Updated on April 8, 2024
Today, identity federation is a given for every mid-market or enterprise organization — extending users’ digital identities in ways that preserve a company’s security and maximize employee effectiveness. But traditional identity federation services are breaking down.
In an Active Directory (AD) environment, every new cloud-based SaaS application comes with a new flavor of identity federation services. Many IT and MSP teams have poured hours into creating their own patchwork solutions to manage the resulting complex web of identity federation services and their extensions.
And these solutions are just band-aids that present major risks to security and compliance. One misstep could cause an outage, breach, or major data loss. And that doesn’t even begin to address identity management on corporate devices.
To better understand how modern federated identity management (FIM) can improve IT and MSP workflows while safeguarding company data and devices, we have to go back to the basics.
In this post, we’ll refresh your memory on identity federation services, explaining what they are and how they work. Then, we’ll explore how modern IT and MSP teams are embracing all-in-one FIM, MFA, MDM, and patch management platforms to centralize and secure their backend operations.
Understanding Identity Federation
Identity federation is a way of recognizing and connecting a user’s identity across an organization’s identity management systems. In practice, this means users only have to log in one time to gain access to multiple other applications. Identity federation involves:
- Authentication to confirm users are who they say they are.
- Authorization to confirm users should have permission to specific resources.
- Access control to grant users permission to each downstream system.
As you might expect, identity federation services are a category of identity management solutions that propagate users’ digital identities to web applications, cloud servers, and other back-end systems. They establish communication with identity providers (IdPs), which store and manage the user identities checked through authentication, authorization, and access control, and service providers — the applications users need to do their jobs. More on that next.
Popular examples of identity federation services include single sign-on (SSO) solutions, privileged identity management, and directory extensions. Identity federation services are typically layered on top of legacy identity management solutions — like Microsoft Active Directory (AD) — to push traditional user identities to non-Windows or cloud-based IT resources.
Benefits of Identity Federation
Identity federation confers numerous advantages, mostly in terms of security. Without FIM, users have to remember their login credentials when accessing every single application every single time. As you can imagine, this often causes users to reuse passwords or create ones that are easy to hack, opening the door to cyberattacks.
But there are two other main benefits of FIM:
- Improved user experience. With FIM, users can type in their credentials once to access multiple applications instead of memorizing multiple passwords. They can also feel confident that they are securely sharing information with other colleagues — those peers must be federated to access it.
- IT cost reduction. Rather than trying to manage a long list of different add-ons, IT teams can use one FIM solution to set and update permissions. It saves IT from paying for several add-ons and frees up their time to work on other strategic initiatives.
How Does Identity Federation Work?
As mentioned above, identity federation is based on mutual trust between an identity provider (IdP) and a service provider (SP). Let’s break down each of these terms in more detail.
Mutual Trust
In the context of identity federation, mutual trust basically means authentication. The service provider needs to know that the user attempting to access a protected resource is who they say they are and are approved to use it. Identity providers perform that spot check and authenticate users. Standard protocols used in identity federation include:
- SAML, which streamlines user authentication by using Extensible Markup Language (XML) to communicate with other systems.
- OAuth, an authorization framework ideal for APIs.
- OpenID Connect, an interoperable authentication protocol that’s based on OAuth.
IdPs
Identity providers create and manage user identities. IdPs verify the user’s identity, authenticate the user, and send the user’s data to the service provider.
Service Providers
Service providers, SPs for short, are web-based solutions that could be anything from an email platform to a CRM, to an ERP, or more privileged resources like remote servers, databases, and network equipment. SPs are connected to identity providers in order to validate the user’s identity and permissions.
When someone attempts to access a service provider, the SP looks to the IdP to confirm the user’s identity, establish mutual trust, and then send the appropriate user information to finalize the login process.
Is Identity Federation the Same as SSO?
SSO and FIM are very similar. Both enable users to use one set of credentials to access many different company tools. But SSO only allows users to access multiple applications within the same enterprise or domain.
