Updated on December 20, 2024
Until recently, Windows was the de facto platform of choice in the working world as businesses set up their networks on the Microsoft operating system.
They used Word for word processing, Excel for spreadsheet work, PowerPoint for presentations, and Active Directory for domain management. However, the old paradigm has been shifting for some time now.
While Windows-based PCs and laptops are still the market leaders for large and small-to-medium-sized enterprises (SMEs), many organizations have begun to adopt Mac, Linux, and Android devices. Improved usability, convenience, and affordability are commonly cited reasons for switching.
Translation: administrators must manage and control access to their Azure Active Directory from different types of devices and operating systems.
So, can you bind a Mac to Azure Active Directory?
Let’s find out.
Mac and Azure AD: Unwilling Bedfellows
The short answer is yes — you can bind Mac to Azure. But as you can imagine, it is far from straightforward.
Competitors hardly find incentives to make life easy for each other. Think of Pepsi and Coke’s cola wars or Nike and Adidas’ sportswear battles; they’ve been at it for decades. Apple and Microsoft are no different.
With Microsoft’s Azure being a leading access management solution, many IT managers have found themselves being the grass that suffers the pinch between the giant boots of these two tech giants.
Since its release in 2000, Active Directory (AD) has been a staple for Windows networks. It provides users and IT admins with identity management, access control, and policy enforcement for Windows servers, desktops, and laptops.
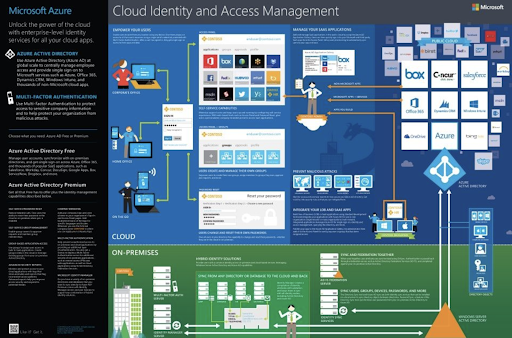
Azure Active Directory (AAD) is Microsoft’s cloud-based version of its traditional on-premise Active Directory service. It allows businesses to securely access their applications and resources from anywhere on their windows device.
However, the problem arises when it comes to Apple’s Macs. While Microsoft has done an excellent job of making Windows computers compatible with AAD, the same cannot be said for Mac users.
The Challenge of Binding Macs to Azure AD
The challenge of binding Macs to Azure Active Directory is twofold:
- No thanks to the Apple-Microsoft rivalry, there is no native integration between Macs and AAD.
- Even when workaround solutions exist, ensuring a seamless user experience can also take time and effort.
For example, some admins have taken a cobbled approach of creating a domain within Azure using the Azure AD Domain Services (AD DS) before setting up a VPN connection between their Macs and the Azure domain. The problem, however, is that this solution is complicated and even discouraged by Microsoft.

Others, which already utilize Active Directory, can choose to implement an on-prem directory extension. However, this presents a new set of challenges, from extra costs to more infrastructure to manage.
In addition, this doesn’t enable direct Mac integration into Azure AD. Instead, admins are left with a non-future-proof method of managing endpoints.
The Solution: Step Out of Platforms And Into Identity
A better approach that IT admins take to resolve this problem is to think away from platforms and into identity.
Rather than relying on a cobbled solution that requires managing multiple directories or on-prem extensions, cloud identity management solutions such as the JumpCloud Directory Platform provide a single-user directory that can manage all users’ access to the network and other applications from one central platform.
This solution enables admins to bind not only Macs but also Windows, Linux, and other devices to Azure Active Directory in an intuitive and hassle-free manner. With JumpCloud, admins can securely manage users’ AAD access, regardless of their device or platform.
Also, IT teams that leverage other cloud-computing platforms, such as Amazon’s AWS, or Google Workspace, needn’t worry about managing different identities.
Users can access every network or resource with a single identity, such as Wi-Fi, VPN, web applications, legacy LDAP application, and on-prem or cloud-based file storage solutions. This configuration creates a true single sign-on (SSO) experience for users, making it more convenient and secure.
Manage Identity with the JumpCloud Directory Platform
JumpCloud provides an all-in-one solution for IT admins to bind Macs to Azure Active Directory without any of the earlier-mentioned problems. It’s an identity provider that delivers secure, cloud-based access services to users regardless of their devices.
The platform streamlines user experiences with SSO while unifying admin tools for mobile device management (MDM), multi-factor authentication (MFA), and compliance controls behind one pane of glass. Want to get a better handle on your heterogeneous environment? Watch our demo video and sign up for a free trial today.





