OpenLDAP is open-source software that facilitates LDAP directory creation and management. Because OpenLDAP is open-source, it’s highly flexible, giving it a broad range of applicability; one company’s OpenLDAP instance might look quite different from another’s.
In this blog, we’ll cover some of the most common OpenLDAP use cases, along with some popular tips and tricks for optimizing your OpenLDAP instance.
Because OpenLDAP is an LDAP server implementation, we’ll start with a quick overview of the LDAP protocol to clarify what it can and can’t do.
The LDAP Protocol
To contextualize the use cases of OpenLDAP, let’s first review the main use cases of LDAP (lightweight directory access protocol).
LDAP is a protocol that facilitates directory building, querying, and management. It can also authenticate and authorize users to resources like:
- Technical applications.
- Server infrastructure.
- File servers.
- Networking equipment.
Examples of these resources include:
- OpenVPN
- Jenkins
- Kubernetes
- Docker
- Atlassian Jira & Confluence
- Linux Samba servers
- Synology, QNAP, and other NAS appliances
While LDAP was originally designed before the cloud became common, LDAP can exist as both a cloud-based and on-prem implementation. OpenLDAP follows suit. Note that organizations leveraging LDAP over the public internet need to take the appropriate security precautions.
What Environments Does OpenLDAP Support?
On-Prem OpenLDAP
OpenLDAP was developed over 20 years ago, before the cloud was a business reality. Thus, it was designed to work with on-prem environments. OpenLDAP is still commonly implemented as an on-prem implementation.
In an on-prem OpenLDAP environment, the organization owns the OpenLDAP server and hosts it on premises. This makes the organization responsible for server setup, management, and maintenance, which can be labor-intensive and expensive.
Hosted OpenLDAP
To minimize the burden of owning and hosting directory infrastructure, organizations can run OpenLDAP on a cloud-hosted server.
However, because OpenLDAP is a software but not a service, the organization remains responsible for its uptime, security, and management. A cloud directory like JumpCloud® is a more robust offering that handles these additional elements (as well as many others) for you.
Further, even if OpenLDAP is hosted, it will still run purely on the LDAP protocol, which authenticates users to primarily on-prem resources and those that support LDAP.
Note: Because OpenLDAP software is free, some organizations fail to account for the costs associated with its implementation, management, and maintenance. Whether your organization chooses a hosted or cloud OpenLDAP instance, be sure to factor in overhead costs.
Interacting with OpenLDAP
When it comes to using OpenLDAP, users have a few options for tailoring the experience to their needs and skill level. By default, OpenLDAP offers a command-line interface (CLI) and minimal UI; however, third-party integrations can overlay the software with a GUI. We’ll discuss both options here.
Command-Line

OpenLDAP is designed to function via CLI. Because it is open-source, commands and tools are available online. For example, here’s what it takes to set up OpenLDAP via CLI. This format is the most simplified and leaves OpenLDAP in its most flexible form. It’s ideal for highly technical teams and those that aim to create unique or highly customized configurations.
GUI-Enhanced

You can pair with third-party OpenLDAP web GUI wrappers and front-end managers. For example, phpLDAPadmin is a third-party web app that offers the admin the option to interact with a GUI to access, visualize, and interact with OpenLDAP instead of issuing commands.
This format is common for admins that prefer visual tools over command-line code and teams that need to accommodate those with and without the expertise to use the CLI.
OpenLDAP Directory Instances
OpenLDAP can be used to form an organization’s sole directory, or it can bind with other directories. We’ll discuss both use cases here.
OpenLDAP as the Sole Directory
IT admins can use OpenLDAP to build the organization’s sole directory. In this case, the organization would function on a pure-LDAP directory, and the directory would be able to connect users to the resources that support LDAP. Keeping only one directory ensures resources all point to the same source of truth, which facilitates data integrity and eases integrations and modifications.
However, using OpenLDAP to form your organization’s sole directory will subject it to OpenLDAP’s limitations, which we detail below.
OpenLDAP Bound to Another Directory
An OpenLDAP directory can also bind to another directory or IAM solution like Microsoft Active Directory (AD) or Google Workspace. This expands the organization’s directory capabilities significantly; by binding with a directory that supports other protocols, your organization’s directory is no longer limited to LDAP (as it would be using only OpenLDAP as a directory solution). On the other hand, some organizations may choose to integrate OpenLDAP into an existing directory to add OpenLDAP’s capabilities to their existing solution. For example, OpenLDAP is better-suited to Linux devices than AD; thus, IT might choose to create an OpenLDAP directory and bind it to their existing AD directory.
