Security-minded system administrators prioritize taking all the necessary measures to safeguard confidential and protected data. The compromise of a device can prove costly if it contains sensitive company information, especially when organizations have compliance requirements. Disk encryption is one of the best ways to mitigate this risk.
Encryption is the process of encoding data. Data is converted from plain text to ciphertext using a special mathematical algorithm that renders the data unreadable unless the encryption key is provided. This key should always remain a secret to the person authorized to access the data.
There are two major types of encryption in a computer: Full Disk Encryption (FDE) and File Level Encryption (FLE).
Full Disk Encryption
In full disk encryption, also known as hard drive encryption, the entire hard drive or volume — including all the files — is protected. During booting, a passphrase or secret key is required to unlock the drive before logging in with your user account credentials.
Implementing FDE guarantees data privacy and security for all the files from unauthorized users or anyone with malicious intent. Learn more about the benefits of FDE, and five reasons you should consider requiring it in your organization.
File Level Encryption
As the name infers, file level encryption happens at the file system level. This type of encryption targets individual files and directories, but not the entire hard disk.
Both full disk encryption and file level encryption can be used simultaneously to achieve a higher level of data protection.
In this tutorial, we will focus on how to enable full disk encryption on Ubuntu 22.04 using LUKS.
What Is Linux Unified Key Setup (LUKS)?
LUKS is a standard hard drive encryption technology for major Linux systems including Ubuntu. It is a platform-independent disk encryption specification and the de facto disk encryption standard for Linux systems.
LUKS was originally developed for Linux systems and is used in nearly all Linux distributions. It is also a popular encryption format for network-attached storage (NAS) devices. It encrypts entire block devices, making it an ideal choice for encrypting SSD, hard disk drives, and even removable drives.
In addition to offering FDE, LUKS allows users to create and run encrypted containers with the same level of protection as LUKS full disk encryption.
With LUKS, disk encryption can be enabled during the installation of an operating system. In fact, full disk encryption is only achieved during the installation of the Ubuntu Desktop operating system. It encrypts all the partitions including swap space, system partitions, and every bit of data stored on the block volume with the exception of the Master Boot Record (MBR).
How to Fully Encrypt Data on Ubuntu 22.04
If you already have a running instance of Ubuntu 22.04 and you want to enable full disk encryption, you’re required to reinstall it. You cannot fully encrypt it once it is installed. You can only encrypt directories or partitions post-installation.
If you forget your encryption passphrase, all your data will be inaccessible. As such, it is recommended to pick one that you can easily remember or store on a password vault or manager. Better yet, if you have used a complex password, you can note it down somewhere and keep it under lock and key.
Additionally, before starting this process, be sure to backup any critical data that could potentially be lost during the reinstallation process.
Getting Started
We will skip the few installation steps on Ubuntu 22.04 and head straight to the “Installation Type” step that requires you to select your preferred disk partition mode.
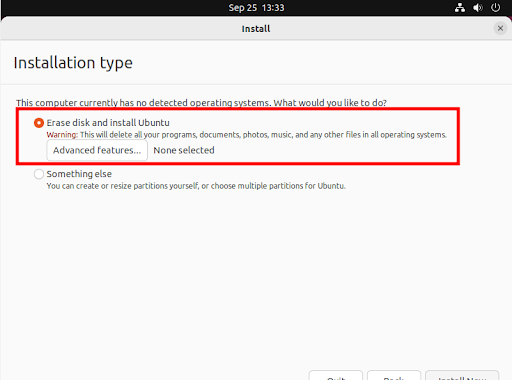
Two options will be presented. The first one (the default option) is “Erase disk and install Ubuntu” which wipes out all the existing data and automatically partitions the drive. The second option is “Something else” which is used to manually configure the disk partitions yourself. Please note that you will not be able to enable full disk encryption by selecting the second option.
Select the first option: “Erase disk and install Ubuntu” and click the “Advanced features” button as indicated.
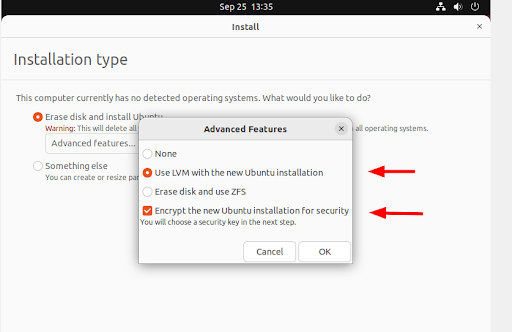
Once you click the “Advanced features” button, a pop-up appears. Be sure to select “Use LVM with new Ubuntu installation” and the “Encrypt the new Ubuntu installation for security” options.
