
Wait – is that even possible?
Yep. Many IT admins don’t realize it, but you can authenticate and authorize users to a directory service without Microsoft® Windows®. And, you can manage the device with GPO-like policies. Not only is it possible to manage your Windows devices without Microsoft’s Active Directory®, it can be powerful.
Let’s start with why.
Why Manage Windows without AD
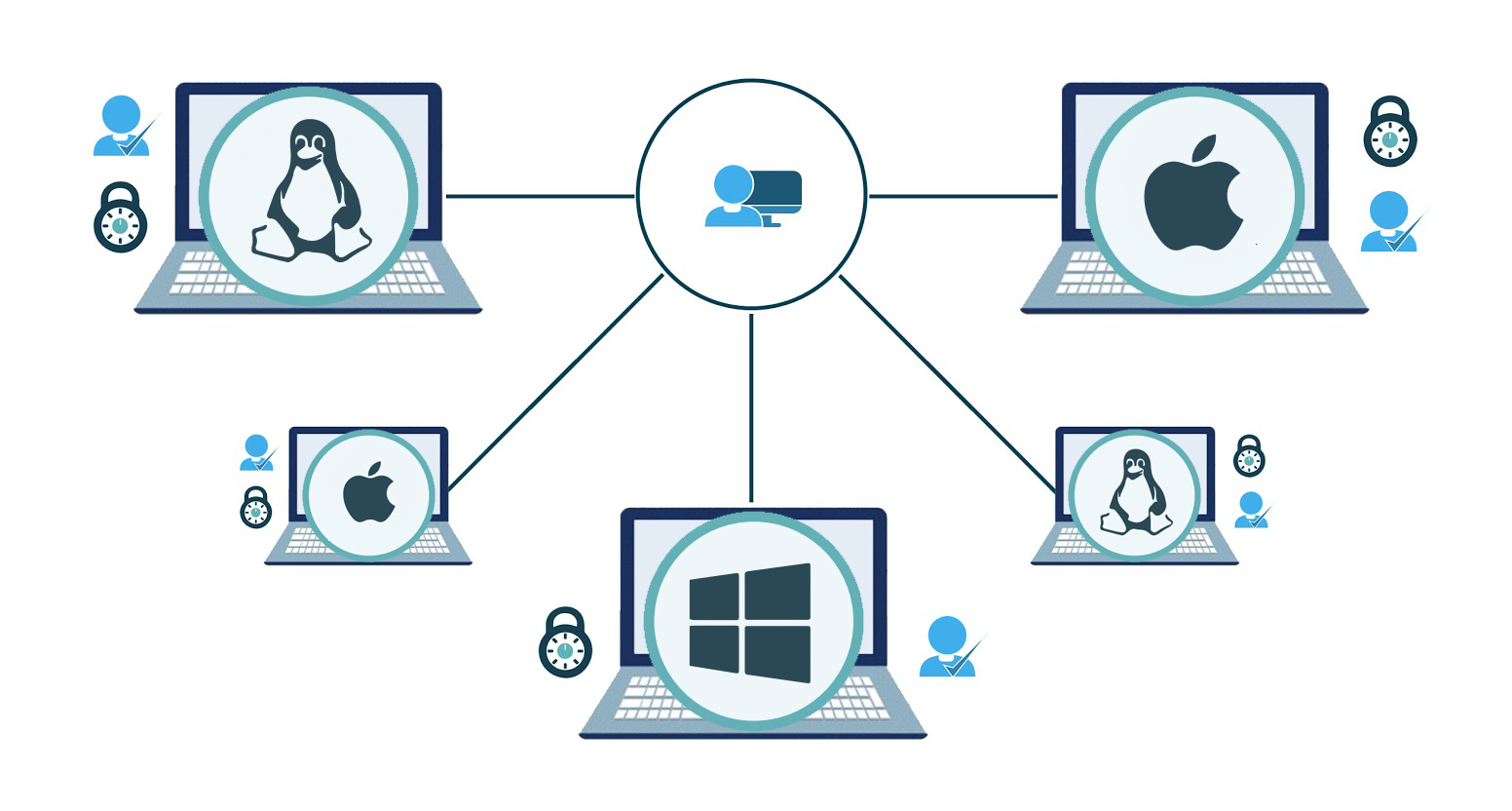
Many organizations today aren’t 100% Windows – in fact, they are a mixture of Windows, Mac®, and Linux® (not to mention iOS and Android). Environments today are heterogeneous and relying on your directory services for only one flavor of platform means missing out on a tremendous opportunity.
Users with Mac and Linux devices should be authenticated and managed just as much as Windows machines. Even beyond that, your directory services should tie into all of your devices, including cloud servers and applications such as Web and SaaS-based applications.
Active Directory device management doesn’t focus as heavily on non-Windows devices and applications and, as such, it’s capabilities are more limited in that area. So if your organization is heterogeneous, it’s important to find an all-encompassing solution that is able to authenticate, authorize, and a wide variety of devices, including Windows. Ultimately, that means managing Microsoft Windows without an AD instance being present.
How to Manage Windows without AD
Now that we’ve established why it’s important to be able to manage Windows devices without AD, let’s talk about how that can happen.
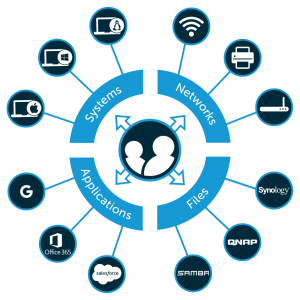
JumpCloud® Directory-as-a-Service® is a cross-platform cloud-based directory service. It can control users on Windows, Mac, and Linux devices. It can also manage the devices themselves by executing policies or scripts on each device type.
JumpCloud’s approach to managing Windows devices without AD has been to build a lightweight agent that is deployed on each Windows device. The agent gives JumpCloud’s SaaS-based platform the ability to natively create users, authenticate them, and deprovision them.
Further, the agent has the ability to run PowerShell commands and scripts, similar to what GPOs do. IT admins can run scripts that will change registry settings, update files, copy logs, and much more. Anything that can be done via PowerShell can be delivered to any Windows device via JumpCloud. Everything is monitored; all policies or scripts executed by JumpCloud are logged for their success or failure and any results.
Benefits of a Cloud-Based Directory

The big benefit of this non-AD approach is, of course, that you have a central directory service and command execution tool across all three major platforms. Rather than managing only your Windows machines and handling the rest of your infrastructure differently, JumpCloud’s approach provides a single pane view across the entire organization regardless of platform or location.
It’s a highly streamlined, highly modern approach to the directory. There is no on-premises software or hardware to manage and maintain. Costs are controlled because you only pay for what you need and use.
Learn More about Directory-as-a-Service
If you are interested in managing Windows devices without the need for Active Directory, take a look at JumpCloud Directory-as-a-Service. You’ll gain much of the control of AD across all three of your major platforms without the drawbacks. Drop us a note if you have any questions or feel free to give JumpCloud a try. Your first 10 users are free forever.




