JumpCloud's Cloud LDAP allows users to connect using StartTLS (ldap://ldap.jumpcloud.com:389) or TLS / SSL (ldaps://ldap.jumpcloud.com:636). Many client applications/appliances require you to upload a Peer Certificate Authority when connecting to TLS / SSL. You can run the following commands from a Mac, Windows, or Linux terminal to acquire this at any time.
You can acquire two types of certificates:
- Certificate Chain: This includes the Root, Intermediate, and Server certificates. This is typically what most applications require.
- Server Certificate: This is the leaf certificate provided by JumpCloud.
OpenSSL is not pre-installed on Windows machines. Jump to Using OpenSSL on Windows to learn more.
Using OpenSSL on Linux or macOS
Run the following command to output the certificate authority to the /tmp/ directory as jumpcloud.chain.pem.
echo -n | openssl s_client -connect ldap.jumpcloud.com:636 -showcerts | sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > /tmp/jumpcloud.chain.pem
Run the following command to output only the JumpCloud LDAP Server certificate to the /tmp/ directory as jumpcloud.ldap.pem.
echo -n | openssl s_client -connect ldap.jumpcloud.com:636 | sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > /tmp/jumpcloud.ldap.pem
The certificates are signed by GoDaddy. Depending on the LDAP client configuration requirements, the GoDaddy Root CA and Intermediate CA certificates may need to be saved to the local Trusted Root Certificate store. Both of these certificates can be obtained from the GoDaddy website repository.
Using OpenSSL on Windows
OpenSSL is not pre-installed on Windows devices. To collect certificates, you'll need to download and install it and then use the following commands.
To install OpenSSL on Windows:
- On a Windows device, download and run the OpenSSL Installer for Windows: Win32/Win64 OpenSSL Installer for Windows - Shining Light Productions.
- After installing OpenSSL, add the OpenSSL path in Windows Environment Variables:
- Go to System Properties > Advanced > Environment Variables.
- Under System Variables, select Path from the list and then click Edit. A window appears with a list of directory paths.
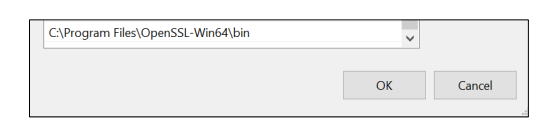
- Click New and enter the directory path to the OpenSSL bin folder. See the following example for reference.
Your OpenSSL path may differ from the above screenshot.
After installing and configuring OpenSSL on Windows, you can now run the following commands to collect the certificate details.
To collect certificates using OpenSSL on Windows:
- Open Command Prompt and run one of the following commands:
- To get the certificate chain, run:
openssl s_client -connect ldap.jumpcloud.com:636 -showcerts - To get only the server certificate, run:
openssl s_client -connect ldap.jumpcloud.com:636
- To get the certificate chain, run:
- In the output, copy the text from -----BEGIN CERTIFICATE----- to -----END CERTIFICATE----- including the headers.
- Paste the certificate details in to a plain text file (for example, Notepad) and save the file with the appropriate .pem extension:
- For the certificate chain, save the file as: jumpcloud.chain.pem
- For the server certificate, save the file as: jumpcloud.ldap.pem
LDAP Client Certificate Configuration Examples
Softerra LDAP Browser Certificate Store
This LDAP client has a Certificate Store that you can use to upload Trusted Root Certificate Authorities and Intermediate Certificate Authorities. Many clients only provide a single Trusted Root Certificate store. See your vendor documentation for details on the required client configuration and certificate format(s) accepted.
Duo Directory Sync LDAP Certificate Chain
The Duo Directory Synchronization configuration requires you to enter the full PEM formatted certificate chain in the SSL CA Certs section. The full PEM formatted certificate chain contents can be acquired using the first command mentioned at the beginning of this article. The command outputs a file called ‘jumpcloud.chain.pem’, which contains all certificates and includes the -----BEGIN CERTIFICATE----- and -----END CERTIFICATE----- references for each certificate in the chain.