On-prem domain controllers are a fact of life for IT admins at many organizations. You probably inherited whatever IT infrastructure you’re using, but that may just be technical debt. Many companies can achieve the same results for access control and system management without a domain controller by opting for cloud-based directory services. IT environments that have many Windows® machines can keep their domain controller and extend what’s possible for identity and access management (IAM) and manage devices (including non-Windows) via the cloud.
Not every organization is sold on the benefits of cloud-based IT management, but it’s worth considering because it can also eliminate some of the worst operational risks. Ask yourself, “Do you have a contingency plan if your domain controller goes down?” If it does end up failing, you’re going to be in a predicament that’s both disruptive to your productivity and costly to your business. That scenario is where cloud services will deliver higher availability as well as the capacity to manage identities and securely access resources wherever they may exist.
JumpCloud’s open directory platform is architected for high availability and redundancy across the globe, so it can help save the day when your domain controller goes down while doing more to manage identities and access than Active Directory (AD) itself. It also assists in the replacement or extension of your current Active Directory domain to the cloud using its open directory. Users access resources using the best authentication methods, entirely from a web browser. With this cloud-based solution, you no longer have to worry about your hardware server’s health, redundancy, or maintaining database integrity of AD domain controllers.
This article covers some of the scenarios that make an environment especially prone to AD failure and discovering how JumpCloud can help in these situations.
What Can Cause Domain Controllers to Go Down?
There are different risks to a domain controller’s uptime depending on how it’s being hosted. Several factors could cause domain controllers to go down or become unreliable if you’re running a traditional AD domain on Windows servers in a server rack on-site. These scenarios include power outages, network outages, AD database corruption, and hardware failure.
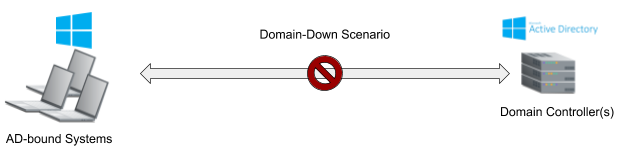
Those are just a few ways that a domain controller or your AD domain could fail. Running a single domain controller in a domain with no AD database backups, secondary domain controllers, or additional hardware available to reinstall Windows Server and Active Directory is an even worse scenario. That’s not an uncommon situation: hardware is expensive.
Running Active Directory on servers locally may bring some benefits to the company and its users, but without a proper crisis or backup plan in place, getting AD back to its original state might be impossible without a total rebuild. Rebuilds could take admins hours — if not days — depending on factors such as the number of users, computers, objects, and policies. Backups and redundancy are essential to running a proper AD domain. A full rebuild may be the only way to get Active Directory up and running again if the environment isn’t backed up.
Keeping up with licenses and versions can be another expense and chore for your IT admins. Windows Server’s core licensing model may cost more than you think, and licensing for Microsoft’s Azure cloud services (as a failover) is difficult to unpack. Given the associated licensing costs and complexities, domain controllers that have a critical failure could be in an unsupported or unrecoverable state, putting your business’s security and operations at risk.
Why Not Use Azure AD (AAD) Connect?
Microsoft makes it possible to authenticate via the cloud using Azure Active Directory and its AAD Connect middleware. Your domain controller remains the “source of truth” but AAD can handle authentications. There’s a 1:1 relationship between each synced AD object and an AAD tenant. This topology requires a subscription to AAD and installing AAD Connect.
A single domain controller will remain a single point of failure, even with AAD Connect configured with a secondary server in staging mode for disaster recovery. AAD Connect aids in disaster recovery but adds IT overhead. Azure AD Connect cloud sync is a new offering that uses an agent-based approach, but its capabilities are more limited than AAD Connect, i.e., no Azure AD Domain Services support. Neither approach will continue to manage your devices. That’s another subscription. JumpCloud can be configured as hybrid infrastructure, but also works domainless.
Single Domain Controller Scenarios & JumpCloud
Many small and medium-sized businesses (SMBs) running Active Directory might also be running a single domain controller in their domain. This could be due to complexity, cost, or user count.
