As the IT world continues to migrate to the cloud, Microsoft® continues to push Azure Active Directory as their platform of choice. But as many IT admins know, Azure AD just isn’t a viable replacement for on-prem Active Directory. The result is that IT organizations are left asking, “Is there an open source Azure Active Directory alternative?” Let’s briefly explore the question together.
Searching for an Open Source Azure Active Directory

In a sense, IT admins are looking for an OpenStack®-like alternative to AWS® or other IaaS platforms. Released in 2010, OpenStack is essentially “a free and open-source software platform for cloud computing” from which virtual resources can be used. OpenStack has achieved some success as a software platform, but its results are instructive as IT organizations consider the use of an open source directory services platform.
Unfortunately, an open source replacement for Azure Active Directory just isn’t available. There are, of course, a number of on-prem open source directory services and identity providers delivered as software. Some examples include OpenLDAP™, SambaTM, and FreeIPA. All three of these open source authentication platforms are useful and can benefit organizations, but they aren’t going to end up being a replacement to Azure AD.
Outside of the obvious difference between Azure AD and other open source identity providers (Azure AD is certainly proprietary), the challenge with these open source directory services solutions is that, ultimately, they inhibit IT organizations from being able to authenticate to a wide range of IT resources. Each of the open source identity providers is greatly positioned to cater to a specific slice of the market, intentionally limiting the breadth of their functionality to do so. In the case of OpenLDAP, for instance, the LDAP protocol is the primary path. FreeIPA, on the other hand, adds in the Kerberos® protocol. Samba does this a well, but can also act as more of a domain controller in the process. None of these platforms deeply integrates with systems to provide Microsoft Active Directory (MAD) controls.
Open Source Challenges in the Modern Era
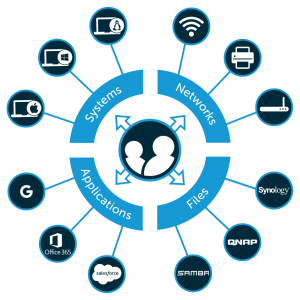
The end result is that organizations that are leveraging modern IT solutions, such as G SuiteTM, AWS, Mac® and Linux® systems, cloud storage, NAS appliances/Samba file servers, and much more, will struggle with Azure AD, as well as its on-prem open source alternatives. By Microsoft’s design, they’re simply not built to work together. While this doesn’t seem all that practical in the modern world, it’s the reality for heterogenous organizations now looking elsewhere to optimize their identity management infrastructure for open source, on-prem, or virtual resources.
In short, the idea of shifting to an open source directory service is still considerably difficult if you are a modern organization with a wide range of IT resources and cloud forward. Of course, Active Directory (which is still needed with Azure AD) isn’t the cloud identity management platform that IT organizations are imagining and hoping for either.
The good news is that there is a modern, comprehensive cloud identity management solution called JumpCloud® Directory-as-a-Service®, which is an alternative to Azure Active Directory as well as a replacement to on-prem Active Directory. While not open source, Directory-as-a-Service streamlines identity management and alleviates the workload of IT admins with cross-platform, endpoint-centric access for users to the resources they need. Whether Mac®, Linux®, or Windows systems, on-prem or in the cloud, Directory-as-a-Service gives IT organizations a significant alternative to Azure Active Directory.
Directory-as-a-Service Replacement for Active Directory
Want to know more about how JumpCloud Directory-as-a-Service can be implemented as an alternative to an open source Azure Active Directory? Go ahead and drop us a line or give us a call and we’ll be happy to answer any questions you might have. Ready to see the features for free? No problem. Sign up and your first 10 users are on the house, forever.