FIM takes this concept to the next level, allowing users to access applications across multiple domains, depending on the federated configuration. FIM uses SSO technology to authenticate those users. So implementing FIM means you’re also using SSO, but implementing SSO doesn’t mean you’re using FIM.
Implementing Identity Federation
Before implementing an identity federation solution, it’s important to take a step back and think through your requirements. Every company has its own unique identity federation use cases, integration needs, and preferred mechanisms for IT and MSP configuration and oversight. Take a moment to write these down before going into an evaluation.
If you’re stuck, here are some basic requirements every company should consider:
- Security and compliance. Many organizations have to comply with GDPR, CCPA, and uphold other standards like SOC 2 and PCI. Look for solutions with extensive logging, automated notifications for suspicious activity, and reporting capabilities.
- Integrations. If it can’t natively integrate with your platforms, databases, and existing IT infrastructure, you have to build your own custom integrations, which take time to develop and may have security gaps.
- Intuitiveness. If it’s not easy for end users to adopt, they simply won’t use it. And if they have to memorize passwords, you’re basically asking for some kind of security or compliance incident.
- Scalability. This is especially important for mid-market and enterprise companies looking to expand to new markets and geos. Finding an FIM tool that complements your existing IT or MSP tech stack is a boon — that way, you can control and update everything in one place.
Once you’ve decided on an FIM solution, you’ll need to:
- Set up your identity provider.
- Implement your authentication platform.
- Integrate your FIM solution with your identity provider, your authentication platform, and each of your major service providers.
- You’ll need to make sure that there is a button on each application that gives end users the choice to sign in with a federated IdP on the login page.
- Ensure meaningful trust has been established among all of your service providers.
A key consideration for successful implementation of a new FIM solution is the employee login experience. You’ll want to think about:
- Which tools own the authentication experience?
- What screen(s) do you want users to see?
- Will there be a confusing change of logos or platforms?
- Do you already have conditional access policies set up?
- Where do you want your MFA policies to live?
- Are there ways you can streamline the login process?
Lastly, you’ll need to train end users. Announcing the new FIM solution at all-hands meetings, hosting lunch & learns for each department, and incorporating training into new hire onboarding are good ways to communicate what your new FIM is, how it works, and who employees can contact with issues or questions.
Challenges and Considerations
When implemented thoughtfully, identity federation should greatly improve security. A holistic, centralized mechanism for controlling access to various systems makes it more challenging for cyberattackers to penetrate the domain.
However, FIM is only as secure as the permissions it sets.
IT and MSP teams are still responsible for creating and updating security mappings for different types of employees or contractors. That task becomes even trickier when balancing multiple federations. Any mishaps during implementation or maintenance can lead to compliance breaches, data leaks, and criminal activity — a far higher risk in companies still using outdated identity federation techniques atop Active Directory.
Even if you have solid IdP and SSO solutions and feel confident in your FIM integrations, you’re still missing one critical piece of the security puzzle: device management. Finding an MDM that’s (1) aware of end user identities and (2) plays nicely with your existing tech stack is a challenge in and of itself. Once implemented, it just becomes one more thing for IT and MSP teams to manage.
Identity Federation With JumpCloud
Fortunately, there’s a next-generation cloud identity federation service that can securely manage and connect users to virtually any IT resource — and it’s not Microsoft Active Directory.
It’s JumpCloud. JumpCloud is a modern, identity-as-a-service (IDaaS) platform that covers virtually all identity federation use cases IT and MSP teams need, using core protocols like LDAP, SAML, RADIUS, SSH, and REST to connect users to resources on-premises or in the cloud. With an open cloud directory, native MDM, MFA, real-time event logs, and multi-OS support, JumpCloud is a one-stop shop for user, device, and identity management.
JumpCloud’s Federated Authentication feature also provides authentication and authorization pathways to third-party IdPs, giving IT admins, MSP firms, and employees more flexibility:
- End users can add themselves to a device using an upstream IdP they already know and understand while JumpCloud handles authorization, including any step-up multi-factor authentication or other IdP-supported processes.
- IT and MSP teams can provision user and device permissions during new hire setup, using JumpCloud to facilitate communications between IdPs, SSO solutions, and devices.
