
Zero Trust Demystified
Simplifying the Zero Trust Journey for Small and Medium Enterprises
Zero Trust is a security model that has gained traction since the shift to remote work, and has now become necessary for all small to medium-sized enterprises (SMEs). However, its novelty and pervasiveness in the market have earned it buzzword status, giving rise to confusion around what Zero Trust is (and, equally important, what it isn’t), whether businesses need it, and how to achieve it.
Zero Trust arose for a reason, and despite its reputation for complexity, it’s actually a straightforward (but important) concept:
Employees should only have the necessary amount of access to accomplish their tasks.
Despite its straightforward core concept, however, Zero Trust implementation takes time and planning. In Forrester’s Practical Guide to a Zero Trust Implementation, it estimates that a typical Zero Trust roadmap might extend about two to three years. What’s more, the initial steps (like the mapping process itself) can take significant time and resources.
Fortunately, there are many Zero Trust wins businesses can implement quickly and cost-effectively, and many more Zero Trust elements businesses already have in place, even if they weren’t implemented for the purposes of Zero Trust (like multi-factor authentication (MFA), mobile device management (MDM), and identity management projects). Small tweaks to these structures or building off of them can speed up your overall Zero Trust progress alongside your planning and mapping processes.
This guide intends to demystify the complexity that’s built up around Zero Trust, help you identify and implement quick wins in your organization as part of your longer Zero Trust journey, and accompany you on your Zero Trust journey, offering practical guidance alongside your strategic, long-term planning.
Benefits of Zero Trust to Small and Medium Enterprises
Security
Cybercriminals don’t just target large conglomerates and Fortune 500 companies; cybercrime trends tend to follow similar patterns in small and large businesses alike. And they’re on the rise. The shift to remote and hybrid remote work created a security gap: many organizations adopted remote models quickly and haphazardly, and security took a backseat to keeping the business afloat. Cybercriminals acted quickly while companies’ defenses were down, and cybercrime skyrocketed in 2020. Today, bad actors continue to exploit gaps in companies’ remote and hybrid infrastructure, and cybercrime continues to rise.
Remote and hybrid environments necessitate modern security; while the perimeter method may have gotten companies by before the pandemic, it’s no longer adequate in the face of modern environments and threats. Now that the average SME has 30% of employees working remotely and 32.5% working hybrid-remotely, SMEs’ security programs need to support remote and hybrid setups. In fact, SME IT professionals ranked “adding layered security so work-from-anywhere is truly secure” as their top priority for both 2021 and 2022, and over 80% agreed that remote and hybrid-remote work increased their focus on security.
IT Industry Pulse Check
JumpCloud conducted two surveys in 2021 to assess SME IT professionals’ experiences with their technology in the rapidly changing workplace. The first survey, conducted in April, reflects organizations’ changing priorities in the face of remote work. The second survey, conducted in October, shows IT professionals pivoting to embrace security and work-from-anywhere models.
As Zero Trust is designed to protect modern cloud environments, it provides the best defense against cybercrime and offers SMEs a sustainable security foundation for long-term remote and hybrid work.
Usability
Zero Trust frameworks are designed to accommodate cloud resources, which have evolved to be more user-friendly than their legacy counterparts. As such, Zero Trust implementations tend to be similarly cloud-based and user-friendly. From reducing the user’s need to remember and input passwords to automating onboarding and offboarding, Zero Trust implementations tend to improve the employee experience. Pure Zero Trust environments use integration, automation, and a single source of truth, which in turn offer users consistent, intuitive, and seamless experiences.
Future-Proof
Because Zero Trust was designed to work within and support cloud environments, it is better-suited to securing cloud-based resources than older security models. As the shift from legacy to cloud continues to pick up steam, Zero Trust will likely continue growing in popularity and replacing perimeter security models over time.
Further, Zero Trust’s departure from physical infrastructure makes it more malleable and adaptable than traditional perimeter-based security and, therefore, better-suited to adapt to future changes. Most Zero Trust tools and practices are software-driven and can be controlled virtually, allowing them to adapt and scale as organizations and technology do over time. This is particularly important to the SME, which needs to remain nimble and adaptable amidst frequent organizational and market changes.
