Modern single sign-on (SSO) is an authentication method that enables users to securely and efficiently authenticate to a variety of IT resources such as networks, devices, servers, applications, and services using a single set of credentials. At JumpCloud®, we refer to modern SSO as True Single Sign-OnTM compared to the traditional and outdated version of web application SSO.
The difference here is that web app SSO only connects users to web apps, while True SSOTM allows users to connect to virtually any IT resource via SSO by a variety of open protocols. This allows IT admins to manage identities and access no matter what resources live within their IT ecosystem. Modern SSO also serves other purposes — it improves security along with user and IT productivity, reduces password fatigue and management, streamlines the user experience, prevents Shadow IT, and more.
In this article, we’ll dive into an overview of how single sign-on works, protocols you need to be aware of, how to choose the protocols you need, and how JumpCloud’s SSO solution works.
How Does SSO Work?
Single sign-on allows users to authenticate to various IT resources with one username and password combination based on a trusted relationship between each resource and an identity provider (IdP). Typically, this relationship’s foundation stems from a certificate that is exchanged between the resource (or service provider (SP)) and the IdP when configuring SSO.
The certificate’s purpose is to create a trust relationship between the SP and the IdP to verify the integrity of the information being exchanged. During the single sign-on process, the identity data being pushed from the IdP to the SP takes the form of tokens which contain identifying bits of information about the user. These tokens can be signed with the certificate used when creating the trust relationship.
When a user signs into an SSO provider’s portal, the IdP tracks that the user is already authenticated, usually via a session cookie. From there, any resource connected via SSO will check with the SSO provider when a user attempts to access that resource. If the IdP verifies the user based on their initial login through the portal, a token will be passed to the resource, and the federated identity is used to complete the sign-in process. However, if the user has not signed in to the main SSO portal or their session has expired, they will be prompted to log in before being granted access to any SSO connected resources.
Different SSO Authentication Protocols
Authentication tokens are a crucial part of the single sign-on process — they enable identity verification to take place separately from other cloud services. These authentication tokens can take different forms while following varying communication standards to ensure validity. One extremely common authentication token standard (also referred to as an authentication protocol) is called Security Assertion Markup Language (SAML), which is used for web app authentication.
A couple other common authentication and/or authorization protocols are the Lightweight Directory Access Protocol (LDAP) and Open Authentication (OAuth2).
How Does LDAP Work Within SSO?
The LDAP protocol was originally designed for facilitating on-prem authentication and other on-prem server processes, and continues to be used to authenticate user access to legacy systems and applications.
When LDAP and SSO are used together, a user enters their credentials and the details of the user’s identity are sent to a security server for authentication. After that, the security server sends the info to the LDAP server which then utilizes the given credentials to attempt to authenticate the user. Essentially, LDAP is an authentication protocol used to cross-check information on the server end.
LDAP is considered a legacy protocol but still has a variety of common use cases including authenticating Linux-based applications, OpenVPN, Jenkins, Kubernetes, Docker, Atlassian Jira and Confluence, and commercially distributed NAS appliances like Synology or QNAP.
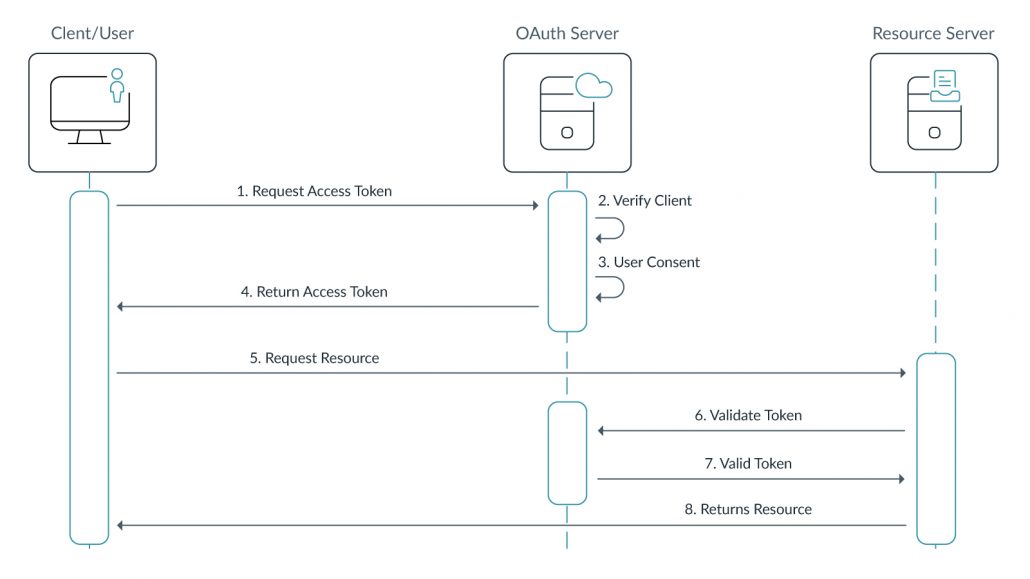
How Does OAuth2 Work Within SSO?