- JumpCloud can refer users through an upstream IdP to run double security checks or conditional access for key resources.
The best part? It’s completely plug-and-play, meaning an MSP’s customers don’t have to transfer IdPs to leverage JumpCloud as either a point or platform solution.
Embracing the Future of Identity Management
The JumpCloud Directory Platform® gives IT and MSP teams all-in-one access control from within the cloud, federating user identities from one centralized location. With JumpCloud in place, IT can easily manage user access to devices and resources through Windows, Mac, and Linux authentication and direct integrations with Google Workspace, Microsoft 365, and HRIS platforms. And with no on-premises hardware, JumpCloud setup is a breeze.
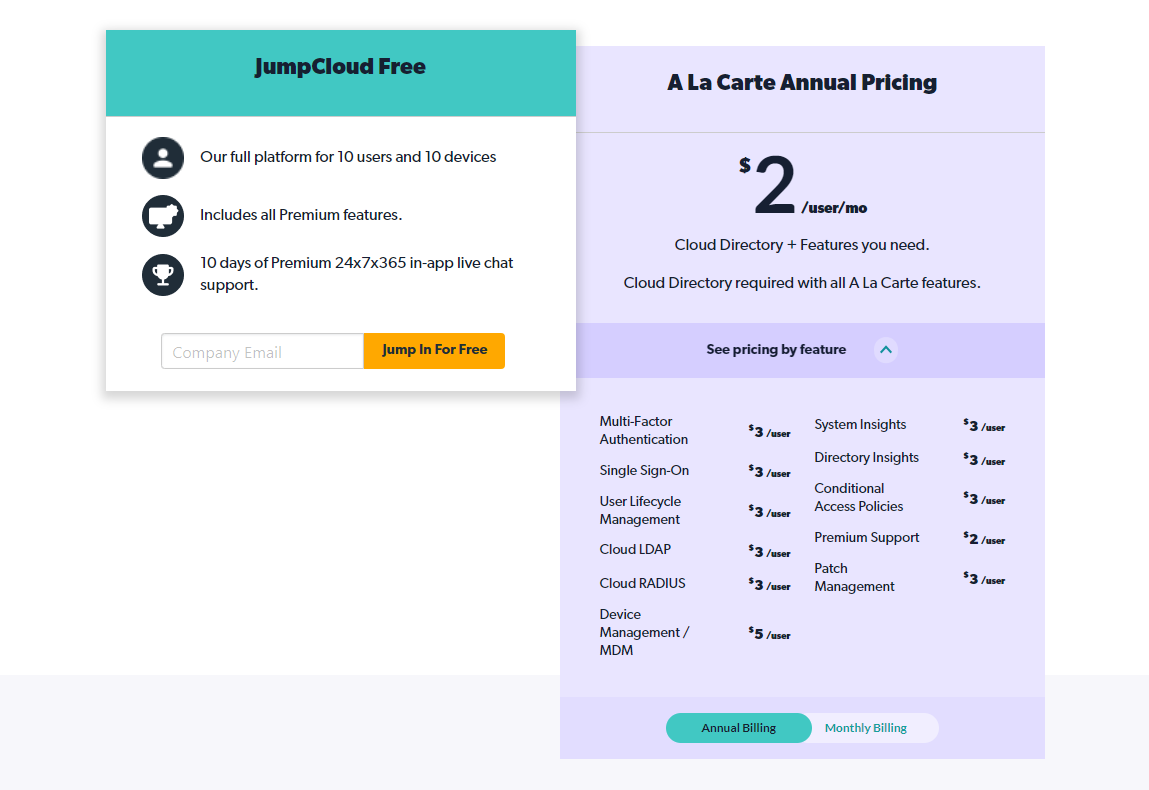
For MSPs, JumpCloud consolidates all client identity federation and device management services into a single pane of glass, enabling a more productive workflow. IT admins can expect dramatically reduced overall costs, giving them more budget for other strategic tools and the time to implement them.
So what are you waiting for? Sign up for a trial of JumpCloud today to see its power for yourself.