Key Takeaways
- TOTP MFA generates time-based one-time passwords directly on a user’s smartphone, creating codes that refresh every 30-60 seconds and fall under the “something you have” authentication factor, requiring both compromised credentials and physical device access for account takeover.
- TOTP MFA blocks 76% of targeted attacks and 100% of bulk phishing attempts, according to Google Security research, making it one of the most effective authentication methods against unauthorized access.
- TOTP MFA offers stronger security than SMS-based authentication, as codes are generated locally on the device rather than transmitted via text message, eliminating risks from SMS interception, carrier vulnerabilities, and insider routing attacks.
- JumpCloud’s cloud directory service enables TOTP MFA deployment across all IT resources—including systems, applications, infrastructure, and networks—regardless of platform, protocol, provider, or location, with centralized configuration.
- 80% of recent data breaches could have been prevented with MFA implementation, as compromised credentials remain the leading source of security breaches and MFA serves as a critical barrier between attackers and organizational data.
What is MFA?
Organizations concerned about identity security need to make multi-factor authentication (MFA) a standard practice for their users. MFA is one of the most effective security methods for blocking unauthorized account takeovers. There are several types of MFA, but before we talk about TOTP MFA specifically, let’s talk about MFA in general and why it’s so effective at securing user accounts.
MFA (also called two-factor authentication or 2FA) is the practice of requiring additional authentication factors beyond the standard username-password combination most authentication mechanisms require.
If that credential combo is compromised for any reason, MFA acts as the final barrier between an attacker and their prize: the critical data housed within an organization’s network. Since compromised credentials are the leading source of breaches, an additional layer of security through MFA works wonders. In fact, Symantec found that 80% of recent breaches could have been prevented with the addition of MFA.
Because of its additional factors, MFA helps to fully authenticate that a user requesting access is who they say they are. These factors are colloquially referred to as “something you have, something you know, or something you are” (e.g., an MFA token, password, or biometric information, etc.).
Additionally, login time and location can also be used as authentication factors. In practice, each should be individualized and mutually exclusive, meaning that compromising one factor doesn’t compromise the others, thus making the possibility of taking over a user’s account significantly more difficult for a bad actor.
What is TOTP MFA?
TOTP (Time-based, One-Time Password) is a form of MFA that uses a randomly generated code as an additional authentication token. TOTP MFA codes are generally created via a smartphone app (e.g. Google Authenticator), so it falls under the “something you have” classification.
As the name suggests, each TOTP code is only valid for a short amount of time and constantly refreshed, meaning that the perpetrator of a breach would need both a user’s compromised credentials and direct access to their phone in order to take over their account. From a security standpoint, TOTP adds a sizable buffer between an organization and a breach.
Regarding end user experience, however, TOTP is sometimes met with consternation. MFA already adds an extra step for users by default, and TOTP can introduce the challenge of inputting the code only for it to expire right before you submit. In comparison to other forms of MFA, however, TOTP is both fairly lightweight and effective.
Comparing TOTP to Other Popular Forms of MFA
SMS-based MFA
SMS-based MFA uses codes similar in structure to those of TOTP, except instead of being generated directly on a smartphone, they’re sent via SMS text message, which means they’re being created outside of the device. Although usually generated by a trustable source, an insider attacker could potentially route the code to themselves.
Additionally, SMS codes often last longer than TOTP codes. While this makes them easier to leverage by end users, intercepted SMS codes give a wider time frame for bad actors as well. As such, many consider SMS to be one of the least secure methods of MFA.
Physical Key
Physical MFA devices use a hardware token as the secondary authentication factor, such as a USB device. Since it requires direct possession of the authentication token, physical key MFA is considered the most secure of the available forms of MFA.
Unfortunately, setting up unique physical keys for every member of an organization can be incredibly time consuming for already-busy IT admins. In addition, physical keys have a higher potential of becoming lost in the daily hustle and bustle, and if stolen, can spell disaster for an organization.
Push Notification MFA
Probably the most convenient form of MFA available, push notification MFA leverages a pop-up message on a user’s smartphone which allows them to confirm or deny access with the push of a button. Push MFA also alerts the associated user of the time and origin of the access request, meaning they are instantly aware if another entity is attempting to breach their account.
The main drawback of push notification MFA is the fact that organizations are required to purchase the service/application needed to do so. TOTP-generating apps, on the other hand, are often freely available. For budget-conscious organizations, push notification MFA may not be worth the convenience compared to its effects on the bottom line.
Biometrics
The most futuristic form of MFA, biometrics uses fingerprints, retinas, faces, or even voices as the additional authentication factor, and is the main “something you are” form of MFA. It goes without saying that biometrics are the most personalized MFA method, making them highly secure.
Unlike the other methods, however, biometric MFA is the least developed of the group, meaning that implementations of it at enterprise scale are few and far between. Beyond that, there are some potential disadvantages to biometric authentication, such as the fact that new deepfake technologies and other imitation games may provide hackers a backdoor method to a person’s physical identity, allowing them into an account unhindered.
By the Numbers
To wrap up this comparison of MFA forms, let’s look at a recent study by Google’s Security Blog on the efficacy of popular forms of MFA:
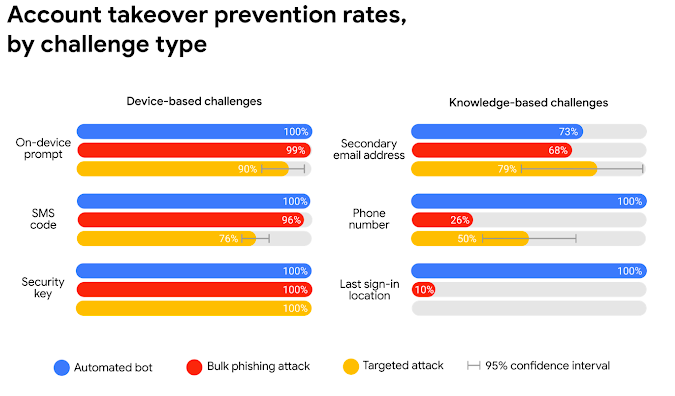
As you can see, TOTP MFA (which falls under “On-device Prompt”) is incredibly effective at safeguarding accounts from the effects of an attempted hack. Armed with this knowledge, the challenge then becomes how to implement TOTP at scale.
TOTP MFA Everywhere
There is a solution for organizations who need to enable MFA across all facets of their IT environment. A cloud directory service can enable TOTP MFA on systems, applications, infrastructure, and networks with just a few clicks. That’s virtually all IT resources, regardless of platform, protocol, provider, or location, backed by one of the top forms of MFA.
To learn more about TOTP MFA everywhere, consider reading how a cloud directory service can help in our Security Playbook for SaaS Startups whitepaper.