Better Admin Experience
Zero Trust’s software-driven architecture makes it easier for IT to manage. While its implementation is a large undertaking, its adaptability, automation, and remote accessibility make it user-friendly to the IT administrator in a hybrid-remote environment. Further, Zero Trust architectures provide better visibility into the infrastructure as a whole and its activity. This simplifies security administration, making it easier for IT admins to detect and address issues before they become breaches.
Streamlining the IT admin’s experience heightens security while creating an environment that fosters smooth organizational changes, scaling, and IT maintenance. In SMEs where IT departments may be strained, this saved time can be reallocated to make a significant impact in other IT initiatives without compromising on security.
Why Haven’t More SMEs Adopted Zero Trust?
According to a survey conducted in late 2021, a little over half (58.6%) of SMEs reported pursuing or planning to pursue a Zero Trust security program. In another survey conducted in the same year, only 23% of respondents said they had fully adopted it already. If Zero Trust is so beneficial to SMEs, why haven’t more of them adopted it yet?
The Piecemeal Problem
The all-too-common products claiming to be the “Zero Trust magic bullet” have been more harmful than helpful to Zero Trust adoption. The SaaS market tends to encourage companies to keep up with the latest and greatest tech; companies, in turn, end up stacking their infrastructure with security tools that lack cohesion and strategy. This ad-hoc purchasing approach and high tool volume tend to move companies further away from Zero Trust rather than closer to it.
These cluttered infrastructures require many complex integrations to get tools to work with one another. They likely contain many dependencies (which are not all documented) that slow any agility that the tools might have promised. Anything from a tool update to a new addition to the stack can break one integration, sending a domino effect through the rest of the infrastructure.
23% Percent of SMEs have fully adopted Zero Trust
Businesses working within such an environment, therefore, hesitate to make sweeping changes to adopt Zero Trust. Businesses that went this piecemeal route to achieve Zero Trust might have abandoned the cause after witnessing an ever-increasing complexity without any increased security to show for it.
Cost and Labor
The piecemeal approach to Zero Trust can cause costs to compound – not just in terms of solution purchases, but in terms of the labor and expertise it takes to manage them as well. Introducing new solutions in an environment requires ramping up time and training followed by ongoing management and maintenance. This ongoing labor can either be filled in-house or by hiring additional expertise. Because point solutions tend to accumulate, SMEs that manage them in-house often end up with strained IT teams. Those that hire new employees or external help usually find that cybersecurity expertise is hard to come by and expensive, which can quickly make this approach cost-prohibitive.
Overcomplication of Zero Trust
For many, Zero Trust seems like a monumental undertaking that intimidates them. For many more, Zero Trust remains somewhat of a mystery. IT professionals are tired of hearing about the latest and greatest “Zero Trust product” and feel that Zero Trust is just another buzzword.
In addition, seeing many different tools with “Zero Trust” labels can further confuse the Zero Trust concept, making the Zero Trust goal feel too broad and unattainable for SMEs. But in reality, it’s a straightforward concept that can have a lasting impact, even when implemented in incremental phases.
Simplifying the Journey
There are many stages in the Zero Trust journey that precede the end goal of a pure Zero Trust architecture, which takes years to achieve. The best way to start and plot your journey is to embrace your perimeter/Zero Trust hybrid state and set your sights to smaller, achievable milestones.
In its Practical Guide to Zero Trust Implementation, Forrester recommends mapping those milestones in three key phases:
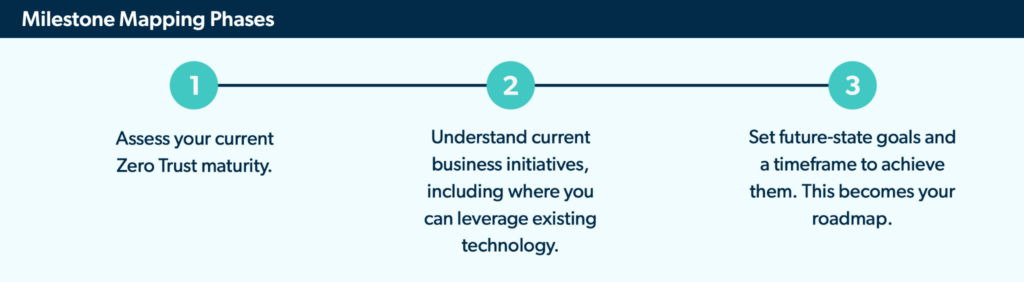
The goals and roadmap developed in step 3 can be broken up into five categories, which Forrester recommends addressing in roughly the following order:

This order allows your security to compound and build off of existing initiatives to form a cohesive Zero Trust security framework. However, these phases are (purposefully) broad; when your entire infrastructure stands to be reformed, it can be hard to know where to begin.