Before we can answer this question, it’s important to call out the difference between authentication and authorization. Authentication has to do with user identity, whereas authorization has to do with user privileges. This is an important distinction to make when discussing OAuth2’s role in web app single sign-on.
While SAML is an authentication protocol that extends user credentials to the cloud and other web applications using the Extensible Markup Language (XML) format, OAuth2 is an authorization protocol that’s more tailored toward access scoping, which is the practice of allowing only the bare minimum of access within the resource/app that an identity requires once verified. OAuth2 is specifically ideal for web and mobile apps and is generally used by the apps themselves in conjunction with an IdP. OAuth2 also allows for sign-in mechanisms like “Sign in with Google,” streamlining the login process even further.
Which SSO Protocol Is Best For Me?
If you’re interested in implementing modern SSO within your organization, you will likely need a variety of protocols depending on the resources that you want to connect via SSO. SAML is a staple protocol across virtually all IT environments, and if you want to connect users to web apps, it will be necessary. OAuth2, used on its own for authentication purposes, can be considered “pseudo authentication,” but is not the most ideal scenario.
However, by using the SAML and OAuth2 protocols in conjunction within a single sign-on framework, you cover all of your bases and allow for more secure authentication and authorization across different apps. If you also need to provide users with efficient access to legacy apps and systems, LDAP needs to be supported by your modern SSO provider as well.
Using a wide range of protocols for SSO is the modern solution to the existing problem of “I want to give my users access to as many IT resources as I can with as little manual work as possible.” This means implementing a combined directory and SSO solution that supports a wide variety of protocols so you have the ability to make use of LDAP, SAML, OAuth, and others such as RADIUS, from one pane of glass.
How JumpCloud’s SSO Authentication Works
JumpCloud built its cloud directory to function as a core cloud identity provider that streamlines IAM and SSO by providing everything under a single platform, including Cloud LDAP; Cloud RADIUS; SAML, SCIM, and JIT capabilities; and more! JumpCloud also has a library of hundreds of pre-configured SAML connectors to make setup easier.
Looking at it from a high level, JumpCloud allows your organization to leverage the major IAM protocols (LDAP, SAML, OAuth2, RADIUS, and more) to authenticate users to virtually any IT resource they need using SSO. Utilizing JumpCloud as your core IdP and SSO solution also limits the amount of work that you have to do with configuration and maintenance. After the initial SSO setup is complete, you can provision individual or groups of users access to the resources they need to get work done, including apps, networks, and more.
How Does SSO Authentication Work with Different Operating Systems?
Using the JumpCloud Directory Platform, SSO can be configured across Windows, Mac, and Linux devices with little to no extra effort. Without a comprehensive IAM and SSO solution in place, cross-OS single sign-on can be difficult to put together and maintain. However, JumpCloud allows you to set up SSO across each OS which facilitates user authentication to virtually any IT resource they need. Our goal is to connect users to their IT resources regardless of operating system, provider, protocol, or location.
Try JumpCloud’s SSO Solution Free
Test out JumpCloud’s modern, simplified IAM solution with True SSO, and see if it’s right for your organization! Create a JumpCloud Free account to access the entirety of the platform for free, up to 10 users and 10 devices. Along with that, enjoy 24×7 in-app support — free for the first 10 days!





