JumpCloud consolidates identity and access management (IAM) with unified endpoint management (UEM). This approach makes it possible to safeguard your most critical assets through a Zero Trust security strategy, all from one console. We’re rolling out enhancements that will enable IT admins to manage their digital estates with JumpCloud, even if they use another identity provider (IdP). This is made possible by federating with upstream IdPs and key advancements to device management. We’re also introducing helpful new automations, workflows, and troubleshooting tools that will improve IT’s overall efficiency.
JumpCloud will soon be more flexible, secure, and user-friendly than ever before. Here’s the recap of what you missed if you didn’t tune into the Q4 product roadmap 2023 webinar.
Open Directory
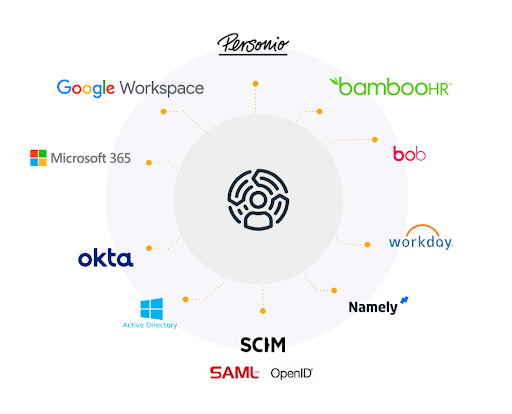
JumpCloud uniquely future-proofs your organization by connecting anything to everything and preventing vendor lock-in with open identity standards. We’re working on the “open” in open directory with the addition of federation, as well as improving interfaces and connectors.
Active Directory Integration
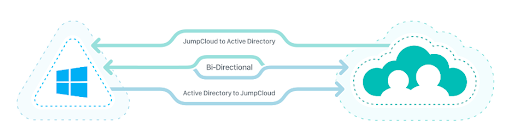
Active Directory (AD) is still widely used on premises, and JumpCloud is embracing AD now and into the future. To date, we’ve delivered powerful integration (bi-directional and password mastery) with the option to deploy agents on member servers in your deployments.
Active Directory Integration (ADI) helps admins to modernize AD while providing a path to fully adopt JumpCloud when the time is right. AD admins retain control while gaining the flexibility of a cloud identity.
Upcoming features include:
- Server 2022 support (EOY)
- AD credential use to access JumpCloud managed resources (2024)
Note: Even more directory connectors will be added in 2024.
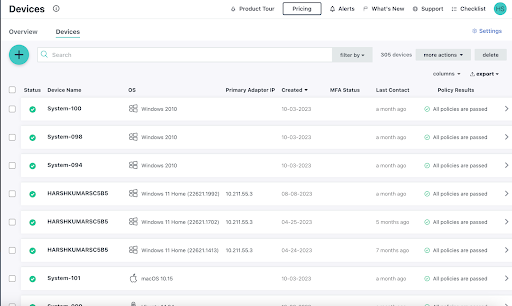
Core Device Management
In Q4 (and beyond), JumpCloud’s open directory platform will bring UEM to Okta users at scale. We’re also working to provide self-service provisioning, introduce a new device login screen experience for Macs and Windows PCs, and advance mobile device management (MDM).
Device as Gateway
Devices are gateways to our jobs. JumpCloud places managed users on managed devices. Today, admins can configure JumpCloud Go, a hardware-bound and phishing-resistant credential, to provide user-friendly passwordless authentication and end multi-factor authentication (MFA) fatigue. JumpCloud Go layers on technologies such as Windows Hello and Apple’s Face ID to provide secure access to privileged and/or standard line-of-business apps.
We’re making that experience even better:
- Step-up MFA will provide an extra layer of protection for privileged resources. Only managed users on managed devices will access the most privileged apps and data.
New Login Screens

We’re introducing a new login experience for JumpCloud managed users on Mac and Windows endpoints. Upcoming capabilities include:
- System diagnostics to troubleshoot issues at login that provides admins with details such as the MAC address, device serial number, and OS versions.
- Wi-Fi control for macOS makes it possible for admins to unlock a machine and change network settings.
- macOS does not support managing network connectivity from the login window
- The JumpCloud macOS login window has an user interface to “Manage Wi-Fi”
Self-Service Account Provisioning
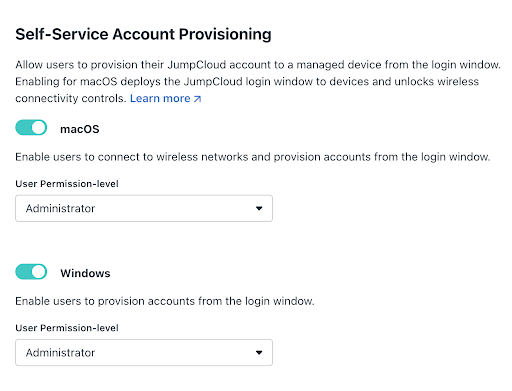
We’re introducing a new account onboarding experience for device and identity management. Users will soon be able to “Sign In With JumpCloud” to auto provision and associate their JumpCloud account to their device with default account permissions. The JumpCloud agent will sync their JumpCloud password back to their device. Previously, admins had to pre-prepare devices and associate users with devices to activate their JumpCloud experience.