AD domain controllers in this type of environment should be continuously backed up or have multiple instances so that replication and high availability are sustained. Creating a highly available and redundant domain with proper backups, disaster recovery plans, and stability comes at an increased cost and complexity. Extra hardware, dedicated off-site real estate, networking gear, and licensing come into play when creating a secondary domain controller.
Learn more about the total cost of Active Directory.
JumpCloud’s open directory platform extends your current AD domain users, groups, and their credentials into its cloud-based directory. JumpCloud’s Active Directory Integration (ADI) tool allows changes to users, passwords, and user state within a 90 second cadence leveraging two agents: AD Import and AD Sync. JumpCloud extends Active Directory’s users and their credentials to connect multiple different protocols such as RADIUS, LDAPS, and hundreds of SAML applications. Multi-factor authentication (MFA) is environment wide and modern authentication is available for better security and to safeguard against MFA fatigue attacks.
This way if a domain controller were to fail, the only resources that would be unavailable are the domain-bound resources. Fortunately, all other resources that make work happen (SAML apps, LDAPS connected file shares, RADIUS Wi-Fi, Google Workspace, M365, and more) would still be available for employees to access. Authentication would be managed by JumpCloud while user credentials are in sync with the AD domain and AD serving as the identity provider (IdP).
If a restore is possible in this scenario, the admin could go through Active Directory’s restore process to get the domain back online while their users continue using JumpCloud-bound applications and resources. If there was no restore available or if it was full hardware failure, it might be beneficial to migrate entirely from Active Directory to JumpCloud. JumpCloud has methodologies to manage systems, users, and security policies similar to Active Directory. (See how JumpCloud can help migrate users from Active Directory.)
You could consider repurposing the server to be a local DHCP, DNS, or NTFS file share for your company if your domain controller becomes unrecoverable but the hardware remains intact. This way, you can maintain the server you already have in your environment and repurpose it for other roles and tasks that your company would need without having to look at additional capex or opex costs. JumpCloud can also help manage this repurposed Windows server with its system agent so you can remotely manage users and policies with ease.
How Can JumpCloud Save the Day When an AD Rebuild Isn’t Possible?
JumpCloud can get your business directory and security needs back up and running in a few different ways if a disaster scenario occurs and a rebuild isn’t possible for your domain controller. This section explores JumpCloud’s benefits in hybrid and domainless configurations.
With JumpCloud’s Active Directory Integration
If you’re running a domain controller while also running JumpCloud’s ADI, your users are exported to JumpCloud along with their passwords bisynchronously. This means that your users’ passwords can be changed in either AD or in JumpCloud and will be propagated to the other directory when both JumpCloud’s import and sync agents are configured.
If a critical failure occurs on the domain controller where a rebuild or restore isn’t possible, you may want to consider moving from this hybrid configuration entirely into JumpCloud as your primary directory.
Your first step would be to leverage JumpCloud’s Active Directory Migration Utility (ADMU) to help migrate your domain users and domain-bound systems to JumpCloud-managed systems and local users on the Windows systems.
Additionally, you could take a few other steps to help transition the JumpCloud users in your tenant from AD-managed to JumpCloud-managed with the following commands outlined in JumpCloud’s public GitHub Wiki.
To leverage the commands below, you first need to install the JumpCloud PowerShell Module, outlined below:
Install-Module JumpCloud -Scope CurrentUser
You can then connect to your JumpCloud tenant using the JumpCloud PowerShell Module with the following command:
Connect-JCOnline
Use three copy-paste commands to leverage JumpCloud’s PowerShell Module:
Setting a singular user from AD-managed to JumpCloud-managed:
Set-JCUser -Username bobby.boy -externally_managed $false
This releases user ‘bobby.boy’ from AD Import or Sync so the user account can be fully managed by JumpCloud.
Get-JCUserGroupMember -GroupName Dev | Set-JCUser -externally_managed $false
This releases all users in the JumpCloud user group ‘Dev’ from AD Bridge so their user accounts can be fully managed by JumpCloud.