Then click “OK.”
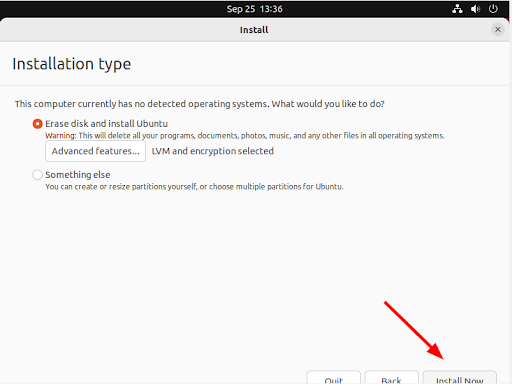
Next, assuming you have already backed up any important data, click “Install Now.”
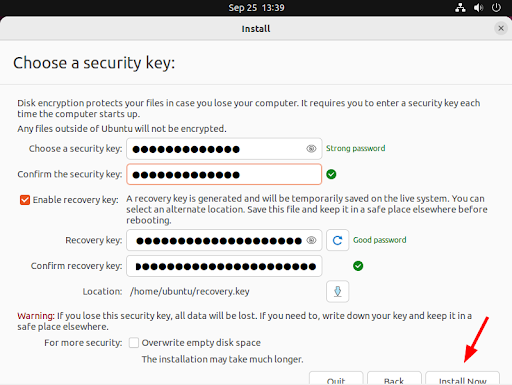
Disk encryption requires a security key in order to access your files each time your device boots. In this step, provide a strong security key or passphrase.
You can also enable a recovery key which enables a user to access the encrypted disk if they forget their password, or if the disk needs to be installed on a new device.
Then click “Install Now.”
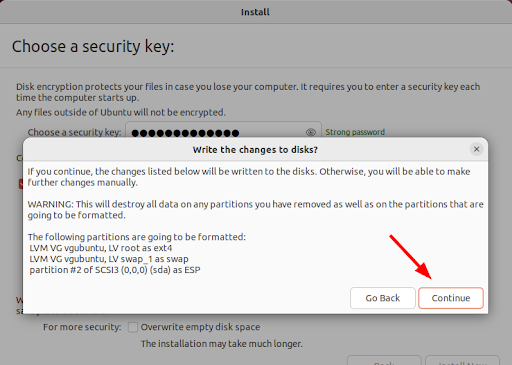
On the pop-up dialogue that appears, click “Continue” to write changes to the disk.
From here, continue with the installation process until the end, and finally, reboot the system. Provide the security key that you generated and hit ENTER prior to logging in.

The secret key unlocks your drive thereby granting you access to your system.

From here, you can log in to your new Ubuntu installation by providing your user account’s password and pressing ENTER.
Conclusion
In this guide, we walked you through the implementation of full disk encryption using LUKS on Ubuntu 22.04. FDE provides a robust way to safeguard your data in case of theft or accidental loss of your device.
Encryption is just one approach to ensuring the privacy and safety of your data. Therefore, you should not relax enforcing other data protection measures such as firewalls, identity and access management (IAM), and Zero Trust controls such as multi-factor authentication (MFA).
JumpCloud’s open directory platform is available to easily implement full disk encryption throughout your entire fleet. Pre-built policies make it possible to achieve full disk encryption for Windows and macOS devices, with granular control and visibility for BitLocker.
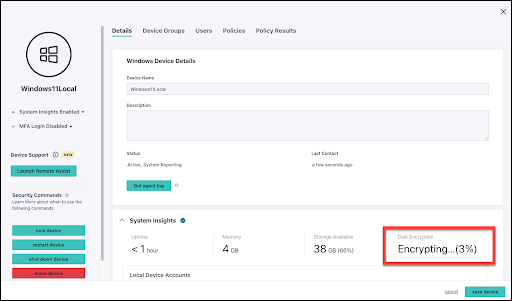
Linux devices can also be managed and monitored for encryption status. To see how this works, along with a number of other device security and management features, sign up today to get started.



