Identity Lifecycle Management
Centralized, and automated identity and access management, from day one of employment throughout their entire tenure with your organization.
Secure and Automated Identity Management
Identity lifecycle management (ILM) is often done via multiple tools and disconnected processes spanning across HR and IT. However, JumpCloud centrally manages one identity and one set of credentials per user — unify and automate identity creation and deactivation, as well as access provisioning and deprovisioning.
Unified On- and Off-boarding
Automate identity creation, access changes, and identity and access termination throughout the identity lifecycle. Connect HR tools or an existing on-prem or cloud directory to JumpCloud to unify and streamline identity lifecycle management tasks.
Blog Post
| What is Identity Lifecycle Management?Video
| Remote Onboarding With JumpCloudBlog Post
| Improper Offboarding Poses Significant Security Risks
Easily Manage Hybrid Users
JumpCloud leverages cloud infrastructure to provide full remote control over identity lifecycles, no matter where users are located. Use JumpCloud on its own, or connect it to other tools in your environment for a seamless admin and end-user experience.
Whitepaper
| Building a Bridge Between HR and ITWebinar
| MSP Demo: Onboard a New End-Client Employee in 90 SecondsBlog Post
| 6 Easy Ways to Enhance Employee Experience Through IT

Secure Identities and Access
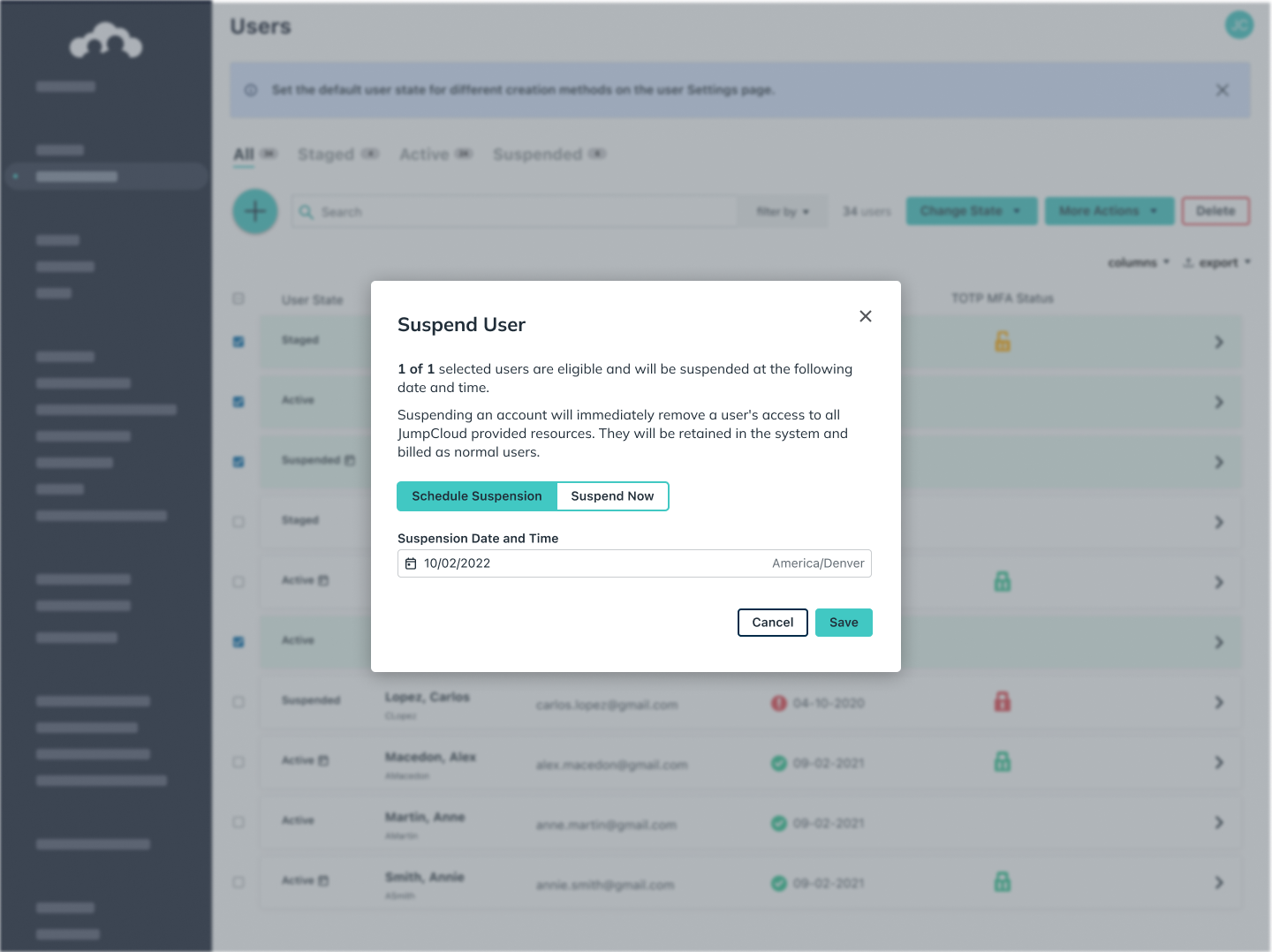
Use group-based access control, including dynamic groups, to grant users access to their resources. On departure, suspend their account and resource access. Layer with MFA, conditional access, and SSO across identities for consistent identity protection.
Webinar
| Practical Tips for Managing the User Identity Life CycleSupport Article
| Getting Started: Conditional Access PoliciesSolutions
| Secure Password Management with IdentityOS®

Explore JumpCloud Open Directory Platform Capabilities
Identity Management
Access Management
Device Management