Without the proper care, however, multiple directories can create data hygiene problems. IT should execute all integrations carefully and maintain one source of truth rather than allowing each to compete with or deviate from one another. Further, binding OpenLDAP with another directory is a highly technical task, and mistakes can be costly. Using one directory is the advised option in many cases; if OpenLDAP is too limited, a more robust directory solution like JumpCloud might be a better fit.
Multiple OpenLDAP Servers
OpenLDAP proxies can direct LDAP queries to more than one OpenLDAP server. This allows organizations to build multi-server directories, which helps with scalability and high availability. It also allows clients to communicate with LDAP servers without needing access to the servers’ details, providing an additional layer of security, and it facilitates load-balancing, data filtering, and failover.
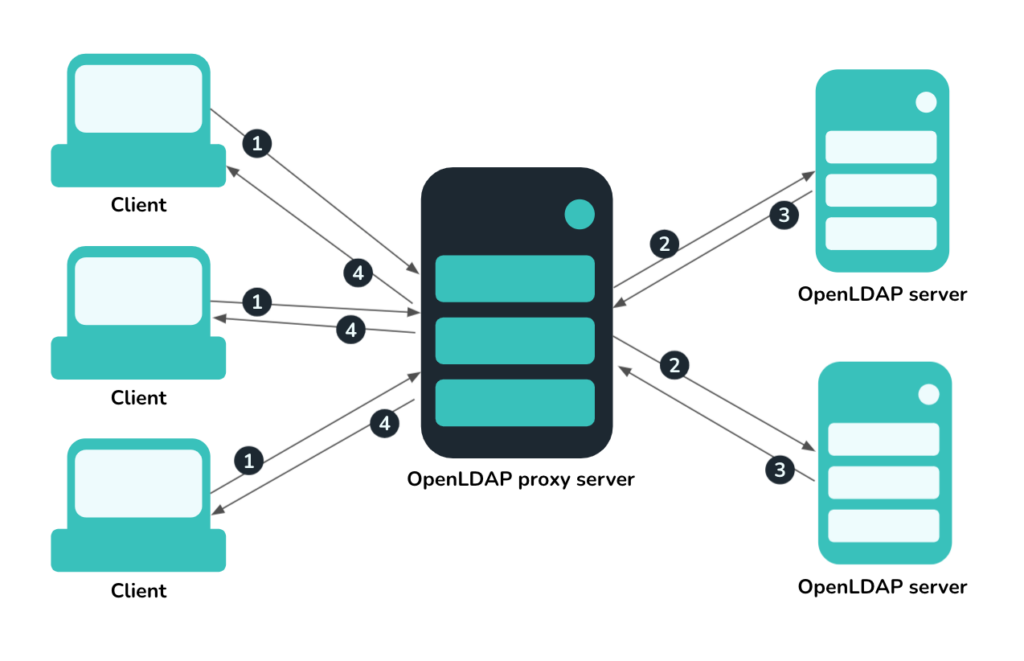
The OpenLDAP proxy can also be used as a backup proxy for non-OpenLDAP directories, like AD.
When Do Businesses Choose OpenLDAP?
OpenLDAP’s strengths lie in its cost, flexibility, scalability, and OS-agnosticism. The businesses that prioritize these benefits are often lean ones with technically savvy IT teams.
Because LDAP works well with many on-prem resources, companies that have on-prem infrastructure or prefer to keep their directory on-prem may opt for OpenLDAP. Businesses often choose hosted OpenLDAP as a free, flexible means of creating a cloud-based directory.
OpenLDAP’s Limitations
OpenLDAP supports a single protocol: LDAP. While LDAP is flexible and OpenLDAP can support a fully fledged LDAP directory, it does not support other protocols.
As business operations, services, and applications migrate to the cloud, the number of authentication protocols different resources may use increases. While some resources still support LDAP, other resources opt for SAML, RADIUS, SCIM, WebAuthn, and others instead. Thus, a directory that’s LDAP-exclusive can’t encompass all the resources in a modern business environment.
A Unified Alternative
The increase in protocol variety and emphasis on the cloud in modern business environments is driving businesses to look to more unified solutions. As such, cloud directories like JumpCloud are becoming popular alternatives to OpenLDAP.
Cloud directories take a multi-protocol approach, allowing them to authenticate and authorize users to many different types of resources. JumpCloud, for example, supports so many protocols that it can connect users with virtually all the resources they need.
To learn more about how a cloud-based directory might be a viable OpenLDAP alternative for your business, download the whitepaper, It’s Time for a New Cloud Directory Platform.