Other upcoming features include:
- The ability to take over an existing local Windows account
- Self-service password reset
Note: Scheduled user syncs from Google will eliminate manual processes when admins onboard users from Google Workspace into JumpCloud.
Self-service provisioning is great for shared devices.
Open Directory Federation
JumpCloud will create managed users on managed devices for upstream IdPs. It will soon be possible to use Okta credentials (and MFA) to provision users into JumpCloud. Admins will proceed through the usual process of creating local users on devices with local credentials. Current customers may reach out to their account managers to enroll in the early access program.
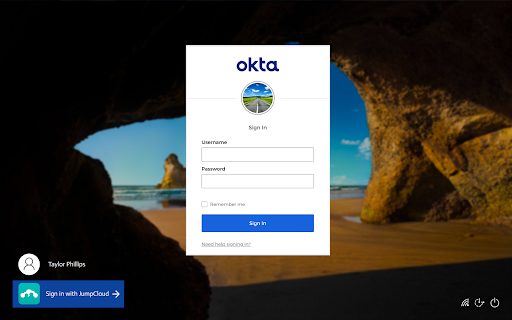
Use Okta for device logins
Note: More IdPs are coming: Google, Azure, and Generic OIDC.
Easy Windows Enrollment
Earlier this year, JumpCloud streamlined how Windows devices that are already in the field are provisioned. We’re now focusing on enabling return-to-service workflows to enroll Windows endpoints through Provisioning Packages (PPKG) created with Windows Configuration Designer (WICD). Packages can be deployed using USB drives or network shares. Admins may also opt to partner with their OEM or contact JumpCloud partners like GroWrk and Hofy to equip remote workers with the devices that they need to start getting work done.
Note: Self-service account provisioning is another great way to enroll new users to devices without having to ship them with a local admin configured ahead of time.
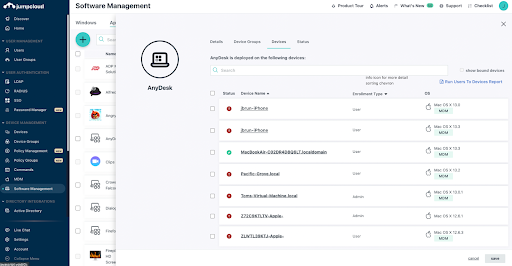
Custom App Repository
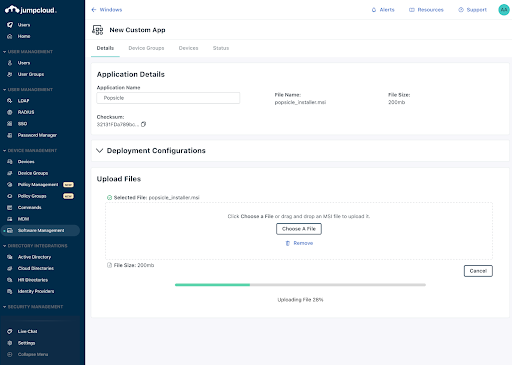
A custom app repository is in early access, and is expected to ship next year. JumpCloud-hosted Windows MSI and Apple PKG files can be uploaded and delivered to assigned managed devices. This approach offers JumpCloud customers more assurance that packages haven’t been modified. Installers are validated through hash values for file integrity. JumpCloud will provide more visibility into installed apps on endpoints over time via app inventories.
Some of its features will include:
- Storage management and file transfer tracking [with GA]
- Uploading creates a ‘version’ and triggers update [post GA]
Note: Chocolatey deprecation: JumpCloud thanks Chocolatey for its support over many years; however, a different solution will be adopted for package and software management throughout the platform. Customers can migrate to self-hosted instances if they choose to.
Advancing Mobile
JumpCloud’s integrated MDM solution is being enhanced for enterprise use cases as well as holistic device management for Zero Trust security and easier employee onboarding.
Android
We’re covering critical enrollment flows for our customers:
- Advanced Android policies will be released on a rolling basis for fully managed devices.
- Android zero-touch enrollment will be available via Enterprise Mobility Management (EMM). This makes it possible to ship devices at scale.
Apple iOS
Deliver company apps safely and quickly to enable a user’s personal device for work while avoiding more direct control over their personal property.
