Updated on August 15, 2024
Managing Linux devices is a demanding challenge facing many of today’s IT organizations. IT and DevOps personnel need to ensure that each Linux system and server is patched, log files are rotated, the right users are on each device, processes are functioning as intended, and more.
In fact, with Linux desktop variants dramatically impacting the market (positively), IT admins need to consider this OS as a core part of their device fleet. Of course, Linux server OSs have been dominant for years and continue to take massive market share from Windows.
Historically, the process of Linux device management involved unique technical expertise, making it a task that only a select few IT professionals would undertake. DevOps engineers and IT admins would need to know their way around the command line and be able to write and implement scripts. Learn more about mobile device management challenges and how to mitigate risk.
Over time, configuration management tools were created, but those required even more coding. Now, though, armed with the right tooling, the device management process for both Linux servers and desktops can be made accessible by most administrators with JumpCloud’s MDM for Linux.
Learn more about mobile device management (MDM) and why it’s important for your company’s different OS fleets.
Separately Managed Linux Devices

In general, Linux servers are used by developers to house production infrastructure or other critical data and information systems. The Linux desktop versions are often used by developers, and increasingly many organizations are using them to cut costs with other functions such as sales, customer support, and sometimes with remote workers.
As such, Linux MDM requires a keen security mindset to ensure that said infrastructure is protected. In practice, this means that the devices are often managed separately from other systems in the environment. Many IT management tools ignore Linux since historically it was considered to be a server platform managed by DevOps.
When a developer or other user has a separately managed Linux device, the IT organization may not have full control and visibility over the device, including managing user access, enforcing full disk encryption, and implementing other security policies.
This can cause significant risk to an organization as the device’s critical software components and data could be vulnerable to attack without IT’s knowledge. With the developer use case, often there is source code on the Linux device, so it can be high risk.
In the data center of cloud infrastructure environment, DevOps often manages their Linux machines through tremendous amounts of scripting and programming. Sometimes those groups will leverage configuration management solutions such as Chef, Salt, Ansible, or Puppet to handle management. Open source MDM is another popular solution for many IT admins, but is not often a good fit for Linux device management.
While these config management tools can provide flexibility, they require coding skills as well as infrastructure to ensure that the versions are correct, the code is safe, and there is data on the execution of those scripts.
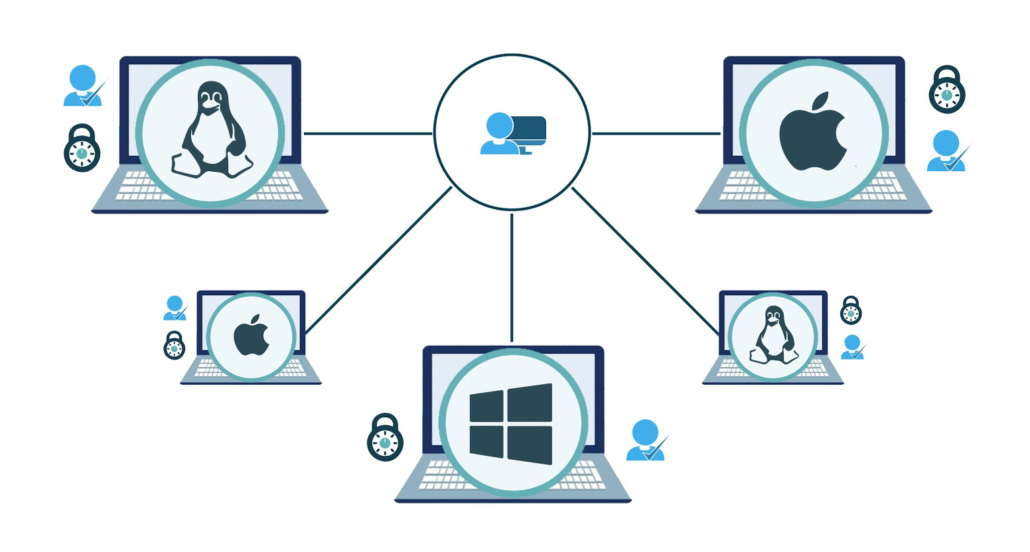
The trouble with these various approaches to device management is that there is no one central, cross-platform MDM for heterogeneous environments that manages Linux devices along with the rest of the devices in the infrastructure — Windows MDM, Apple MDM, or mobile devices, for that matter. Not to mention, the need for multiple tools can drive up the cost of your MDM solution.
Often an IT organization and a DevOps team will have completely separate tools to manage their infrastructure without the ability to understand the entire device fleet across an organization.
A Complete, Centralized Linux Device Manager
Linux device management — like all other system management or mobile device management approaches — should start with user access. With identity security being arguably the most critical issue in security today, IT or DevOps must manage access to the device in order to manage the device itself. Check out the full list of mobile device management best practices, regardless of the OS.
Once IT or DevOps controls access, configurations, settings, and security processes can be implemented without heavy scripting from manual management, configuration management solutions, or other tools. The benefit of a new approach to MDM for Linux can include better monitoring and reporting along with increased control and security.
JumpCloud Directory Platform is, at its core, a user and device management system with Linux user authentication and device management incorporated in the solution.
This cloud directory controls who can access your Linux devices and how — whether they need SSH keys, have sudo access, and more. JumpCloud can also enforce multi-factor authentication to Linux devices for step-up security.
And, through System Insights, JumpCloud provides hundreds of critical data points about each Linux device to better understand their health status and more.
Further, through a lightweight agent on each Linux device, admins can execute policies, tasks, and commands on each device. Tasks can be written in any language supported by the Linux device and JumpCloud’s command execution framework provides full audit reporting and logging of the tasks. JumpCloud even provides pre-programmed Linux Policies that can be leveraged reducing even more work for IT admins and DevOps engineers.
Compare MDM solutions with JumpCloud to get a better understanding of your options for Linux MDM.
Device Management in Linux Is Easy With JumpCloud
JumpCloud is OS-agnostic, which allows you to manage your Linux devices alongside the rest of your fleet. To manage your Linux device fleet much like you have control over your Windows, Mac, or mobile devices, sign up for a trial of JumpCloud today.





