Zero trust security is a concept developed by John Kindervag and Forrester Research Inc. in 2009. (Forrester)

Also called zero trust network architecture, the idea of zero trust security is really a diametrically opposing view to the conventional “perimeter-based” architecture of security over the last twenty to thirty years. With recent identity breaches, vendors and analysts are wondering whether a zero trust security model could work to prevent compromises.
Early Network Security

Kindervag describes traditional network security models as being akin to “‘. . . an M&M, with a hard crunchy outside and a soft chewy center’” (Forrester). IT organizations would create a perimeter “fortress” around their network and then create layers of security so that hackers would struggle to get through them.
The core of the network would have the most critical assets—data, applications, and identities—and, in theory, the defense in-depth approach made it difficult to get to them from a hacker’s perspective. This approach to security involves implicitly placing trust in not only the perimeter layers, but also users who operate inside of the core of the network.
The Advent of Zero Trust Security

In the modern era, however, bad actors are everywhere, and the traditional method of security leaves something to be desired, as more and more hackers have started attacking networks from both inside and out.
The chart above from a NIST report on Forrester’s development of the zero trust security model shows the most common sources of security breaches from 2011-12. Almost 50% of these attacks originated from inside an organization, while only 25% of those were headed by external sources. In other words, in today’s world, more security threats come from inside an organization.
So, does the traditional, perimeter-based security model still work?
If a network is an M&M, it’s clear that the “hard outer shell” isn’t doing it’s job to protect the “chewy center.” But the zero trust security model doesn’t rely on a hard outer shell.
The mindset behind zero trust security is to regard all sources of network traffic, both external and internal, as potential attack vectors. Therefore, all users and resources must be verified and authenticated, system data must be collected and analyzed, and network access and traffic must be limited and monitored.
While it may seem a bit paranoid, zero trust security is rooted in the realities of the cloud computing age. Instead of an M&M, the perimeter-less approach to networks more closely resembles a hard candy: equally resilient from perimeter to core.
Modern Information Security

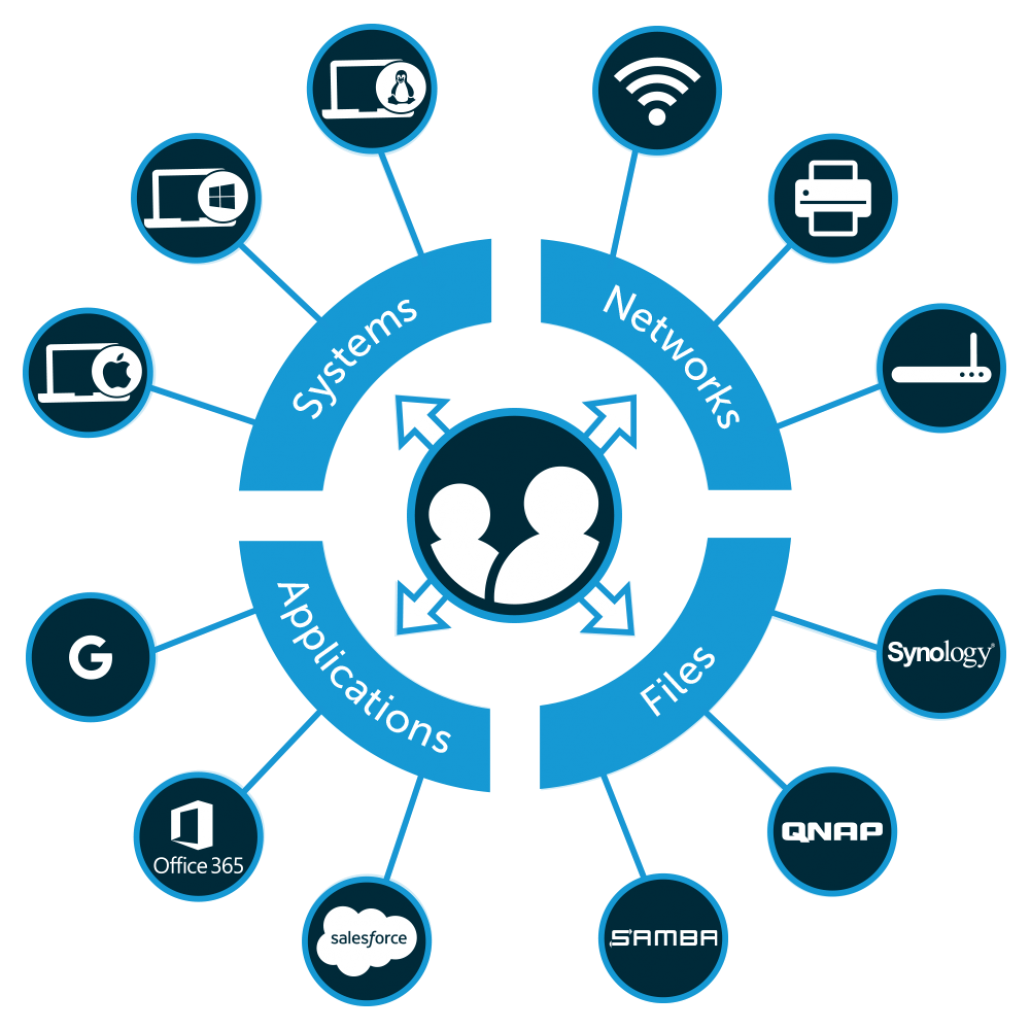
Today, data and applications are stored directly on the internet with SaaS providers and cloud infrastructure. Users are located around the world and need to be able to access their IT resources. Meanwhile, on-prem networks are looking more like internet cafes with WiFi than the fortresses of the past. Hackers no longer need to step through layers of security measures; rather, they can choose specific types of IT resources to target.
The result is that IT organizations are considering different ways to approach how they protect their environments, especially regarding authenticating user identities. It was recently reported that over 81% of all breaches are caused by identity compromises (CSO).
So, if ever there were something to distrust, it would be identities. But we can’t just eliminate identities. We all need our credentials to access whatever IT resources are necessary. So, how does a zero trust security model work with the fact that identities are most often the conduit to a breach?
Zero Trust Security in Identity Management

IT security experts have been developing a set of identity security practices that can solve this problem. The simplest, yet most powerful, way to confirm identity is to leverage a multi-factor authentication (MFA) approach. Requiring a second factor for machines, as well as applications, eliminates a massive level of risk by ensuring that leaked credentials alone won’t be enough to ensure access.
When you fortify MFA capabilities with strong passwords, SSH keys, and strong internet hygiene (i.e. ensuring that you are safe on the web with SSLs/https and only going to credible sites), you can further reduce the chances of a breach. By requiring significant step ups in authentication, as well as a keen policy of internet vigilance, IT organizations can adopt a zero trust security model and apply it to identity management.
Cloud IAM Solution for Zero Trust Security
To learn more about leveraging a zero trust security mindset in your identity management solution, contact us. If you are interested in an all-in-one, cloud-based zero trust solution, try JumpCloud® Directory-as-a-Service®.
With JumpCloud, you can implement MFA, password restrictions, centralized user management, access controls and more, as well as a platform-agnostic directory service. Schedule a demo of JumpCloud, and see what it has to offer.
