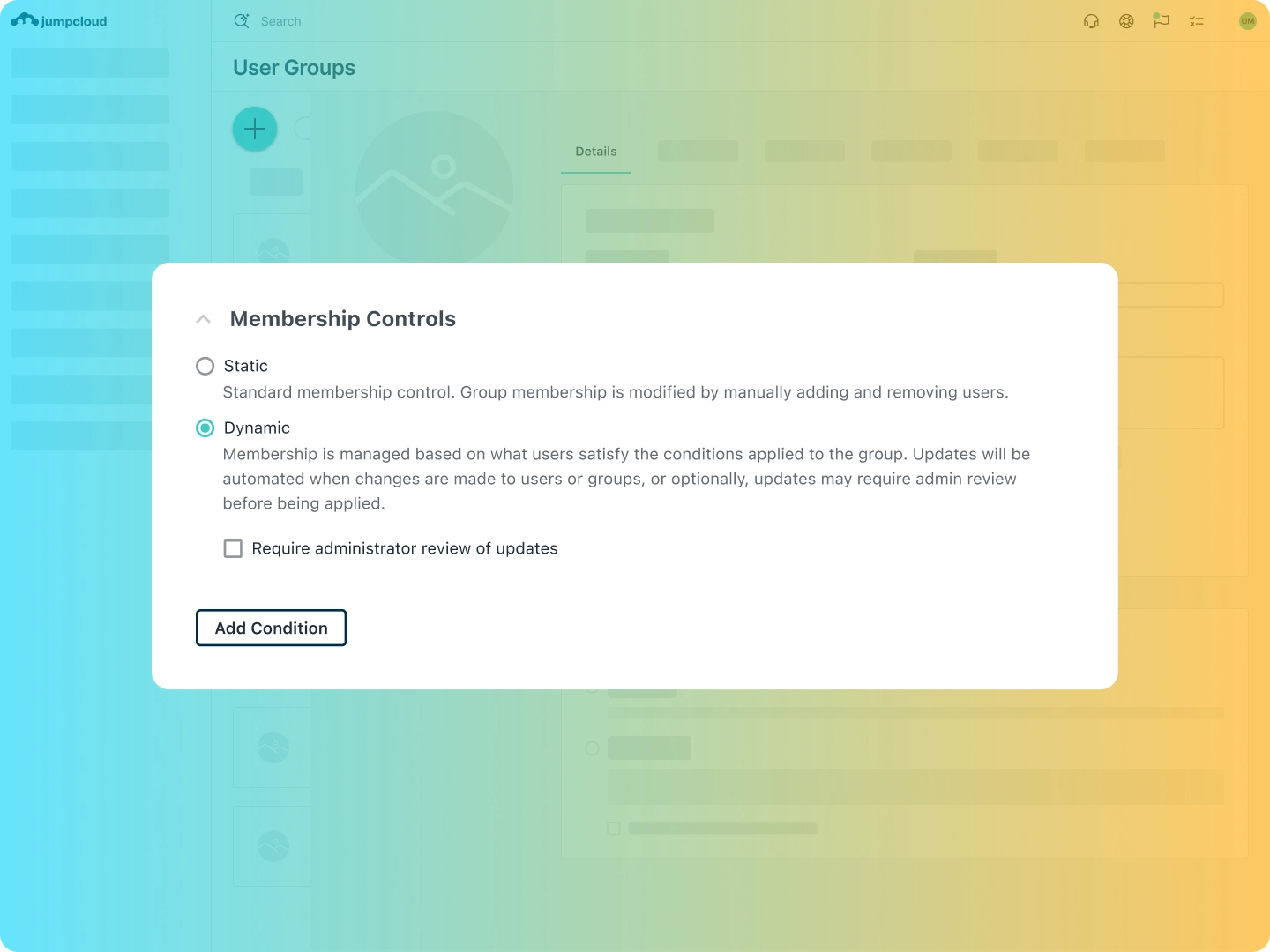
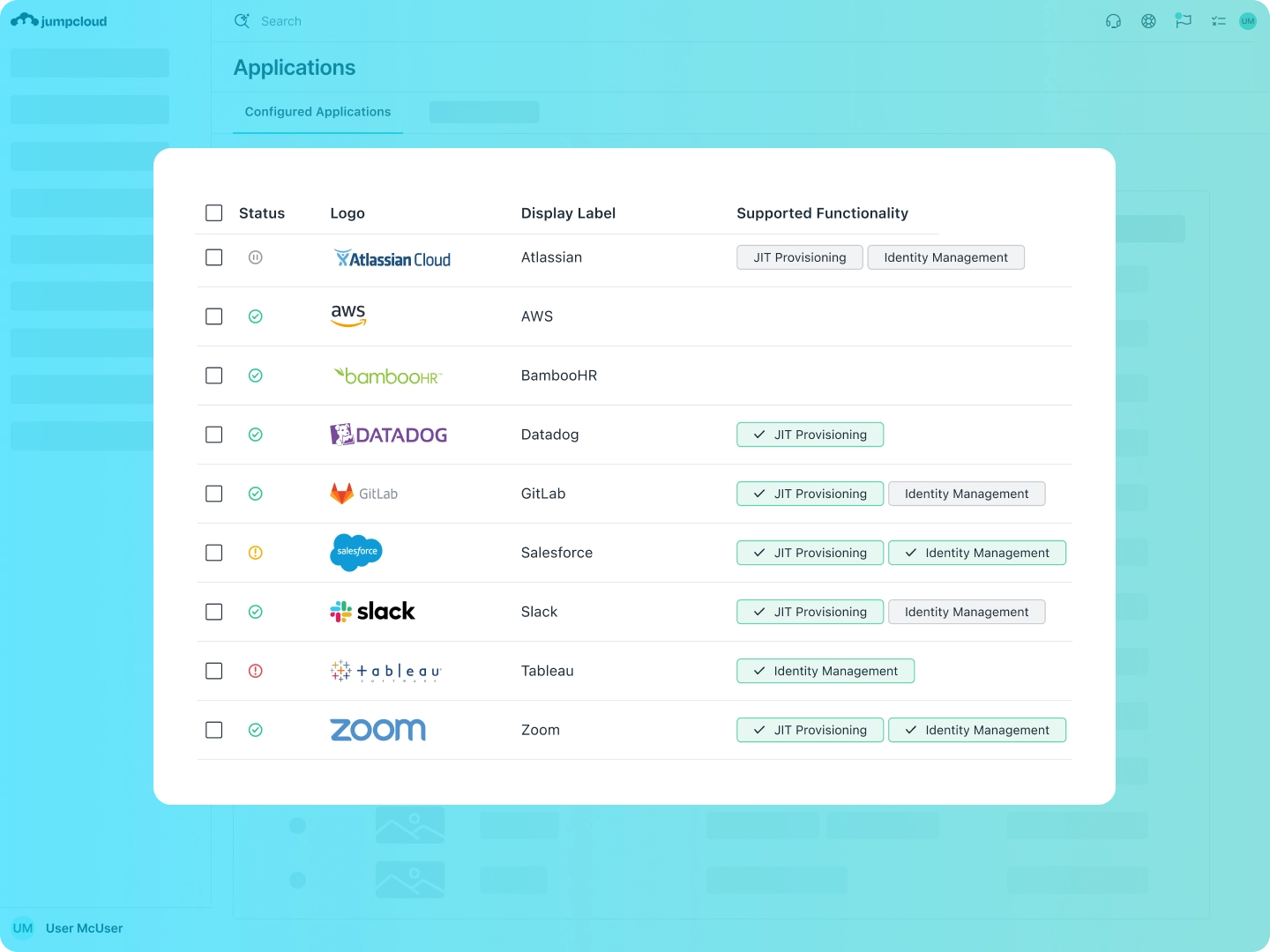
Flexible, Open Integrations
In today’s business ecosystem, it’s essential for organizations to be able to adapt and innovate as needs change and technology evolves. JumpCloud empowers you to choose the tools that best suit your needs, with the assurance that they will easily connect to your core directory.
Support Article
| Integrating Google Workspace with JumpCloudSupport Article
| Integrating Microsoft 365 with JumpCloudBlog Post
| How to Plan an Active Directory Migration
Vendor Consolidation
JumpCloud’s core directory includes native capabilities covering the workloads you care about most, such as: web application SSO, password management, MFA/2FA, cloud-based LDAP and RADIUS services, SSH key management, cross-OS device management and MDM, identity governance and auditing, and more. JumpCloud is an ideal solution for unifying your existing IT environment, eliminating IT inefficiencies and manual processes, consolidating point solution vendors, and saving you a significant amount of money.
Explore JumpCloud Open Directory Platform Capabilities
Identity Management
Access Management
Device Management