7 Simple Zero Trust Action Steps for SMEs
Starting any new endeavor can feel overwhelming, especially when one wrong move could cause productivity to come to a grinding halt. Check out these seven simple action steps – emphasis on the word simple – for small-to-medium-sized enterprises (SMEs) wanting to move toward a Zero Trust security framework.
Where to Start?
There are a few angles you can take when deciding what to prioritize. However, the key to any of these angles is prioritizing the steps that make the most sense for your organization. Below are a few guiding metrics to choose from when identifying which steps will be most impactful.
Start Small
For some organizations, baby steps are the best route. This may be the case for strained IT teams, smaller organizations, organizations at the very beginning of their journey, and organizations without much leadership buy-in.
Small steps don’t have to yield small impacts. Some small, low-cost initiatives can have substantial effects on your security and move you significantly closer to your Zero Trust goal.
MFA Everywhere: Many organizations already have MFA in place in some of their tech stack. Expanding this to cover more of their tech stack – to eventually be in place everywhere – has substantial security gains, and can be cost-effective and easy to implement. Most users are familiar with MFA processes, so buy-in effort is usually minimal. Some MFA solutions even come free with IAM and directory software, which can further amplify your Zero Trust progress. Investing in one tool that can do both (among other Zero Trust initiatives, like automating offboarding and patch management, for example) is a cost-effective way to spur significant progress.
The key to any of these angles is prioritizing the steps that make the most sense for your organization.
We recommend slowly integrating new systems and tools as you move from one Zero Trust stage to the next. Check out these eight tips to overcome Zero Trust obstacles (and make small improvements along the way).
Start With High-Traffic Tools
Another place to start can be at high-traffic junctures: what people use the most. For instance, while securing access to documents only HR leadership uses may be worthwhile, its low usage might allow it to wait while you focus on more frequent touchpoints, like collaboration platforms or project management tools. This method can be ideal for larger SMEs with many users working on certain platforms and remote or hybrid SMEs that worry about proper tool usage in unsupervised environments. Securing these high-traffic tools can be a great catch-all safeguard to start with.
Single sign-on: SSO can apply to all employees and all resources, making it a high-traffic tool with a high security yield. Implementing SSO is a low-cost and low-effort way to drive immediate security benefits across your organization.
Secure the Crown Jewels First
This methodology approaches security at the most critical level first. Of course, in an ideal world, you’d be able to secure all the elements in your infrastructure right away. But prioritizing one thing de-prioritizes another by nature; understanding your company’s infrastructure, resources, environment, and threat vectors can help inform these tough choices.
Thus, this approach works well in organizations that already have a good understanding of their environment, resources, and stack, and can easily identify their most critical assets. If inventorying your infrastructure to identify your crown jewels becomes a large task that could hold up progress, consider starting with another, more digestible step instead as you inventory and assess your infrastructure.
Network segmentation: Segmenting the network to at least guest and corporate levels can work wonders in protecting your critical assets. Segment resources on each segmentation based on PLP, with the crown jewels only accessible on the admin/highest-privilege network.
Despite the publicity, only 23% of SMEs have fully adopted Zero Trust security programs to date. Why? Here are six unexpected roadblocks SMEs often face (and how to overcome them).
Note: Don’t Underestimate Usability and Buy-In
Even the best-laid Zero Trust plans won’t take hold without buy-in from users, IT, and leadership.
Buy-in from users stems from usability. As cloud-based tools become more user-friendly and people integrate technology more heavily into their personal lives, users expect clear, intuitive, and seamless technology experiences in and out of the workplace. In fact, the employee experience is becoming a key differentiating factor when it comes to employee retention. Thus, implementing a security system that accumulates friction for the user will result in avoidance, shadow IT, human error, and even higher employee churn. This failure to seamlessly adopt the security practices can create more vulnerabilities than they prevent – shadow IT and human error in particular are substantial contributors to security breaches.