- iOS VPP user enrollment will make it possible for admins to deploy and/or unenroll line-of-business apps from within a secure partition on employee-owned devices. This will include the ability to reclaim software licenses. This will help to ensure that sensitive company data remains private without wiping devices.
- JumpCloud will leverage user enrollments with robust upcoming features next year. Device enrollments in JumpCloud will be backed by managed Apple IDs with federated authentication.
Device Trust for Mobile
Hardware-backed session keys will soon make it possible for organizations to adopt JumpCloud’s Conditional Access rules across all endpoints. Supported devices will include Android and iOS and the scope will include both fully managed and user-enrolled.
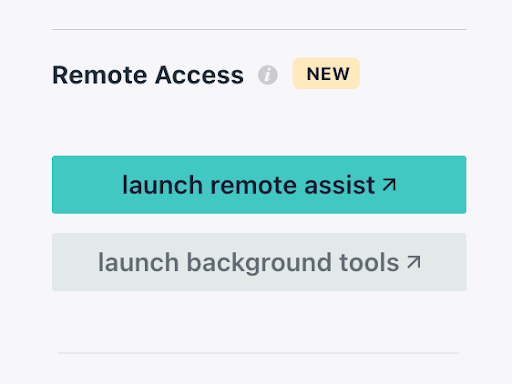
Better Troubleshooting with Background Tools
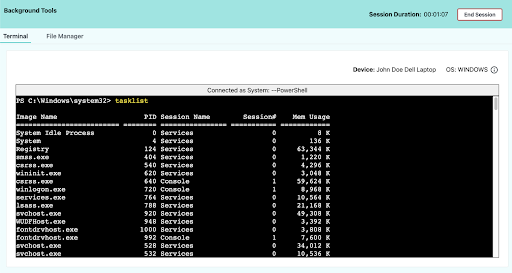
A remote, interactive command line with autocomplete is now available in the Admin Portal, and it has full tab control and ASCII color codes for textual awareness. Note: admins can turn these tools off. Troubleshooting can occur in the background without interrupting users.
Upcoming features for JumpCloud Remote Access include:
- The ability to launch a file manager from your browser
- The ability to transfer large files without FTP, USB, or unsecure apps
Results for Device Policy
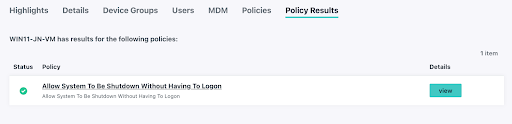
Admins will have visibility into whether policies are pending, failed, or successful. The console will display policy conflicts that require remediation.
Workflow and Automation
Automations and workflows are the underpinnings of “JumpCloud dot next.” Dynamic groups already automatically organize users and devices using basic attributes. The next phase will include operators to create compound queries that will increase admin efficiency and streamline device and identity lifecycles.
It will become possible to take more actions against dynamic groups such as approvals and automating deployments as we enter 2024, especially with HRIS integrations.
Dynamic Groups and Work Orchestration
We’re adding more user and device attributes for users:
- Manager
- Company email
And for devices:
- OS versioning
- Vendor
- Hostname
- IP address
Identity and Authentication
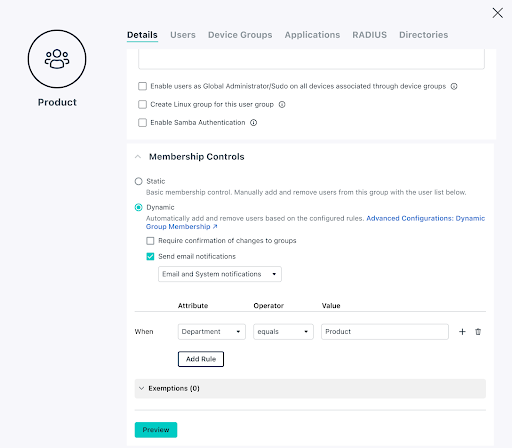
Automated group enrollment for users and devices by setting up rules will be released shortly. More enhanced and granular security controls will be introduced as soon as Q1 of 2024, such as passwords for groups, versus a global policy for all users and groups.
Note: In the future, the user relationship to devices will become clearer.
Platform Enhancements
JumpCloud Password Manager

Many customers use JumpCloud Password Manager (JPM) to share secrets with each other. These use cases are critical for many organizations, and JPM is becoming even more robust.
Improved sync performance and reliability is already rolling out.
Upcoming enhancements include:
- Changes to how device password resets function for improved usability
- An improved desktop and browser extension UI/UX
- The ability to display shared folder activity logs
- The introduction of a Password Manager RPM installer for Linux
If you want to learn more about what’s coming drop us a note or sign up for a free demo. We’d be happy to talk you through the capabilities and solutions that JumpCloud’s open directory platform can provide. Your account manager can sign you up for early access to try out the upcoming features that interest you the most; your feedback will help to shape the product.




