When you assess your devices’ health and security, a key data point to monitor is the software installed on each end user machine.
It’s possible in Active Directory® (AD) to pull reports on Windows® machines by crafting a PowerShell script, but the same isn’t true for other operating systems, like macOS®. Whether you use AD or other system management tools, it’s worth examining whether you can centrally manage and monitor all machines across your organization, regardless of operating system.
Here’s why you should monitor installed applications — and how to do it from a single platform.
Why to List Installed Applications
Here are a few reasons to list installed applications on your users’ macOS and Windows machines:
- Maintain security: Ensure users have only downloaded approved applications on their machines, and verify that those applications are up-to-date. This information can help you respond to and mitigate zero-day vulnerabilities like Zoom’s.
- Troubleshoot user issues: Particularly as more users work outside the office, you need to have a strategy for remote troubleshooting. Installed applications might affect machine performance, like CPU.
- Track licenses: By monitoring installed applications, you can track license usage and make sure that licenses aren’t going to users who don’t need them.
A Cross-OS Monitoring Solution
Often IT administrators use different point solutions to manage their macOS and Windows machines. However, JumpCloud® offers a comprehensive cloud directory platform you can use to manage user identities, access, and devices — including macOS, Windows, and Linux® machines.
JumpCloud also offers a premium feature called System Insights™, which returns key system telemetry about hardware, software, and network configurations across end user devices. The data is available directly in the web-based Admin Portal, as well as via API calls.
This includes installed applications on macOS machines and installed programs on Windows machines, as well as their version and last open date. Here’s a view in the Admin Portal for one user’s machine:
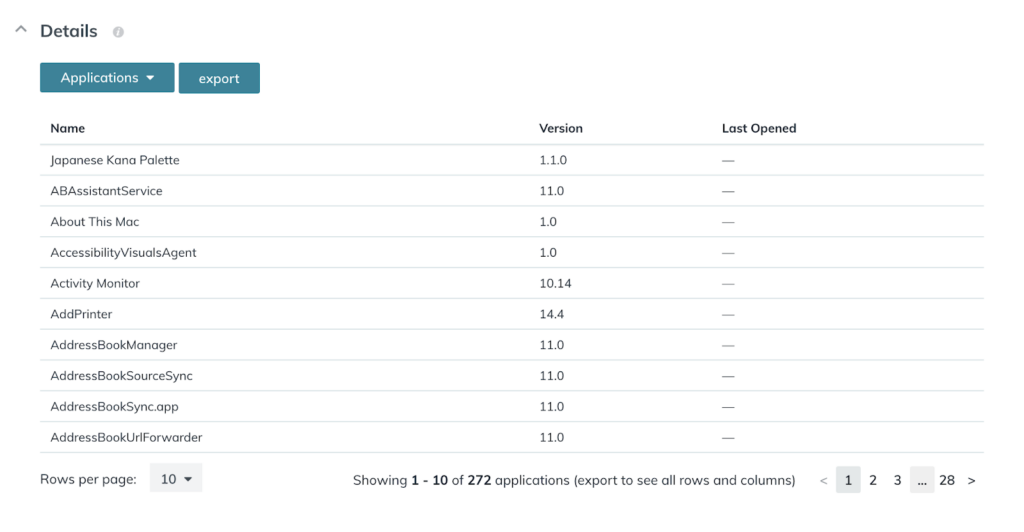
Other software data points include Chrome extensions and Python packages across macOS, Windows, and Linux machines — as well as a wide breadth of data points about hardware and network configurations.
System Insights at Work
The IT team at Chase International allows remote users to fill out a form if they need to download new software or a Google Chrome extension and grants those users brief administrative access on their machines to make approved downloads. The IT admins then run a System Insights report to ensure users didn’t download anything unapproved. Read more about how the team at Chase International uses JumpCloud to manage and monitor remote users and devices.
You can also sign up for a no-obligation JumpCloud Free account and test the platform’s full functionality, including System Insights, for up to 10 users and 10 devices entirely free. Use 10 days of free in-app chat support with our support engineers to get the most out of your first days in your new account.




