IT admins are grappling with how to manage Mac users and systems after all the changes to macOS® High Sierra. One specific example of a change made to macOS High Sierra is that Secure Token is disabled for a user. This problem affects the usage of FileVault® because without a Secure Token, users are unable to manage a FileVault volume. Essentially, this means users can not enable, disable, or decrypt the FileVault volume.
Unintended Consequences of Secure Token and FileVault® for IT
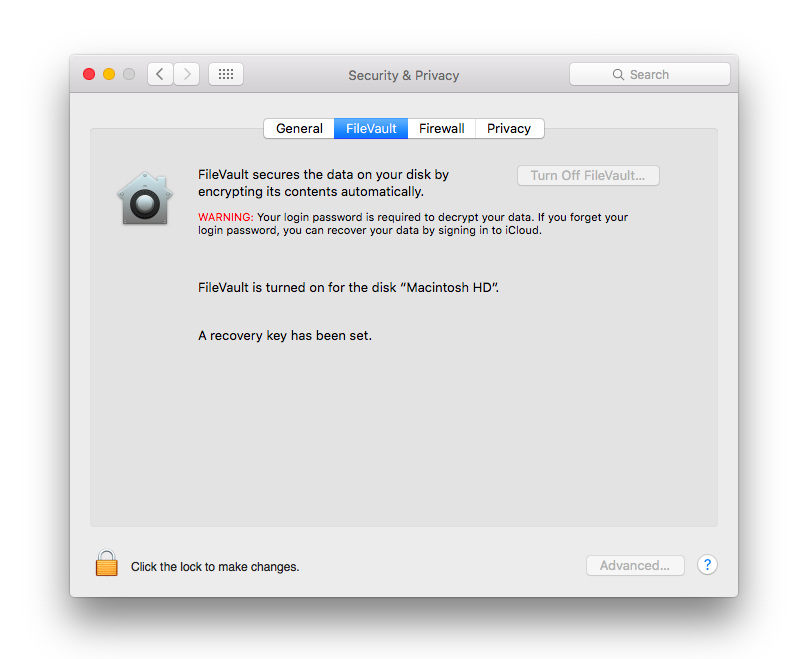
Apple® created this issue seemingly from a place of benevolence. Apple intended to both increase the security of FileVault while reducing the number of steps needed to enable full-disk encryption for users. This resulted in fundamental changes with regard to how user management works within macOS. With the release of High Sierra, Apple introduced a system that requires users to have a Secure Token in order to use FileVault. This Secure Token was granted to the first user created on the Mac system. Additional users would be granted a Secure Token only if their user account was created locally by the first user. This essentially creates a chain-of-trust that ensures only additional users approved of by the first user are given access to the FileVault volume (essentially data) on a given macOS High Sierra system.
How Can a Chain-of-Trust Create Animosity?
The problem admins will come to discover is that identity management systems create users remotely, not locally, which has effectively broken any instances managing Mac systems with FileVault enabled via Microsoft® Active Directory® (MAD or AD). This is just another instance in a long line of instances where Active Directory has struggled to manage Mac users and their systems. IT admins are now the ones in the crosshairs, because they are no longer able to create users by utilizing APIs or network-based tools . Instead, they’re forced to go host-by-host in order to properly manage Mac users. This, of course, is far from an ideal solution, especially as we consider that the usage of Macs within the enterprise is rising.
That’s Going to Take Some Time
Sure, admins could trawl each and every Mac in their fleet and manage their Macs that way, but what professional has time for that? Fortunately, for both IT admins and users alike, there is a solution to this vexing problem. JumpCloud® Directory-as-a-Service® recently enhanced its agent to effectively and properly manage macOS High Sierra users with FileVault enabled. Now, IT admins can remotely manage users on macOS High Sierra systems with ease. In addition to the benefits gleaned from remote Mac management, the JumpCloud Directory-as-a-Service platform enables GPO-like policies on the Mac as well. While called Group Policy Objects in an Active Directory environment, JumpCloud just calls them Policies. These policies allow admins powerful tools previously only seen on Windows machines due to tight integration with their on-prem directory solution, Microsoft Active Directory. Now, because JumpCloud Directory-as-a-Service is platform agnostic, those GPO-like policies work across Mac, Windows®, and even Linux® systems to create blanket policies that enable cross-platform harmony. And, it all works without a VPN.
Learn More about JumpCloud®
So, if you’re tired of dealing with the Secure Token disabled for a user problem and subsequent issues with FileVault and wish to enable remote management of Mac machines in your IT infrastructure, feel free to try JumpCloud Directory-as-a-Service for free today. The first 10 users, no matter the platform, are free forever. Finally, you’ll be able to work with Mac, Linux, and Windows machines easily and from one single pane of glass. If you have further questions, go ahead and head on over to our support site or drop us a line.