Get-JCUser | Set-JCUser -externally_managed $false
This in turn releases the binding to the Active Directory domain and the user will become a user account entirely managed by JumpCloud.
Without JumpCloud’s Active Directory Integration
If your AD domain controller fails or reaches an unrecoverable state without a restore possibility, JumpCloud can step in to become the primary cloud-based directory fulfilling your security and directory needs, entirely from your web browser.
There are several ways to get users into JumpCloud:
- CSV import (if applicable)
- Microsoft 365 Directory Sync
- Google Workspace
JumpCloud integrates with several different directories, creating a secondary method to get your users into JumpCloud to start to build out the services, resources, and security policies you need to meet your compliance requirements.
Once users are imported into JumpCloud, you can then move forward with JumpCloud’s ADMU (Active Directory Migration Utility) to migrate your AD domain-bound Windows systems to JumpCloud-managed systems. This will unbind the system from Active Directory, convert the AD user account to a local user account, and then install the JumpCloud System Agent automatically for you.
Simply bind the JumpCloud user to his or her JumpCloud system after the systems and users are provisioned. JumpCloud will take over the profile and enforce the password that the JumpCloud user has set (as long as the JumpCloud username and Windows local username match). This all happens within minutes.
Enforcing system policies to specific systems or to entire system groups is much easier than with Active Directory and can be done entirely within the JumpCloud Admin Portal. Groups are attribute-based to automate user lifecycle management for higher admin productivity and more mature entitlements management than AD. Check out JumpCloud’s Knowledge Base for more details on system policies, user naming conventions, and user resource bindings.
How Does JumpCloud’s Open Directory Platform Avoid a Traditional Domain Controller Failure?
The open directory platform makes identities your new perimeter and devices gateways to resources. JumpCloud was designed to be a cross-platform alternative to Active Directory and LDAP. It can serve as the single, central directory for multiple different resources and protocols such as Microsoft 365 and Google Workspace to other SAML or OIDC applications your organization might use. It was built on a secure, robust platform in the cloud and there are multiple high-availability zones which are continuously maintained and monitored by our team.
JumpCloud unifies IAM and device management capabilities, regardless of the underlying authentication method or platform. Secure, frictionless access is fundamental for IT organizations, and JumpCloud ensures that every resource has a best way to connect to it.
For example:
- Servers use SSH keys, which are more secure than passwords
- Passwordless certificates can secure RADIUS Wi-Fi access
- Web applications use SAML and OIDC for authentication
- Conditional access rules for privileged access management
The user experience is also straightforward and easy to comprehend. Plus, one admin can manage policies, devices, as well as single sign-on (SSO) for your enterprise apps. And policy templates are available to assist with scaling your device postures across your entire fleet.
Centralized Device Management
Its system management capabilities are robust, with a small, lightweight agent that is installed on all of your machines, regardless of OS. Users can log in and access their systems from anywhere, whether it be online or offline. JumpCloud also includes mobile device management (MDM) for Apple products and Android Enterprise Mobility Management (EMM). JumpCloud enables both corporate-owned device (COD) and bring-your-own device (BYOD) scenarios.
JumpCloud’s System Agent manages local accounts as well as local system policies. When online, the system agent regularly checks in to see if there are any updates for the user, system, or associated policies. Policies are pre-built and command triggers are available, in addition to PowerShell and terminal access (with root rights), all from a secure, centralized admin console.
System and user management is entirely done in the cloud — meaning no servers, no RDP, and only one platform to govern your resources. JumpCloud’s Admin Console gives you and your IT team the flexibility of administering all from within a browser window, including remote assist.
JumpCloud follows a transparent, workflow-based pricing model, and is tailored for cloud-forward, mixed platform environments. Try JumpCloud today without any obligations. Your first 10 users are free with 10 days of complimentary premium chat support.
Need a Helping Hand?
Reach out to [email protected] for assistance determining which Professional Service option might be right for you.




