LDAP is the Lightweight Directory Access Protocol. Developed in 1993, LDAP is still widely used at businesses and organizations worldwide for directory-based authentication.
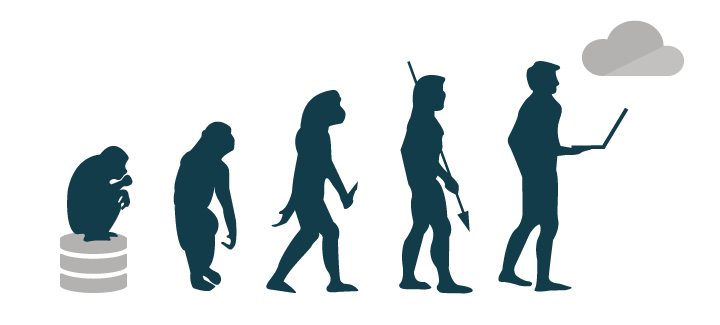
With the changing identity management landscape and all kinds of new, modern authentication protocols, many are wondering if LDAP is still relevant. In this post we’ll start by listing some of the common use cases for LDAP – then we’ll go on to explain how LDAP started and how it has adapted to the changing IT landscape.
We’ll also share where we think LDAP is going: a cloud-based, “LDAP-as-a-Service” approach that enables organizations to leverage the protocol without having to stand up their own LDAP servers.
Use Cases for LDAP
When is it appropriate to use LDAP? While LDAP can be considered a legacy protocol, it is still excellent with authenticating Linux-based applications including many open source solutions. Examples of use cases for authenticating via LDAP include:
- OpenVPN
- Jenkins
- Kubernetes
- Docker
- Atlassian Jira & Confluence
- Linux Samba servers and commercially distributed NAS appliances like Synology or QNAP
This list makes no claims of being comprehensive. In fact, LDAP is such a versatile protocol that we would venture to say there are literally thousands of additional applications that can be integrated using LDAP.
Using LDAP in a Multi-protocol World
In modern IT, how do you implement LDAP? It’s a very good question because every IT resource seems to have its preference for protocol. The result is a need for a variety of authentication protocols, including SAML, RADIUS, OAuth, and others. The downstream impact is that IT admins and DevOps engineers end up needing to separately implement each protocol. This is called “siloed identity management” and it can be very time consuming.
But none of these protocols have completely taken over, so it is critical to have an identity and access management solution that can manage a variety of protocols. We’ll go into further depth at the end about this, but that’s what we’re making at JumpCloud: a cloud-based identity provider that unifies IT resource management by supporting a wide variety of protocols through a single platform.
How LDAP Started
The development of LDAP was arguably the event that kicked off the modern era of identity management. Created by Tim Howes and his colleagues at the University of Michigan, LDAP quickly became a standard authentication protocol.
I was working for the University’s information technology division. The University was mostly on a homegrown mainframe system for email and directory service throughout the campus. I was assigned this project to deploy an X.500 directory for the campus, which I completed. But I quickly learned that it was way too heavy of a protocol and too complicated for the machines that were on most people’s desktops.
“So, LDAP came out of my desire to do something a little lighter weight to accommodate the Macs and PCs that were on everybody’s desktop. Some colleagues and I created a similar protocol called DIXIE, which people liked. Soon after that, I was approached by some people in the IETF community to create a standardized version of DIXIE, and, with the help of a couple of colleagues, that’s how LDAP was born.”
Tim Howes in a 2017 interview
LDAP lived up to its name (lightweight directory access protocol) and would go on to spawn a number of identity providers including OpenLDAP and Microsoft® Active Directory® among many others.
The Impact of LDAP
LDAP began making ripples almost immediately. The protocol spread from the campus of Michigan to enterprises around the world, providing an open source and non-commercialized directory. LDAP offered an avenue for managing open source Linux clusters. At the time (around 1995), these Linux clusters were paving the way and laying the foundation of the rapidly scaling internet. LDAP could mimic SuSe Linux and HP-UX. But where those options were expensive, heavyweight, and commercialized, LDAP was low cost, lightweight, and open source.
While Active Directory became the go-to solution for on-prem, Windows®-based networks, LDAP became ubiquitous with more technical, DevOps infrastructure – servers, Linux/Unix applications, networking equipment, file servers, and more.
LDAP and The Transformation of IT
Over the last decade, the IT landscape has changed dramatically with the addition of cloud infrastructure from AWS®, G Suite™ and Office 365, web applications, Samba file server / NAS appliances, WiFi, macOS® and Linux systems, and much more. Somewhat keeping pace with this shifting landscape has been a plethora of authentication protocols such as SAML, OAuth, OpenID Connect, and many more.
A legacy protocol like LDAP easily could have been forgotten in this transformation, but through it all, LDAP has stayed in use – even at modern, cloud-forward organizations. To simplify a complex situation, the reasons that LDAP has been able to persist are the same reasons that allowed it to catch on in the first place: it’s lightweight, adaptive, and foundational. Inertia is also a powerful factor. Even if organizations would like to move off of LDAP, many don’t because it’s so deeply interwoven into their infrastructure.
Where LDAP is Going
If they don’t already have an existing LDAP implementation, IT organizations generally don’t want to set up an entire LDAP infrastructure just for a handful of applications. Still, they know that connecting those applications and infrastructure to LDAP is critical.
LDAP-as-a-Service has emerged to solve the problem of building dedicated LDAP infrastructure. LDAP-as-a-Service is just one feature of JumpCloud – a cloud-based directory service that securely connects users to their IT resources including systems, applications, files, and networks. JumpCloud’s independent approach means it’s an identity provider designed to work regardless of platform, protocol, provider, and location.
Some of the benefits of leveraging JumpCloud for LDAP include:
- No on-prem servers required – and therefore no configuration or management
- High availability – including automated load balancing, elastic scaling, and redundancy
- Schema compliance – OpenLDAP RFC-2307-based schema and directory structure
- Low latency – regional load balancing to ensure high performance
- LDAPS and Start TLS ensure your data is protected in transit
- Samba file server support – including NAS systems such as Synology, QNAP, and FreeNAS
- Extended user attributes – employee ID, job title, department, location, and more
- Group membership – leverage groupOfNames and memberOf object classes for authorization needs
If you would like to learn more about how managed LDAP may be able to help you with your use case for LDAP, we invite you to take a look at our support documentation on using LDAP-as-a-Service. You’re also welcome to get a demo of the platform or sign up for a trial of JumpCloud to test cloud LDAP out for yourself.