Similarly, the IT team should also experience usability gains when implementing new security measures. While the initial implementation can be expected to create work and friction, the long-term plan should produce a better management experience for your IT team. Otherwise, you’ll face similar challenges like avoidance, workarounds, lack of maintenance, and failure to maintain one source of truth. These challenges create an environment with poor visibility and a lack of central management – a breeding ground for security threats.
Finally, buy-in from leadership and stakeholders should never be underestimated. Trusting in your security program requires trust in your users and administrators; you need to cultivate a strong security culture, and culture comes from the top. Leadership will either drive or stymie your security efforts based on how they treat security. If leadership doesn’t believe in or emphasize the importance of your security program, you won’t be able to achieve buy-in from your users or IT team.
On the other hand, if leadership believes in your initiatives, you’ll not only have the funding and support to invest in the initiative, you’ll also have reinforcements when it comes to enforcing security best practices across your organization.
Overall, when choosing which Zero Trust steps to take, consider buy-in from the user, IT team, and leadership perspective. Choosing steps that will deliver a positive user experience, align with existing buy-in, or easily cultivate buy-in can help ensure the steps take lasting hold.
Choosing Technology Solutions
While it’s important not to overload your IT stack, you will likely need to invest in technology solutions somewhere along your Zero Trust journey. When evaluating solutions, keep the following in mind.
Tip: JumpCloud offers a pricing comparison tool that estimates the cost of different directory and infrastructure implementations based on your organization’s size and environment.
-
Choose a solution that makes sense for your organization: Look for tools that your organization can afford and manage successfully. The robust, feature-rich tools Fortune 500 companies choose might not always make sense for an organization of 50 that needs to accomplish a straightforward task. Similarly, purchasing several popular tools may not be ideal for your organization if one could do the job more cost-effectively. Often, integrated tools offer both cost effectiveness and easier management, making them the ideal investment for SMEs.
-
Consider compatibility with your current and future state: Organizations that aren’t nearing their Zero Trust journey’s completion should ensure tools work with both their current architecture (including Zero Trust and non-Zero Trust elements) and their future-state, pure Zero Trust environment. Organizations at the beginning or middle of their Zero Trust journeys should look for tool flexibility and adaptability.
-
Think ahead: The tools you purchase now will have lasting impacts on your environment. Tools that don’t integrate well with another tool in your stack, for example, will plague your environment for years to come. Similarly, overly complicated tools may offer many features, but they can make upkeep tedious as your environment changes. Often, upkeep dwindles over time and creates new security problems. For instance, failing to update a role’s privileges can result in users with too many permissions – the antithesis of Zero Trust. Look for tools that keep maintenance streamlined for the admin and the experience positive for the user.
-
Consider costs holistically: A solution’s price tag is just one of many costs to consider. The operational costs of maintaining a complicated product, for example, can make it a worse investment than a product with a higher price tag but easier maintenance and lower overhead. Tools that combine several functions can also help keep TCO down by eliminating the need to purchase additional tools. These comprehensive tools also streamline upkeep by ensuring more elements in the infrastructure work well together and minimizing the need for integrations that create compounding tool dependencies down the road.
Take the Complexity Out of Security
Although it sounds counterintuitive, complexity is a detriment to security rather than a strength. Complexity around the “Zero Trust” term has prevented SMEs from embracing it, complexity in the user experience hurts security adoption, and complexity for the IT admin causes infrastructure degradation over time. Instead, straightforward, intuitive, and cohesive solutions form the strongest foundations for a reliable security program.
To help IT professionals eliminate unnecessary complexity from their security initiatives, JumpCloud has drawn up a library of resources designed to simplify important security concepts and offer IT professionals practical security guidance in real-life environments. Visit the resource library, Security Without the Complexity, to continue honing your security strategy.
Make Work Happen
JumpCloud® helps IT teams Make Work Happen by centralizing management of user identities and devices, enabling small and medium-sized enterprises to adopt Zero Trust security models.
Try It for Free
